
*Tgvv is a variant of Stop/DJVU. Source of claim SH can remove it.
Tgvv
Tgvv is a ransomware virus that encrypts different files on the victim’s computers and then demands a ransom to unlock them. If the Tgvv victims fail to pay the ransom on time, they may never manage to access their encrypted information again.
The hackers who stand behind ransomware viruses like Tgvv often set deadlines for the payment and threaten to delete all encrypted data if the user fails to comply with their demands. Since you are reading this, however, you are likely looking for a way to avoid transferring your money to the criminals. That’s why here we will give you an alternative way to handle the infection. Below, you will find a step-by-step removal guide to help you remove Tgvv from your system plus bonus instructions that can be helpful in recovering the files that you can no longer access thanks to the Tgvv encryption. To have maximum use of the guide, we recommend that you read all the information that follows in order to gain more knowledge regarding he type of threat you are faced with.
The Tgvv virus
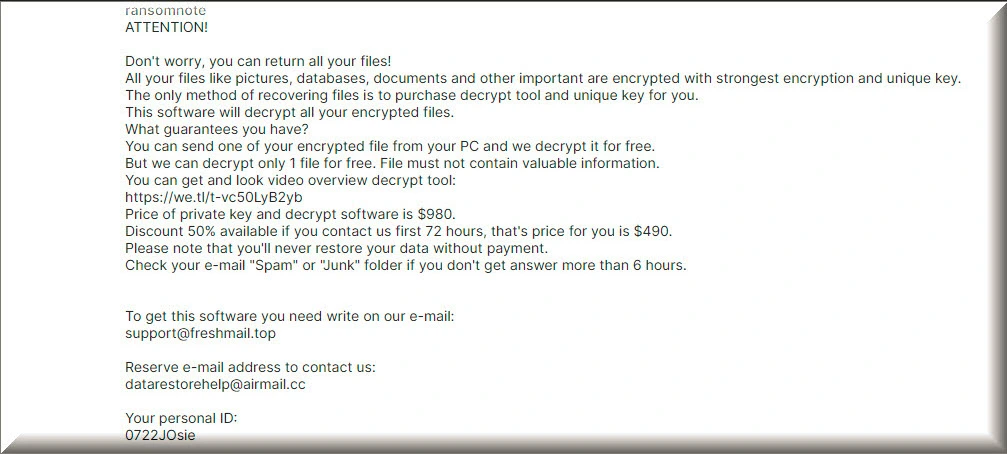
The Tgvv virus is a ransomware virus specialized in encrypting user data and holding it hostage for a ransom. After applying its encryption, the Tgvv virus informs its victims about the steps they need to take to access their data through a ransom-demanding message.
Ransomware viruses such as Tgvv are an incredibly lucrative type of malware. They are used to generate money for their criminal developers through blackmailing and are stealthier than most other computer threats out there.
First and foremost, ransomware like Tgvv and Tghz uses a special crypto-code to restrict the users’ access to their own files. Sadly, the entire encryption process can go unnoticed in the background of the system since most antivirus programs will not see it as a threat. The reason is the file encryption, in general, serves as a means of data protection and is not a process that will damage anything on the computer, including the user files. However, cybercriminals use it for blackmailing by applying encryption to personal files without user permission and refusing to send the corresponding decryption key without a ransom payment.
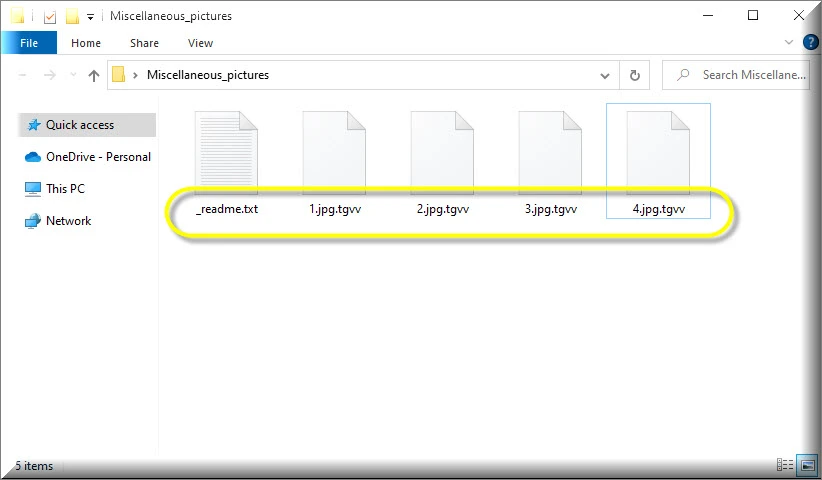
The .Tgvv file encryption
The .Tgvv file encryption is a special code that the hackers behind the ransomware use to keep your files inaccessible. To decode the .Tgvv file encryption, the crooks will ask you to pay a ransom to their cryptowallet.
Once you’ve sent your money to the hackers, however, it’s doubtful if they will really send you a decryption key. Furthermore, the code used for the file encryption is a very complex one, so there is no assurance that your files will be freed from it even if you get a decryption key. Therefore, most security experts, including our “How to remove” team suggest that it should be your first priority to clean your computer and remove Tgvv rather than to send money to some anonymous crooks. Instructions on how to do this are given below and this is also where you will find some free suggestions on how to restore your files from system backups.
SUMMARY:
*Tgvv is a variant of Stop/DJVU. Source of claim SH can remove it.
Tgvv Ransomware Removal

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Tgvv is a variant of Stop/DJVU. Source of claim SH can remove it.
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Type msconfig in the search field and hit enter. A window will pop-up:

Go in Startup —> Uncheck entries that have “Unknown” as Manufacturer.
- Please note that ransomware may even include a fake Manufacturer name to its process. Make sure you check out every process here is legitimate.

*Tgvv is a variant of Stop/DJVU. Source of claim SH can remove it.
Type Regedit in the windows search field and press Enter. Once inside, press CTRL and F together and type the virus’s Name.
Search for the ransomware in your registries and delete the entries. Be extremely careful – you can damage your system if you delete entries not related to the ransomware.
Type each of the following in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete everything in Temp. The rest just check out for anything recently added. Remember to leave us a comment if you run into any trouble!

How to Decrypt Tgvv files
We have a comprehensive (and daily updated) guide on how to decrypt your files. Check it out here.
New Djvu Ransomware
The most recent variant of the Djvu Ransomware family to infect computers is called STOP Djvu Ransomware. This new threat makes it easy for the victims to recognize when they have been infected with it, since it attaches the .Bhui file extension, which is automatically added to the files encrypted by the malware At this time, only files that have been encrypted using an offline key are being decryptable, and if you click on the following link, you will be able to access a decryption tool that may be of use to you:
https://www.emsisoft.com/ransomware-decryption-tools/stop-djvu
Decryption
The process of decrypting can be initiated by downloading the file from the URL provided onto your computer, selecting “Run as Administrator,” and then clicking the Yes button. Prior to proceeding, we kindly ask you to review the license agreement and the concise instructions displayed on the screen.
To commence the decryption procedure, simply choose the Decrypt option within the program. It is important to note that data that has been encrypted using unfamiliar offline keys or online encryption methods may not be decryptable using this tool. If you have any inquiries or concerns, please feel free to share them in the comments section below, and we will make every effort to assist you.
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Reply