Unix.trojan.coinminer ClamAV
Unix.trojan.coinminer is a new and dangerous Trojan Horse virus that can secretly sneak inside your PC and gain elevated privileges in its system without your knowledge or permission. Once Unix.trojan.coinminer embeds itself inside the system, it can launch different harmful processes without getting noticed. The latest iteration of this infection is called unix.trojan.coinminer-9910195-0, but the numeration just identifies a different file as the culprit.
One of the main reasons why PC users get their machines infected by different types of malware is their lack of understanding and awareness with regards to the potential cyber hazards they might face on the Internet. System vulnerabilities are oftentimes used for facilitating the distribution of virus programs but the main tool that the hackers rely on when it comes to spreading their malicious cyber infections is the users’ lack of care and awareness. This is why being well informed with regards to the nature of the potential threats you might face while browsing the World Wide Web is so essential and it is also why we try our best to tell our readers about the latest and most dangerous or problematic forms of malware that they could come across on the Internet.
This makes the Trojan category one of the most commonly encountered types of malware and it’s easy to see why pretty much all computer users have at least heard about them. This, however, is not all – Trojans are also really sneaky and versatile. They can target your data, corrupt your computer system, take control over the processes in the machine, insert more malware programs like nasty ransomware cryptoviruses and rootkits and all of this is barely the tip of the iceberg. If you think that Unix.trojan.coinminer might have sneaked inside your computer, we strongly advise you to carefully look and read the steps from the removal guide below and then apply them on your computer in order to eliminate the insidious threat.
Depending on your specific case, the guide may or may not be enough to resolve everything. In case you’ve completed all of the steps and the malware didn’t entirely go away or in case you don’t think you can finish the whole guide all by yourself, we can offer you an alternative solution in the form of the removal tool from this page. You can find the said tool in the guide and use it in combination with the guide or separately – it should be able to take care of Unix.trojan.coinminer and make your computer safe once again.
The stealth of a Trojan
Threats such as Unix.trojan.coinminer use different kinds of disguise that allow them to sneak inside any system without raising any red flags. Normally, you can expect a Trojan to be hidden inside a pirated program download, inside a fake spam online message or inside some misleading and deceitful online ad or download request. This, however, are only some of the most commonly used methods for Trojan horse distribution. If you really want to stay safe, we also advise you to get a reliable antivirus program which will further boost the protection levels of your PC.
SUMMARY:
| Name | Unix.trojan.coinminer |
| Type | Trojan |
| Detection Tool |
Some threats reinstall themselves if you don’t delete their core files. We recommend downloading SpyHunter to remove harmful programs for you. This may save you hours and ensure you don’t harm your system by deleting the wrong files. |
How to Remove the Unix.trojan.coinminer Virus?
To remove the Unix.trojan.coinminer virus, you must start with finding and deleting the carrier program that brought it to your PC, and then you must clean the system from rogue processes, data, and settings.
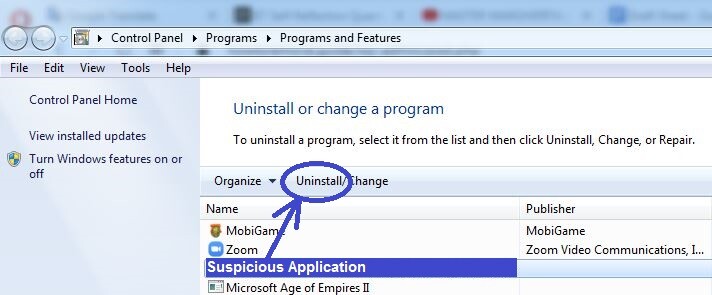
- Search for suspicious/rogue programs in the Uninstall a Program list (found in the Control Panel) and uninstall anything that catches your attention.
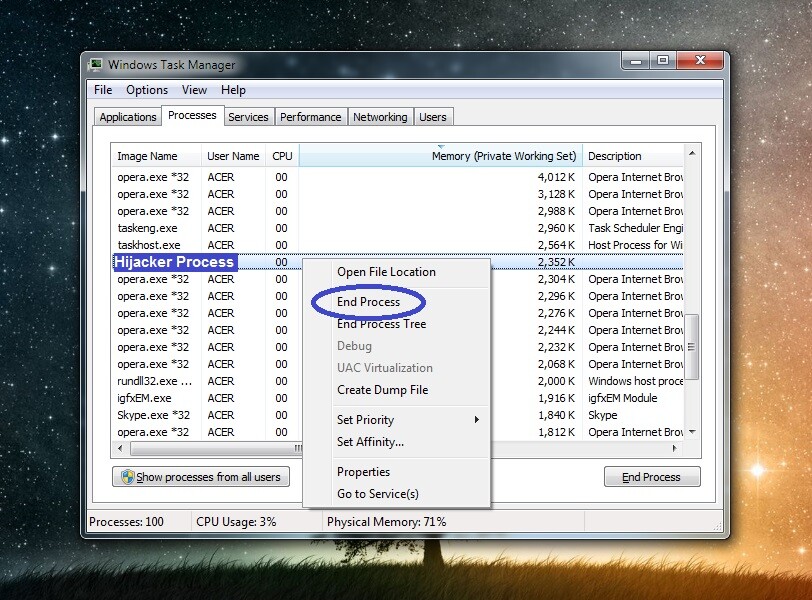
- Open the Task Manager and with its help quit any still running malware processes you may find.
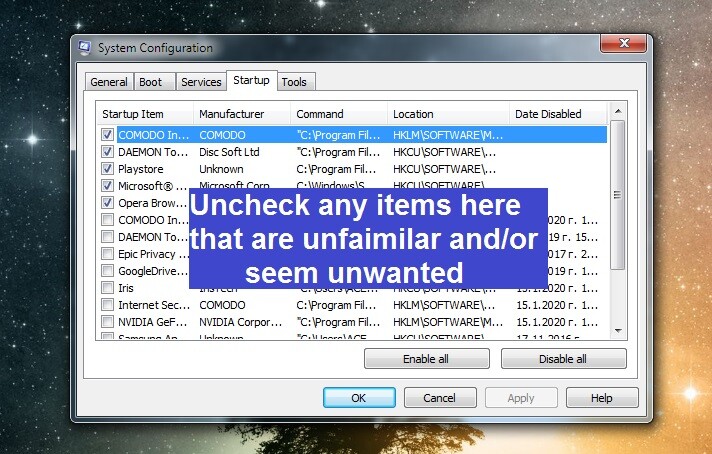
- Access the DNS settings, the list of Startup items, and the Hosts file, and revoke any alterations that may have been made to them by the Trojan.
- Look for remaining rogue files in the system and malware items in the System Registry and delete them to remove Unix.trojan.coinminer for good.
To perform each step correctly, we suggest you read the detailed instructions shown down below.
Detailed Unix.trojan.coinminer Removal Instructions
It’s important to prevent Unix.trojan.coinminer from reaching out to its creators’ servers, and the best way to do this is by disconnecting the PC from the Internet, so be sure to temporarily disable your computer’s Internet connection before starting the guide.
Step 1
Open the Start Menu, search in it for the Control Panel, and open the latter. Then visit the Uninstall a Program section where you must look for any recently added program that looks like it could have infected you with Unix.trojan.coinminer once it got installed on the computer. If you see such a program, select its name, then click the Uninstall button from the top, and perform the uninstallation, making sure to uncheck any options in the uninstallation wizard that may leave data from the program on your computer.
Step 2
WARNING! READ CAREFULLY BEFORE PROCEEDING!
Go to the Task Manager by pressing together Ctrl + Shift + Esc. Open Processes and then search for resource-intensive processes with unusually high virtual memory and CPU usage and that also have questionable names that don’t seem familiar to you. If any such processes are found, try the following two methods to figure out if they are actual malware processes:
On your phone or another device with Internet connection (your PC should currently be disconnected from the web), look up the name of the process you suspect. If that process is truly related to any malware, it’s highly likely that you will find relevant information that confirms your suspicions posted on different security forums and sites.
What you can also do is right-click the process, click Open File Location, and scan what files are in that folder for malware code. We recommend using the free online scanner from below for this task. If it flags any of the scanned files as threats, this would indicate that the process they are related to is also malicious.


You must end any process that turns out to be a threat and also delete the File Location folder where it’s files are contained.
Step 3
It’s important to not let Unix.trojan.coinminer launch any of its malicious processes again – you can make sure this doesn’t happen by booting your computer in Safe Mode, so we recommend this you do that now.
Step 4
Once the computer is put into Safe Mode, click the Start Menu, type ncpa.cpl in its search bar, and click the first shown item in the results. This will bring you to window with one or more networks – right-click on the network you typically connect to, go to its Properties, and there double-click on Internet Protocol Version 4. In the next window, make sure that the options labelled Obtain an IP address automatically and Obtain DNS server address automatically are both enabled, and then go to the Advanced settings. In the Advanced settings window, select DNS, delete anything listed in the DNS server addresses list, and select OK on every window to save the changes.
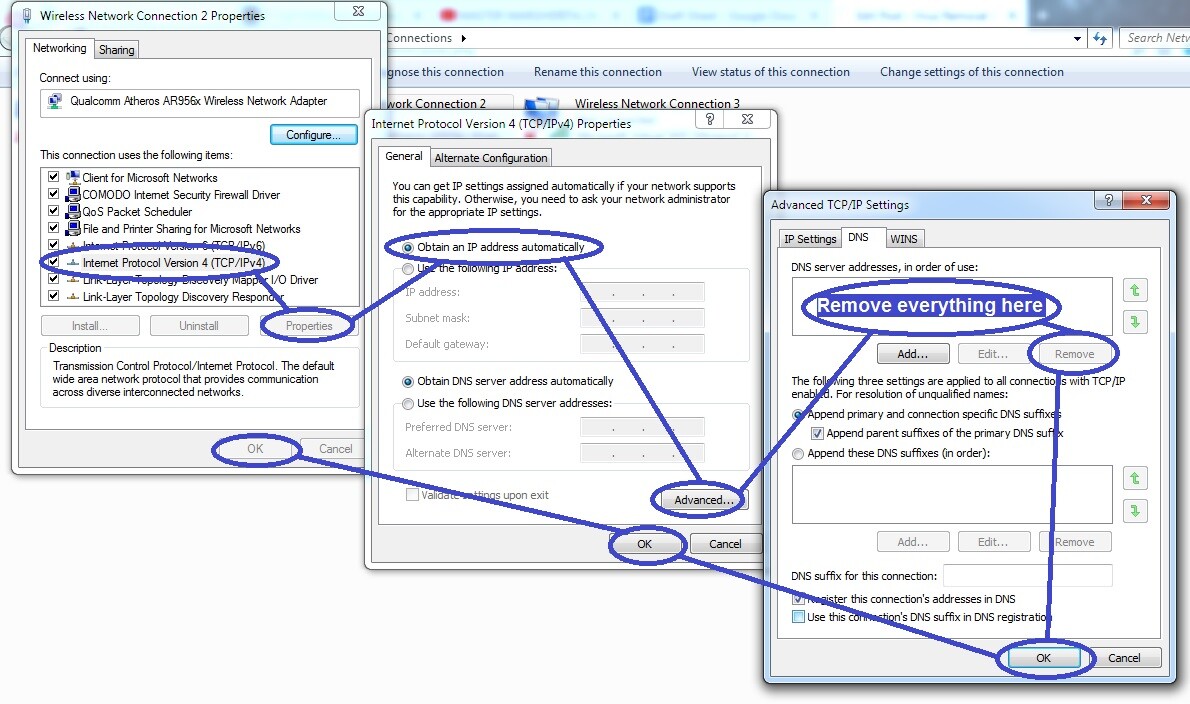
Now go to the Start Menu again, this time type in it msconfig, open the app that shows up, and when you see the System Configuration window on your screen, select Startup and look through the list for items that you don’t recognize or that are shown to have unknown developers. Then uncheck any such items that may be present there and click OK.
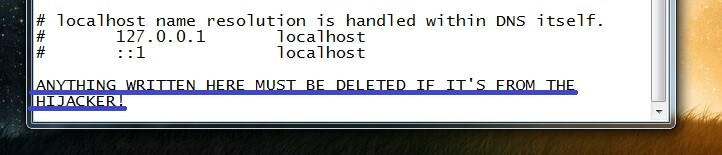
Using the Start Menu search bar again, copy-paste this line in it: notepad %windir%/system32/Drivers/etc/hosts – then select the file that shows up, and when it opens, look at the end of the text and if there you see any IP addresses, send them to us through the comments section below. Once we take a look at them, we will inform you if you must delete them from your Hosts file.
Step 5
Be very careful with this next step because it will require you to delete items from the Registry of your system and if you end up removing the wrong item(s), you could cause further problems for the system. We recommend always consulting us through the comments in case you are unsure about a certain item.
To go to the Registry Editor tool, use the Start Menu search bar to look for its executable named regedit.exe. Once you find it, click on it, and when asked for Admin approval, select Yes. This will open the Editor, and then you must click its Edit menu, then click on Find, type the name of the Trojan in the search bar, and click Find Next. Whatever item gets found, delete it, perform the search again to look for more related items, and delete them too.
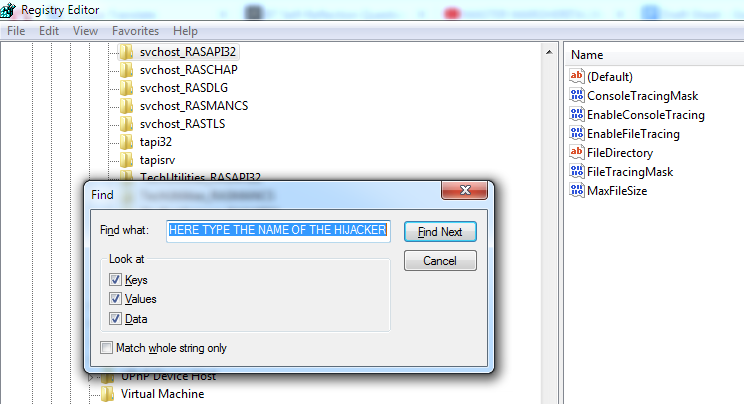
In this way, make sure you’ve deleted everything that is related to Unix.trojan.coinminer from the Registry, and then find and expand the following three Registry locations by using the sidebar to the left.
- HKEY_CURRENT_USER/Software
- HKEY_CURRENT_USER/Software/Microsoft/Windows/CurrentVersion/Run
- HKEY_CURRENT_USER/Software/Microsoft/Internet Explorer/Main
In each of those directories, look for strangely-named items that look like this “0923ru298tu498fj98gty9jd2dj0895ut“, and tell us about them in the comments – we will soon let you know if they must be removed as well.
Step 6
Trojans can sometimes be too difficult to delete manually as they may have entered too deep into the system, which would make finding and deleting all data and settings related to them not feasible without the help of a specialized tool that can do the heavy lifting for you. For this reason, if it seems that Unix.trojan.coinminer is still in your computer even after you’ve completed all steps shown in the guide, it is advisable to try to use a professional anti-malware program that can perform a deep scan of your system, find everything related to the Trojan, and delete it.
We can recommend to you one such tool that can take care of Trojans like Unix.trojan.coinminer, and that we advise our readers to try out if they haven’t managed to manually eliminate the threat. You can find the tool linked throughout the guide above.

Leave a Reply