Vovalex
Vovalex is software created with the intention to restrict access to valuable digital files that are stored on the targeted computer and to demand a ransom from the owners for restoring access to them. Vovalex uses sophisticated encryption to keep the files hostage and displays a ransom note on its victims’ computer in order to inform them about the demanded amount of ransom money.
Sadly, Vovalex is not the only virus that operates in the above-mentioned way – there is a whole group of malicious programs, classified as Ransomware, that attempt to extort money from unsuspecting web users by restricting their access to extremely important and valuable information. Fundamentally, infections such as Vovalex, .Pola, .Waiting are encoding a list of files with a high-end algorithm and is making them unreadable by any application. The victims can open or use the encoded files only after they apply a special decryption key. This decryption key is normally generated by the ransomware itself but instead of being handed over to the data owner, it is stored on the server of the hackers behind the infection.
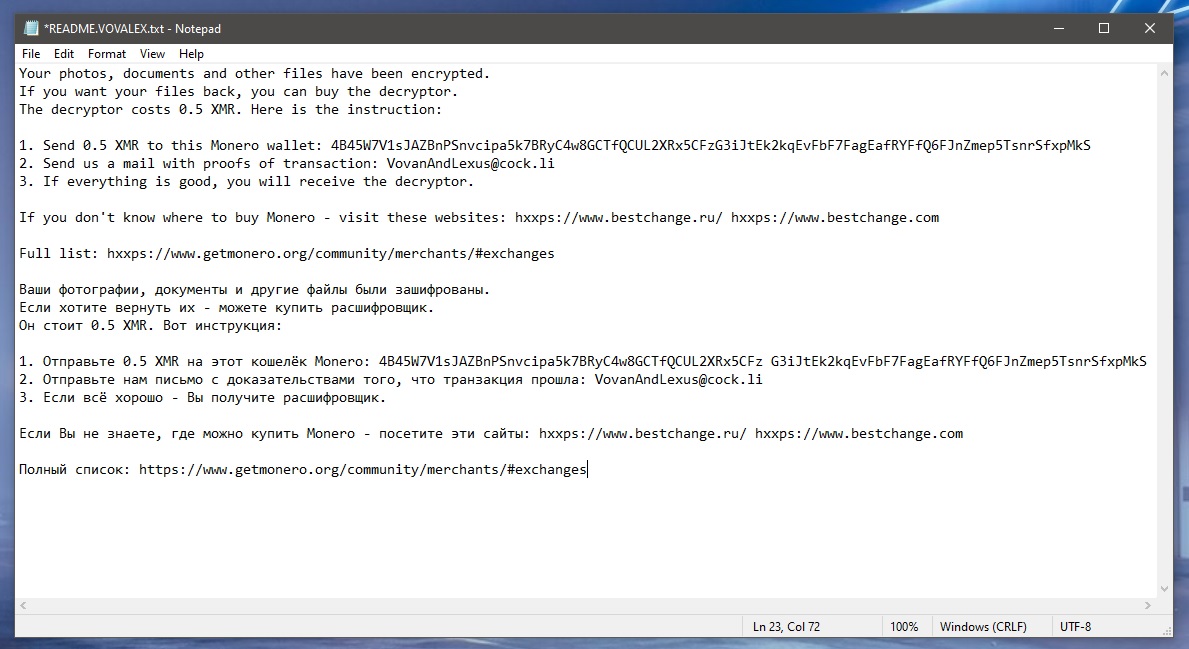
The file encryption process that Vovalex runs inside the infected computer is very stealthy and normally has almost no symptoms that could give it away. This gives the malware the advantage of surprise. When all the target files are locked, however, the malware informs its victims that their data has been encoded by generating a scary ransom message on their screen and threatens them that they cannot open or use it unless they pay for a decryption key.
Unfortunately, the encrypted files may remain inaccessible regardless of your efforts to save them or pay the ransom that the crooks behind Vovalex demand. So, basically, it is very difficult to deal with the effects of the ransomware’s attack and, sometimes, some of the information may be lost for good even after the malicious code has been removed.
The Vovalex Ransomware
The Vovalex is a ransomware threat that can detect and encrypt the files that the users use the most on a given computer. After placing its encryption on them, the Vovalex ransomware can display a ransom-demanding message where it asks the victims to pay a certain amount of money for a decryption key.

The effects of the Vovalex’s attack may not be so serious if the files that it has encrypted can be recovered or are not that important. In that case, all that you have to focus on is how to remove the malicious code and clean your computer. If you really need the encoded information, however, you may have to seek alternative solutions that can help you to deal with the infection in the best possible way and with minimal losses.
Paying the hackers may seem like one of the easiest solutions but, if we have to be honest, nothing can obligate the crooks to help you recover your data as long as they receive from you the money they want. That’s why, in most cases, it is a good idea to explore some free file-recovery alternatives before you risk your money.
The Vovalex file decryption
The Vovalex file decryption is a data-recovery process that, in theory, should return the encrypted data to its previous state. Nevertheless, the successful decryption of the Vovalex file will only be done if the victim applies a working decryption key.
It is not wise to pay a ransom to the hackers for this, though, because chances are that they will vanish with the money and leave you with a bunch of data that is unavailable. That’s why a far wiser approach is to look for legitimate file retrieval alternatives and solutions from security experts that can help you both remove Vovalex from your device and recover some of your data.
SUMMARY:
Remove Vovalex Ransomware
![]()
Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).
![]()
WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.
![]()
Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Type msconfig in the search field and hit enter. A window will pop-up:

Go in Startup —> Uncheck entries that have “Unknown” as Manufacturer.
- Please note that ransomware may even include a fake Manufacturer name to its process. Make sure you check out every process here is legitimate.
![]()
Type Regedit in the windows search field and press Enter. Once inside, press CTRL and F together and type the virus’s Name.
Search for the ransomware in your registries and delete the entries. Be extremely careful – you can damage your system if you delete entries not related to the ransomware.
Type each of the following in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete everything in Temp. The rest just check out for anything recently added. Remember to leave us a comment if you run into any trouble!
![]()
How to Decrypt Vovalex files
We have a comprehensive (and daily updated) guide on how to decrypt your files. Check it out here.
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Reply