White Rabbit
If White Rabbit has contaminated your computer, you are dealing with a ransomware infection. White Rabbit targets all known operating systems and encrypts the files on them.
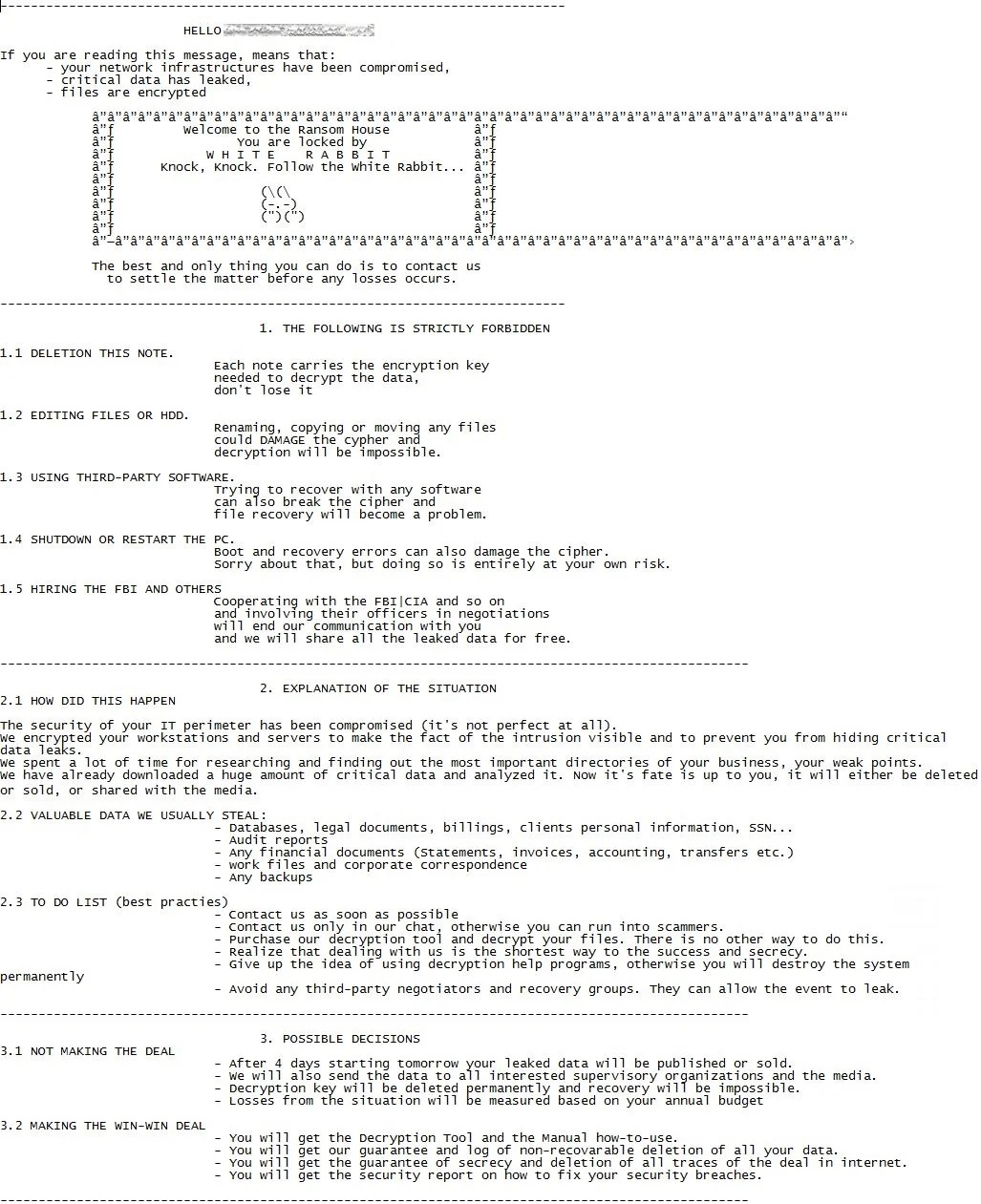
Once this happens, the virus then proceeds to display a ransom note on the screen of the affected PC. As a rule, it informs the victim of the encryption process that has taken place and lets them know that the only way to reverse it is by “purchasing” a decryption key from the hackers. Then there will normally also be payment details and usually also a deadline before which users are required to pay.
Given that you are on this page, you have likely already encountered this highly unpleasant message and are now wondering what you can do to fix this terrible mess. We have created a removal guide specifically for ransomware viruses like White Rabbit, and you can find it just below this article. In addition, we have included some tips on how you can attempt to restore the files encrypted by this virus without having to pay or a decryption key. Keep in mind, however, that there is a chance some of your data may be lost for good.
The White Rabbit virus
The White Rabbit virus uses encryption to lock users out of their very own files. The White Rabbit virus then blackmails its victims into sending money so that they can regain access to the sealed data.
Ransomware is actually part of an ingenious criminal scheme because at this point there is little that can be done to counter an attack like this. The encryption process itself is not a malicious one, and therefore it does not trigger a response from the vast majority of security software out there. And on top of that, the hackers behind ransomware viruses always request their payments be made in different cryptocurrencies. This ensures that they remain anonymous and cannot be tracked by the authorities. And that has, in turn, turned this whole thing into such a lucrative business model.
For this reason, we do not recommend succumbing to the White Rabbit demands and encourage you to explore all other alternative options you have available to you. Not only will paying the ransom amount stimulate the criminals to continue attacking people, but it may also not solve your problem with the encrypted files. There is simply no guarantee that the hackers will in fact send you the needed code or that it will even work successfully.
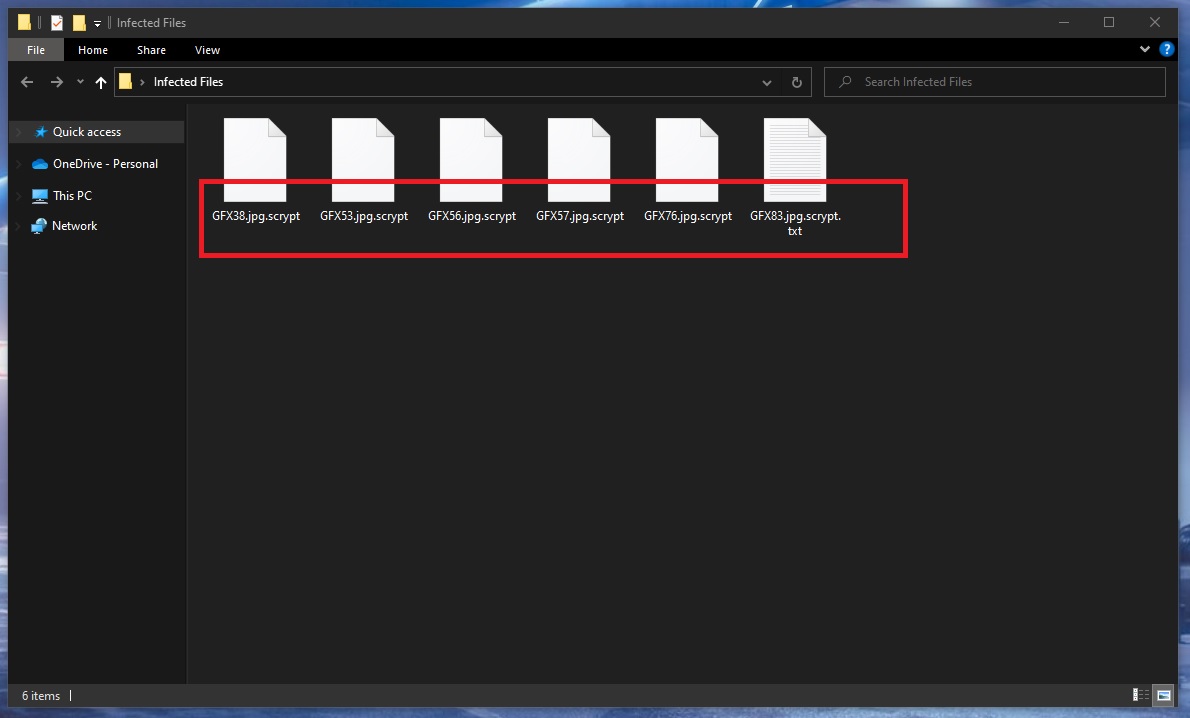
The White Rabbit file extension
The White Rabbit file extension is the telltale sign that a file has been locked by this ransomware. Basically, after a file has been encrypted, the virus changes its extension to the White Rabbit file extension. And if you try to open it, regardless of how many different programs you try to use for this task, you won’t manage.
As far as preventing such infections like Vfgj, Zaqi in the future, we recommend being very cautious with any and all content that you come across online. Be it emails, social media messages, online ads or whatnot – do not interact with anything you aren’t 100% sure is safe.
SUMMARY:
| Name | White Rabbit |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Data Recovery Tool | Not Available |
| Detection Tool |
Remove White Rabbit Ransomware

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Type msconfig in the search field and hit enter. A window will pop-up:

Go in Startup —> Uncheck entries that have “Unknown” as Manufacturer.
- Please note that ransomware may even include a fake Manufacturer name to its process. Make sure you check out every process here is legitimate.

Type Regedit in the windows search field and press Enter. Once inside, press CTRL and F together and type the virus’s Name.
Search for the ransomware in your registries and delete the entries. Be extremely careful – you can damage your system if you delete entries not related to the ransomware.
Type each of the following in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete everything in Temp. The rest just check out for anything recently added. Remember to leave us a comment if you run into any trouble!

How to Decrypt White Rabbit files
We have a comprehensive (and daily updated) guide on how to decrypt your files. Check it out here.
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment