XINOF
XINOF is a representative of the Ransomware virus group that is specialized in locking commonly used user files through encryption. XINOF targets work-related documents, archives, databases, audio and video files, images and other digital data that is stored in the system with the idea to make it unavailable to the owner and demand a ransom for it.
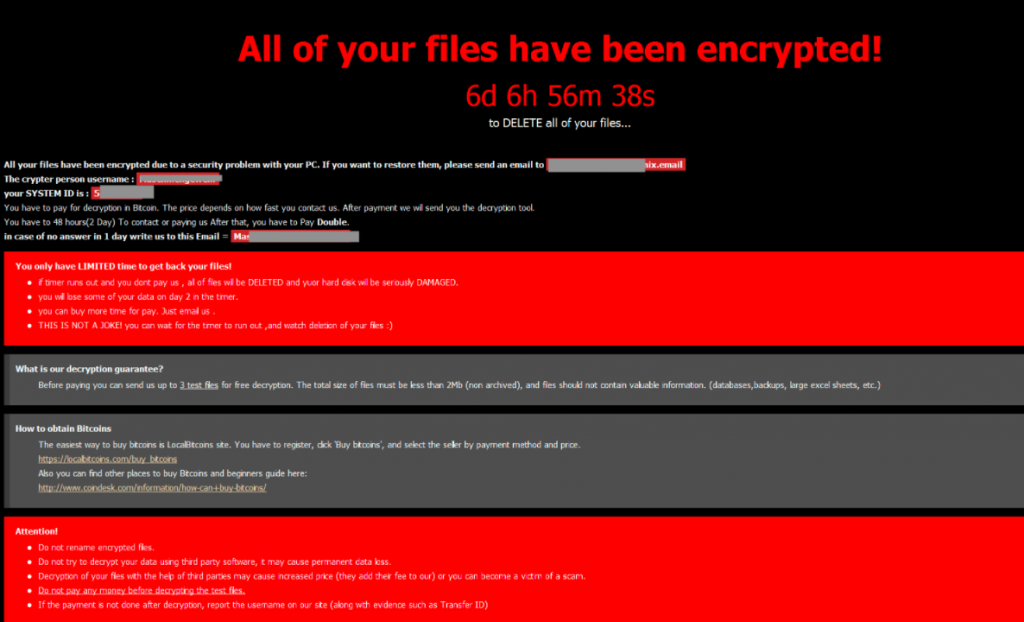
XINOF doesn’t aim to damage or steal the files that it encrypts, but rather keep them locked until the user fulfills the ransom requests of the hacker. Normally, a certain amount of money is demanded from the victim in exchange for providing a decryption key for the encrypted information. A scary warning message appears on the screen of the infected machine after the encryption has been applied. The message typically requires that the victim transfers a certain sum in Bitcoins to the electronic wallet of the hackers. If paid, the blackmailers promise to give a special access key to their victims to re-access the encrypted files.
The XINOF Ransomware
The XINOF ransomware is an online extortionist threat that encodes user files with encryption and uses them as a basis for online blackmail. The XINOF virus notifies its victims about the effects of its attack by placing a ransom message on their screen and gives them a deadline to transfer the money.

Normally, aside from restricting access to the files that you need the most, ransomware viruses like XINOF, .Qlkm or .Omfl doesn’t harm anything on the infected computer. This means that, once you successfully remove the virus, you can use your machine as before. The main problem comes from the fact that if the files that have been encrypted are important to you and you cannot afford to lose them, you may have to seek alternatives to recover them. Sadly, deleting the ransomware will not automatically remove the algorithm that it has applied. A file backup copy can be a real life-saver here but if you don’t have backups to recover your information from, you have to carefully consider the alternatives that may help you minimize the data loss.
The XINOF file decryption
The XINOF file decryption is the main method that the victims of XINOF can use to release their encrypted files. The activation of the XINOF file decryption process, however, requires a special decryption key that is retained by the hackers who want a ransom.
Paying the ransom, however, doesn’t automatically mean that you will receive a decryption key from the hackers. It is highly possible that they trick you just to get your money without providing you with the necessary means for the recovery of your information. At the same time, there might be other options to recover your files, which do not include you contacting the hackers or giving them your money. If you are curious to give them a try, you can check out the second section of our removal guide below. Sadly, XINOF can encrypt any new files that you create or manage to recover. That’s why to prevent that you have to carefully remove it from your computer.
SUMMARY:
| Name | XINOF |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Symptoms | Very few and unnoticeable ones before the ransom notification comes up. |
| Distribution Method | From fake ads and fake system requests to spam emails and contagious web pages. |
| Data Recovery Tool | Not Available |
| Detection Tool |
Some threats reinstall themselves if you don’t delete their core files. We recommend downloading SpyHunter to remove harmful programs for you. This may save you hours and ensure you don’t harm your system by deleting the wrong files. |
XINOF Virus Removal
![]()
Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).
![]()
WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.
![]()
Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Type msconfig in the search field and hit enter. A window will pop-up:

Go in Startup —> Uncheck entries that have “Unknown” as Manufacturer.
- Please note that ransomware may even include a fake Manufacturer name to its process. Make sure you check out every process here is legitimate.
![]()
Type Regedit in the windows search field and press Enter. Once inside, press CTRL and F together and type the virus’s Name.
Search for the ransomware in your registries and delete the entries. Be extremely careful – you can damage your system if you delete entries not related to the ransomware.
Type each of the following in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete everything in Temp. The rest just check out for anything recently added. Remember to leave us a comment if you run into any trouble!
![]()
How to Decrypt XINOF files
We have a comprehensive (and daily updated) guide on how to decrypt your files. Check it out here.
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Reply