.Yjqs
With the help of a new virus called .Yjqs hackers are trying to blackmail web users to give them their money. .Yjqs belongs to the type of malware known as ransomware and is considered one of the nastiest computer threats you may encounter.
It is also much more sophisticated than a regular virus, thus, the problems it can cause can be much more serious. If such a threat infects your machine, it is very likely that you will be blocked from accessing the screen of your device or the data kept on the computer. This is done in order to allow the hackers who control the ransomware to blackmail their victims to pay a ransom if they want to regain the access to their files. They typically display a scary ransom notification and give a short deadline after which they threaten to keep the device or its data locked forever.
Usually, a complex encryption algorithm is applied when a ransomware virus targets the files inside the PC. Dealing with this encryption can be very challenging and now always successful. In the next lines, however, we will offer you some alternative solutions which may help you remove the nasty infection and maybe save your files.
The .Yjqs virus
The .Yjqs virus spreads via different misleading sources such as deceitful links, files or email attachments, legitimate-looking sites, spam and even in a combination with Trojan horse viruses. The contamination with the .Yjqs virus usually happens when users click on such a transmitter and thus unknowingly activate the malware.
.Yjqs follows a specific agenda and targets the files found on the computer. It infiltrates all hard drives and searches for certain file types which later become encrypted with a very complex algorithm. This ransomware is what is known as a cryptovirus and is one of the most commonly used types of ransomware. The main targets of its attack are usually different documents, images, work files, audios, videos, archives and maybe even certain system files that get locked with an encryption and thus become inaccessible to the victim.
A special decryption key, however, is generated on the server of the hackers and with its help, the affected files can get back to normal. The crooks, of course, won’t give that key to you for free. They will ruthlessly blackmail you to pay whatever amount of money they want.
Apart from the file-encrypting type, security experts also identify screen-locking ransomware as well as ransomware for smart devices. These two types do not affect your data and instead place a full-screen ransom note on the screen of your tablet or smartphone and again prevent you from accessing your icons and menus unless you pay a ransom. From all the three categories, however, the file-encrypting ransomware is the most difficult to counteract because releasing the files from the malicious encryption can rarely be guaranteed.
The .Yjqs file
Unfortunately, so far, there is no universal solution that can provide a 100% effective recovery from the .Yjqs file encryption. This makes the .Yjqs file encryption extremely tricky to deal with, mostly because oftentimes losing some of your data is inevitable.
You can, of course, take the risk and give the criminals your money with the hope that they will send you the promised decryption key. Whether this will really happen, however, is anyone’s guess. The crooks may ask for more money, they may send you a key that doesn’t work or simply disappear without sending you anything.
Other alternatives which don’t require your money and you may like to consider include using your own file backups or the backup copies of the system if they are available. For this method, however, you must remove .Yjqs from the computer before you try to connect any backup source. Otherwise, the ransomware may encrypt your backup source as well and really leave you without any data. Contacting a professional is an option as well, but before you do that, we suggest you try the instructions in the removal guide below or use the professional .Yjqs removal tool to scan your computer and remove the hidden ransomware scripts. You can also research different blogs, forums and other alternative methods or decryptor tools which may help you minimize the effects of the attack.
SUMMARY:
| Name | Yjqs |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Detection Tool |
Some threats reinstall themselves if you don’t delete their core files. We recommend downloading SpyHunter to remove harmful programs for you. This may save you hours and ensure you don’t harm your system by deleting the wrong files. |
Before you begin this guide
There are a couple of important things that you must consider before attempting to perform the removal of .Yjqs. First and foremost, if this virus has attacked your PC, you need to immediately disconnect any external devices that have any sort of data stored on them. This includes phones, tablets, flash memory sticks, external drives, etc. If you have anything like that still connected to your PC, unplug it now!
Next, it is a good idea to disconnect the PC from the Internet before you begin the removal steps and access this page from another device and read the instructions from there.
Another thing we must mention is that, even though we always encourage our users to use alternatives to the payment, sometimes you may simply not have another choice and be force to pay the money. If that is your current situation, it may be better to not remove the virus yet, and instead perform the removal steps only after you’ve sent the ransom sum and hopefully received the decryption key.
Last but not least, even though the virus may have deleted itself automatically after encrypting your data, it’s always safer to still perform the steps from our removal guide to make sure that there’s truly no malware left on the computer.
Remove .Yjqs
To remove .Yjqs, you will need to not only delete the rogue program that infected you, but also restore any system settings that may have been changed by the virus.
- See if there’s a recently installed program on your PC that may have caused the Ransomware infection, and uninstall that program.
- Search for malicious processes that may be active on your computer, quit them, and, if possible, delete all of their files.
- See if there are any malware files in the AppData, Temp, LocalApData, ProgramData, and WinDir folders, and delete what rogue data you may find.
- Check for unwanted changes made by the virus to your system’s Startup items list, Task Scheduler, Registry, and Hosts file, and override those changes.
To perform the steps correctly, it’s recommended to read their detailed descriptions that we’ve included in the net lines.
Detailed removal instructions
Step 1
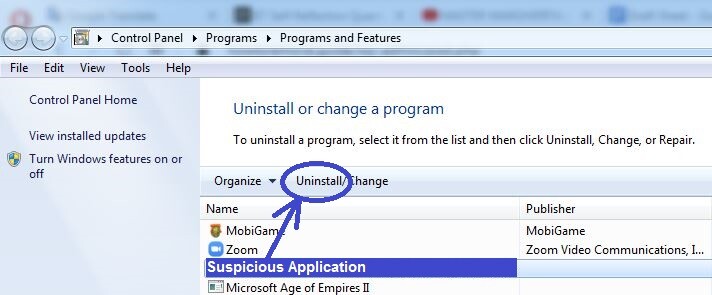
You can see all the programs that are currently on your PC by typing Programs and Features in the Start Menu search bar, and hitting Enter. See what items are shown in the list that appears, and look for anything that has been installed recently and that seems potentially harmful or unwanted. If there is any program that may have injected your system with the Ransomware, click on it, select Uninstall from the top, and perform the uninstallation process. While uninstalling the program, be careful with the settings in the removal manager – be sure to pick the options that would remove everything from that program, including its temporary files and personalized settings.
Step 2
WARNING! READ CAREFULLY BEFORE PROCEEDING!
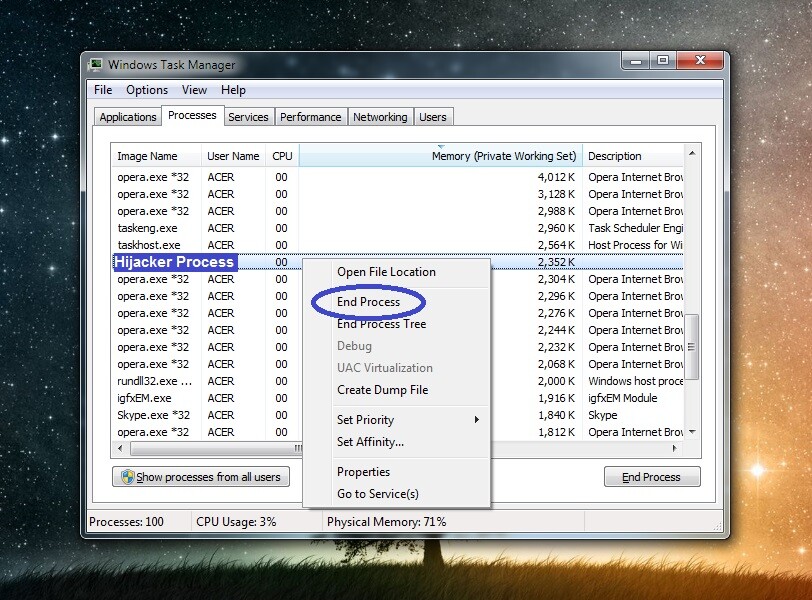
Go to the Start Menu, type Task Manager, and select the first icon that appears in the Start Menu. Now that you are in the Task Manager, click the Processes tab to see the processes that are running in your system at the moment. Search the list of processes for oddly-named entries that use large amounts of CPU and memory and don’t seem related to any of the programs that are presently open on your computer. Look up the names of any such processes and see what results you get. If there are reports on security sites stating that the process you searched for may be malicious, you should probably trust those reports.
Another thing you could do to find out more about the process you suspect of being malicious is to right-click on it, select the first option from the menu (Open file location), and scan the contents of the newly-opened folder with the free malware scanner that you will see right below. If there turns out to be malware among the files of the suspected process, that would mean that the process in question is, too, malicious.


To end a malicious process that you may find in your Task Manager, simply select it and click the End Process option from the bottom-right. After that, remember to go to the directory where the file location folder of that process is located and delete the process’ folder. In case you are not allowed to delete it right now, delete as many of the files in that folder as you can and proceed to the next step. After finishing the guide, try once again to delete the file location folder of the rogue process.
Step 3
The Ransomware on your computer may be able to start its harmful processes once again – to stop this from happening, be sure to restart your computer in Safe Mode.
Step 4
You must now clean several folders on your computer that are likely to contain malware files. First, however, you must make sure that any hidden files that may be stored in them are visible to you. To do this, go to the Start Menu, search in it for Folder Options, and open the first result. Then click the View tab, enable the Show hidden files, folders, and drives option, and select OK.
After that, type %AppData% in the Start Menu, press Enter to open that folder, and sort the files in it by order of the date they’ve been created. Next, delete all files created after .Yjqs attacked you. After that, you must do the same with the %LocalAppData%, %ProgramData%, and %WinDir% folders.
Finally, visit the %Temp% folder, press Ctrl + A to select all files that are in it, then press Del, and click Yes to delete everything in that folder.
Step 5
Search for msconfig in the Start Menu, open the first entry in the search results, and go to Startup. For Windows 10 users, you must select the Open Task Manager option shown in the Startup tab. When you see the list of startup items, disable (deselect) the ones that you don’t recognize or trust and then select OK.
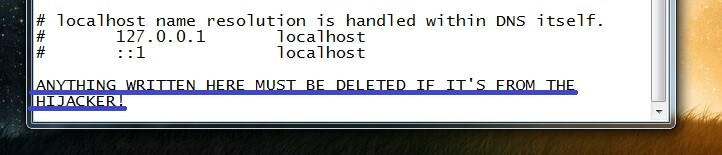
The next thing you must do is go to the Windows\System32\drivers\etc. folder that should be located in your C: drive, double-click on the Hosts file that you should see in that folder, and select Notepad to start it with the notepad app. After you do this, look at the text in the file that shows up on your screen – focus on the end of the text, where there are two lines that end in Localhost. If below those two lines there are any IP addresses listed there, copy those IPs and paste them in the comments section below, so that we can see them. We will soon tell you in a reply to your comment if those IPs are malicious, in which case you’d need to remove them from the file.
Next, search for the Task Scheduler app in the Start Menu, open the app, click Task Scheduler Library (top-left) and then delete any unfamiliar/suspicious tasks shown in the central panel by right-clicking them and selecting the Delete option.

Step 6
Press Winkey + R, type regedit.exe in the Run window, press Enter, and then click Yes when asked whether you are sure you want to allow the Registry Editor app to make system changes. When you are in the Registry Editor, press Ctrl + F, type .Yjqs, and click Find Next to search for related items. Delete whatever item may get found, repeat the search for .Yjqs, and delete the next thing. Do this until all .Yjqs items are gone from the Registry and you are no longer getting any results from this search. After that, repeat the same process with the name of the program you uninstalled in Step 1.
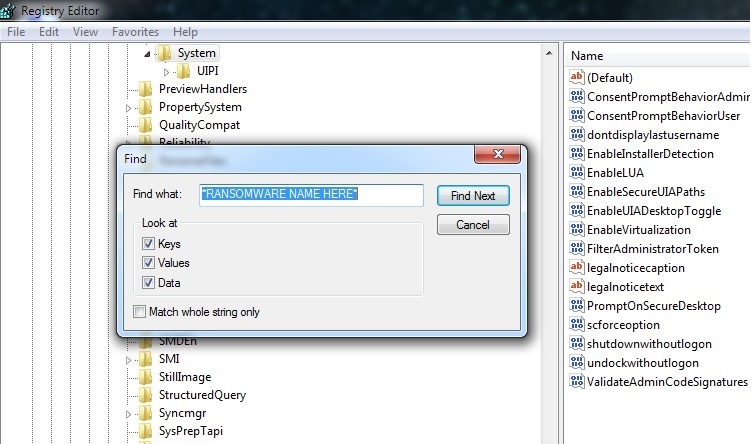
Finally, check the following three Registry Editor folders/keys for any sub-folders/sub-keys that may have unusual names, especially ones that seem randomly-generated (for example, a name like this “309ru3932eu09t2urd0j9u4r0982ru3jd0948uo2t093d2j09tu“). If you come across any such item(s), let us know in the comments section – we will make sure to let you know if this item(s) needs to be erased.
- HKEY_CURRENT_USER > Software
- HKEY_CURRENT_USER > Software > Microsoft > Windows > CurrentVersion > Run
- HKEY_CURRENT_USER > Software > Microsoft > Internet Explorer > Main
If .Yjqs is still in the system
If the virus still seems to be in your system, we recommend deleting it with the help of the professional removal tool that you will find on this page. The reason you may need the help of such a specialized tool is that there may be a secondary threat on the computer (for example, a Trojan or a Rootkit virus) that is blocking your manual attempts to delete .Yjqs. If you use the recommended removal program, however, the tool will delete all malware simultaneously, giving it no chance to remain in the system.
How to Decrypt .Yjqs files
To decrypt .Yjqs files, you must first make sure that the virus has been erased from the computer. After that, you can try some alternative solutions to decrypt .Yjqs files – we strongly advise against paying the demanded ransom unless there’s really no other way.
If you suspect there are any rogue files left on the computer, remember to use the free online scanner we already mentioned above to test them for malicious code and delete them if they are found to be malicious.
Once you’ve cleaned the system from all malware, you are advised to have a look at the instructions show in our How to Decrypt Ransomware article to learn more about the alternative file recovery methods that you can use to try to bring back your data.

Leave a Reply