*Nitz is a variant of Stop/DJVU. Source of claim SH can remove it.
Nitz
Nitz is a virus that is categorized as ransomware. As such, Nitz can encrypt the files on your computer and thus prevent you from opening and/or using them.
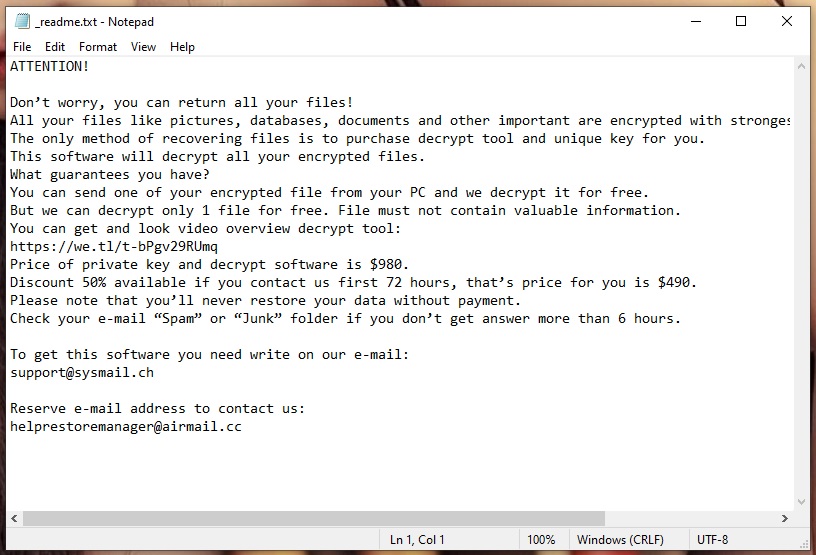
This is particularly unpleasant as the virus can take control of personal files like photos and videos, as well as important work-related files like documents, presentations, etc.
Typically, once Nitz, Niwm or Nifr has finished its encryption, it will display a ransom note on the screen of the affected computer. If you are here due to an infection like this, then you know exactly what the message contains. It informs the victim of the process that has taken place, and provides payment instructions that are to be completed in order to have the files decrypted.
Below is a removal guide that offers a way to circumvent the ransom payment and deal with Nitz accordingly. In addition, we will also describe a few of the existing options you have to restore your files.
The Nitz virus
The Nitz virus belongs to one of the most dangerous malware groups in existence – ransomware. And part of what makes variants like the Nitz virus so harmful is their ability to go undetected by antivirus software.
But before we get into that, let’s first talk about distribution techniques.You may not know where Nitz came from and how it got into your computer. But chances are you clicked on an infected piece of content, such as an email attachment, a link or malicious advertisement etc. Normally, ransomware viruses need a Trojan horse to help them infiltrate your system, so that is likely how you ended up with this particular virus. And that is also why we recommend scanning your system for Trojans with a high-quality malware-removal tool, such as the one we have here.
With the above in mind, we should also underline the importance of maintaining basic safety habits when browsing the web. They are simple to follow and go a long way in keeping your system clean and safe of any potential threats. This includes staying away from unsecure and sketchy web locations, not opening suspicious messages and being careful with the content you interact with.
The Nitz file encryption
This brings us to the Nitz file encryption process which can avoid triggering your antivirus. The Nitz file encryption technique is one that is essentially meant for the protection of files.
Hence, your security software will not view this process as a malicious one and will not do anything to stop it. For this reason, once you’ve been infected with Nitz or other ransomware, there is almost no chance of you detecting it before it’s done. What’s the alternative? With millions of new ransomware threats flooding the internet every year, we cannot stress enough how important it is to keep backups of your files. Whether you choose to store them on a cloud or a separate physical drive, this is the only surefire prevention method against ransomware.
As for the current infection you’re dealing with, please follow the removal guide instructions below to delete Nitz from your computer. In addition, you can try the file recovery steps we offer, although please note that they may or may not be effective in your specific case.
SUMMARY:
*Nitz is a variant of Stop/DJVU. Source of claim SH can remove it.
Remove Nitz Ransomware

The Nitz uninstallation may require several system reboots. For this reason, we suggest that you bookmark this page so that you don’t lose the instructions for removing the ransomware from your browser.
The next step is to follow this link’s instructions and restart your computer in Safe Mode in order to prevent some of the ransomware-related applications from running in the background.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
Read more details in the first ad on this page, EULA, Privacy Policy, and full terms for Free Remover.
*Nitz is a variant of Stop/DJVU. Source of claim SH can remove it.
After you reboot the system in Safe Mode, you need to head to the Task Manager and search for processes that are linked to the ransomware and are running in the background without your knowledge.
To do that, you need to open the Task Manager, (hold down CTRL, SHIFT, and ESC at the same time) and check the Processes Tab to see if there are any processes that might be hazardous or have ties to malicious activities.
Right-click on the process you’re not sure about and select Open File Location to view its files.

Scan these files with a reputable malware scanner, or use the free online virus scanning program provided below:

Once an infected file is discovered, immediately end the processes and remove the infected files.
If you want to know more about a specific process, it’s a good idea to research it online and see if there’s any risk related to it.
![]()
Press Windows Key and R on the keyboard simultaneously. A Run dialog box will pop-up on your screen. Then copy and paste the following and click Enter:
notepad %windir%/system32/Drivers/etc/hosts
You’ll see a new file called Hosts in Notepad. Search your Hosts file under the Localhost section to see if there are any IP addresses that look like those in the picture below:

Let us know in the comments if there’s anything unusual in the file that you’re concerned about. If not, just close it and proceed to the next instructions.
The victims of ransomware may not be aware that Ransomware-related items may have been added to the list of Startup processes. To see whether there are any such entries in your system, launch System Configuration by typing msconfig into the Start menu search field and pressing Enter.

Click the Startup tab and if you feel the infection is connected to any startup items, deactivate them by unchecking their checkmark. Suspicious-looking items often have odd names or an unknown manufacturer, so be on alert for such things. Click OK to save your changes and then close the window.
![]()
Read more details in the first ad on this page, EULA, Privacy Policy, and full terms for Free Remover.
A ransomware infection may typically lead to malicious modifications in your system’s Registry. That’s why, the next thing that you will need to do is search the registry for malicious entries. You’ll need to launch the Registry Editor to complete this step. Using the Start menu search bar, enter “Regedit” and hit Enter.
To save some time and find the ransomware-related entries quickly, you can open a Find box (click CTRL+F together) and write the exact name of the ransomware in it. Then, click on the Find Next button and, if anything is discovered in the Registry with that name, remove it.
Note! If you remove items that are not connected to the ransomware, there is a serious risk of system harm. A reliable malware cleanup program like the one found on this website may help you prevent accidental system damage, so please use it if you are unsure about your Nitz removal actions.
When no more malicious items are identified, close the Registry Editor and go to the Start menu search bar once again. Type each of the following lines into it and open them one by one:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
See if anything new has been added in these locations, that could be connected to Nitz.
Also, please remove all temporary files that may have been left behind by the ransomware by selecting and deleting all the content in the Temp folder.
![]()
How to Decrypt Nitz files
To begin the file recovery process, you’ll need to know precisely what ransomware version you’re dealing with and how to remove it. The extensions that have been added to files that have been encrypted by the ransomware may assist you to distinguish between different variants of the malware.
However, you must first ensure that your computer is free of the ransomware infection. For your own safety, we recommend that you carefully follow the removal instructions from the guide above and then run a system scan with a reliable anti-virus application or an online virus scanner.
New Djvu Ransomware
STOP Djvu, a new ransomware variation from the Djvu Ransomware strain, is currently threatening users across the globe. This new variant is adding the .Nitz suffix on encrypted files which makes it easier for the victims to distinguish it from other versions of the infection.
While new ransomware variants may be incredibly difficult to cope with, STOP Djvu encryption can be deciphered if an offline key was used for encryption. What gives a little more hope is that there is a decryption program that you may use to retrieve your data. In order to get it, just go to this URL and click the “Download” button from the page.
https://www.emsisoft.com/ransomware-decryption-tools/stop-djvu
It’s critical that you run the decryptor that you’ve downloaded as an administrator, and then click “Yes” on the confirmation dialog box when it appears. Next, read the license agreement and the instructions shown on the screen before proceeding further. The Decrypt button can be used to start the decryption process of your information. Consider the fact that the tool may not be able to decrypt data encrypted using unknown offline keys or online encryption.



Leave a Comment