Security researcher Mosh discovered a new version of 7eve3n Ransomware
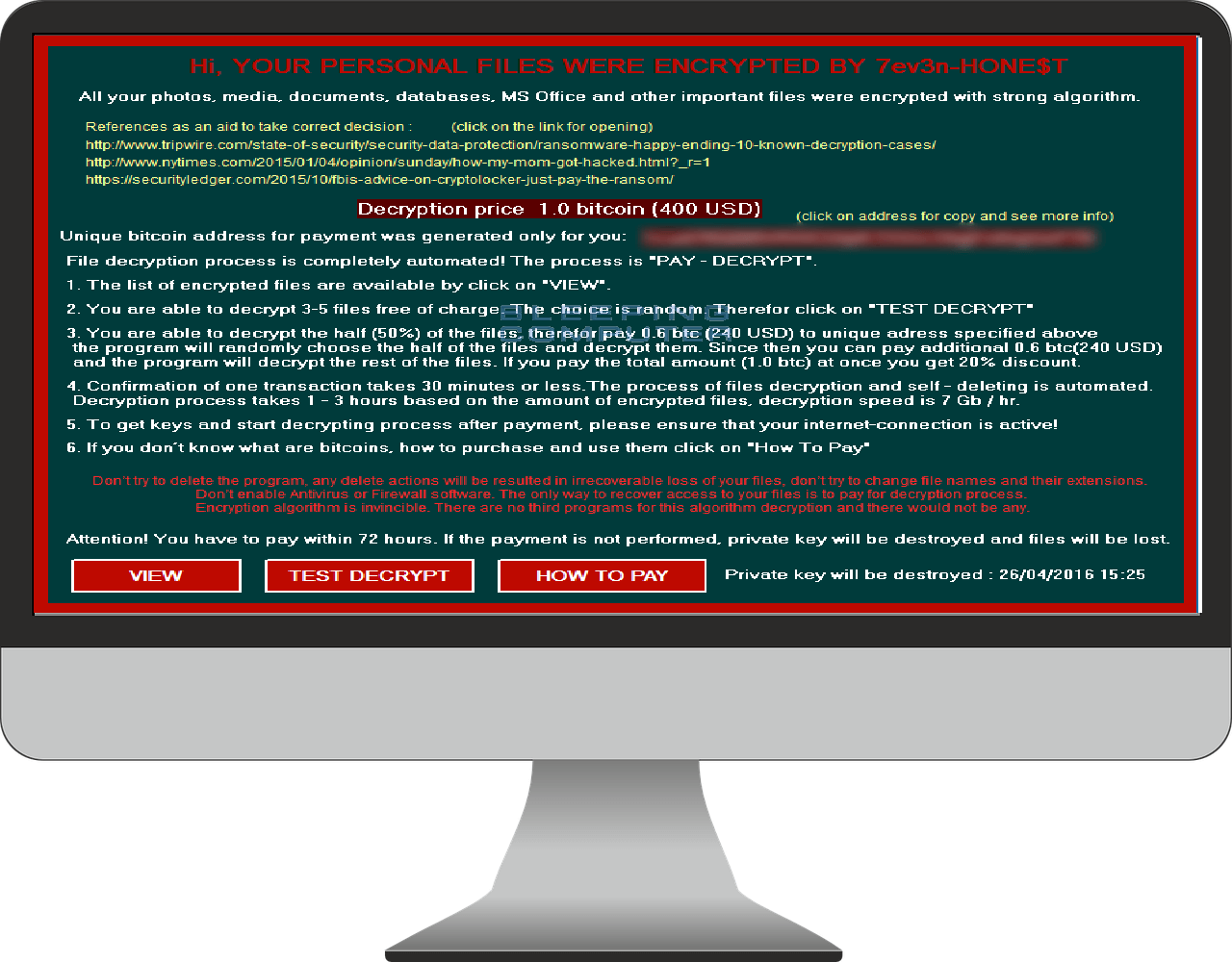
It is still not known how this ransomware distributes itself through the net and what the encryption it applies is. However, what is known is, that it acts like a typical ransomware virus by encrypting the victim’s data and asking for a ransom of about $400 in bitcoins in exchange for the decryption key. The bad news is that security researchers have still not found a way to break the encryption and decrypt the files locked with 7ev3n-HONE$T. Therefore, what victims can do now is either say bye – bye to their encrypted data forever or pay the ransom and remain on the hackers’ mercy to send them the decryption key and hopefully, restore their files.
What’s new in 7ev3n-HONE$T Ransomware?
While encrypting your data, 7ev3n-HONE$T renames your files to sequential numbers and changes the files extension to .R5A. The renamed files most probably would look something like this: 1.R5A, 2.R5A, 3.R5A, etc.
When all your files are encrypted, this ransomware connects to the Command & Control server and uploads different types of information and statistics. This information contains your assigned bitcoin address, the number of files encrypted, and your unique ID. According to the researcher Mosh, the Command & Control server is located in Turkey, Istanbul with the following IP address – 46.45.169.106. When 7ev3n-HONE$T is done with the encryptions, it would place its installation and description files in the C:\Users\Public folder. There, users can find the ransomware executable file, a full list of the encrypted files, a .txt file with instructions how to contact the ransomware developer with the payment, a list of files that can be test decrypted for free and the timestamp of when all your files were encrypted.
Unfortunately, at this moment, there is still no way to break the 7ev3n-HONE$T encryption. Security researchers are working on the possible solutions to deal with this ransomware. At this time, our “How to remove” team would advise users to stick to the online safety rules and ensure they are having a safe surfing while avoiding sketchy content and suspicious files interaction.
Our virus removal experts would follow up with updates on this topic on our website and notify users about any changes. To make sure you are timely informed about new threats and hot news in the digital world, you can follow HowToRemove.Guide on Facebook, Google+, YouTube or Twitter and stay tuned for security tips, tricks, and notifications.

Leave a Comment