8base
8base is among the latest ransomware viruses to be released onto the public and it’s been spreading like wildfire. 8base is extremely dangerous and can cause immeasurable damage to individuals and even businesses and organizations.
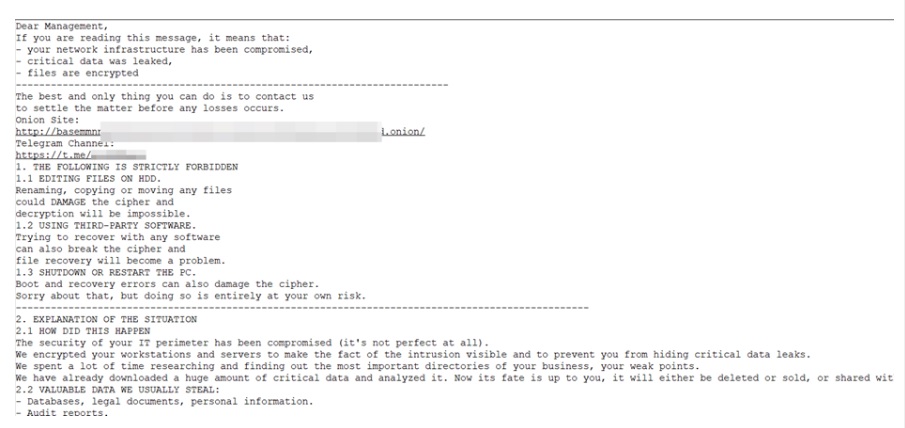
Specifically, 8base fall into the file-encrypting subcategory of the ransomware kind, which makes it the worst type of ransomware you can land. And the reason why it’s so devastating to users is because of what it targets – your data. Once 8base makes its way into your PC, it will scan it for specific file types which it will then proceed to encrypt. So, in other words, it will lock you out of your very own data and prevent you from accessing it, unless a special decryption key is applied. This decryption key is in the possession of the cybercriminals behind the virus, and for it they demand they be paid a certain amount of money in ransom.
Now, right now you have two options. You can comply with the hackers’ demands and pay them whatever amount they’ve requested from you. Or you can try and handle the situation using alternative means and try and recover your files through system backups or other solutions. If you choose the latter, below is a removal guide that will help you locate and remove 8base from your system – a very vital step. And after that, in the second part of the guide you will find suggestions as to what you can do to try and recover your data by other means.
The 8base Ransomware
The 8base ransomware usually acts in complete stealth and easily avoids detection from users, and even from professional antivirus software. The encryption used by the 8base ransomware allows it to go unnoticed, as it is not itself a malicious process.
The above is one of the main advantages that ransomware exploits heavily and what has made it among the most lucrative cybercriminal schemes to date. But aiding this factor is also that of the ransom payment. It may have made an impression on you already, but the hackers behind viruses like 8base, Vaze, Vapo typically demand they be paid in Bitcoin or some other cryptocurrency. And this, in turn, is a safety guarantee for them and their anonymity. In other words, because of this, they can be sure that the respective authorities will be powerless to trace them and they’ll be able to get away with their extortion scheme.
This is another reason that we generally don’t recommend opting for the ransom payment. It’s bad enough that you’ll be losing your money on something that should already rightfully be yours, but on top of that it would go to sponsor the unscrupulous criminals that created this virus.
8base file extension
The 8base file extension is added to the name of each and every one of the encrypted files, replacing their original extensions. This means that now the 8base file extension answers to their format, which is a non-existing one and can therefore not be recognized by other software.
SUMMARY:
| Name | 8base |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Symptoms | Very few and unnoticeable ones before the ransom notification comes up. |
| Distribution Method | From fake ads and fake system requests to spam emails and contagious web pages. |
| Data Recovery Tool | Not Available |
| Detection Tool |
Remove 8base Ransomware

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Type msconfig in the search field and hit enter. A window will pop-up:

Go in Startup —> Uncheck entries that have “Unknown” as Manufacturer.
- Please note that ransomware may even include a fake Manufacturer name to its process. Make sure you check out every process here is legitimate.

Type Regedit in the windows search field and press Enter. Once inside, press CTRL and F together and type the virus’s Name.
Search for the ransomware in your registries and delete the entries. Be extremely careful – you can damage your system if you delete entries not related to the ransomware.
Type each of the following in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete everything in Temp. The rest just check out for anything recently added. Remember to leave us a comment if you run into any trouble!

How to Decrypt 8base files
We have a comprehensive (and daily updated) guide on how to decrypt your files. Check it out here.
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment