Agpo may expose your browser to redirects, ads, and persistent unwanted components. Install SpyHunter Pro to scan for risks, remove related threats, and enable real-time protection.
*Source of claim SH can remove it. Trial w/Credit card; image is for illustration; full terms.
*Agpo is a variant of Stop/DJVU. Source of claim SH can remove it.
Agpo
Agpo is a file-attacking cyber threat used by criminal hackers for blackmailing purposes. Agpo will block your files and force you to pay a ransom to the hackers if you wish to be able to once again open, use, or edit the blocked data.
When discussing malware infections, it can be said that a very large percentage of them are caused by representatives of the Trojan Horse malware family. Despite that, the most horrifying infections the cyber world has ever witnessed haven’t been a result of the activities of those viruses but of the members of another malicious category – Ransomware.
This is exactly the reason behind the article published below – to help you better understand the features and consequences of a certain Ransomware that goes under the name of Agpo. Here, you can find some advice on how to cope with this incredibly malicious contamination in a wise and effective way.
Generally speaking, Agpo and Agvv are representatives of the famous file-encrypting Ransomware subgroup. Its members are capable of sneaking into your device without you noticing anything and after that locking up the personal data which has been stored on your computer machine. Later on, the procedure continues with a message to let you know the scammers behind this malware expect you to pay a ransom for the safe decryption of the affected files.
The Agpo virus
The Agpo virus is one of the sneakiest and most difficult to stop Ransomware threats and it will lock all valuable data on your computer and keep it that way even after it is removed. The Agpo virus uses military-grade encryption algorithm to achieve its goals.
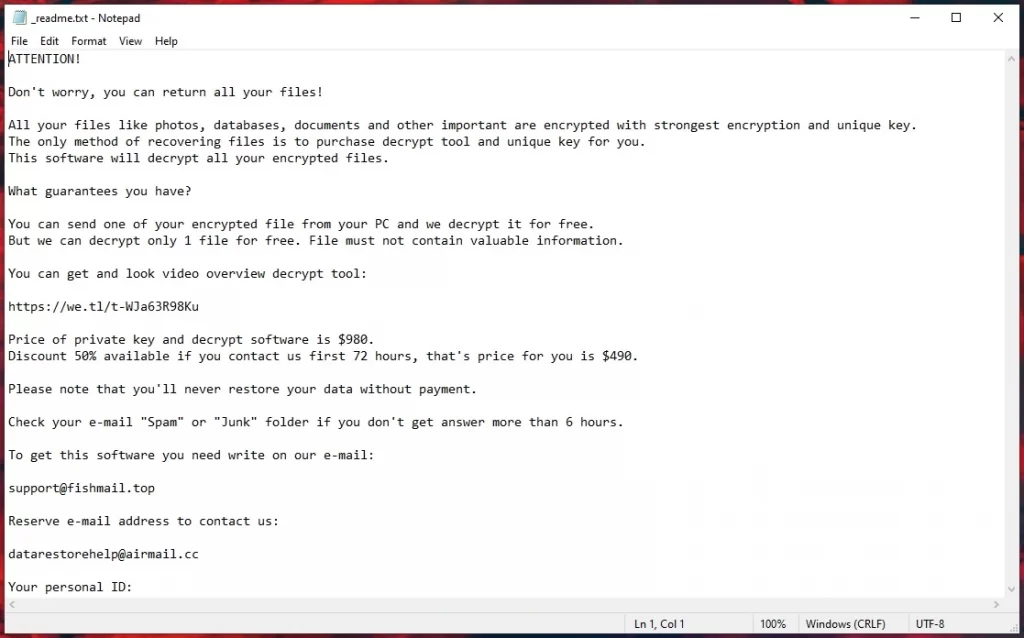
This standard virus kind typically performs a file-encoding process, which takes place right after the program has already selected the file formats that are most likely to be valuable for the user. After all targeted files have been encrypted and rendered inaccessible by Agpo, the user receives a note that states a ransom needs to be paid by the victim for the retrieval of the sealed files.
This process, of course, takes some time, so logically there are cases it has been noticed while it was undergoing. But don’t get your hopes up too much – that happens rarely. Nevertheless, in case you see an odd process going on in your Task Manager, we suggest you turn off your device, and head to a professional for assistance. It may be a Ransomware trying to lock up some essential files.
As soon as the entire encryption process ends, the situation is almost out of our control. Unfortunately, the data-encoding viruses are awfully difficult to counteract. We must point out that even the experts in these fields could find it very complicated to eliminate such a virus without paying off the demanded ransom, let alone restore the victim files. In fact, your chances of success in facing Agpo aren’t exactly high, we aren’t going to lie to you about that.
The .Agpo file decryption
The .Agpo file decryption is the preferable way to restore your files as it is the only one that can ensure full data recovery. However, without the private key, the .Agpo file decryption may not be an option so you may need to look for alternatives to recover at least some of your files.
We hope we didn’t discourage you too much because it will still be helpful to make an attempt to remove this contamination. Always look for different options – leave paying the requested money to the scammers bothering you as a last resort alternative. One way you can potentially handle this issue is trying out the Removal Guide for Agpo posted below – it might help you eliminate the malware and maybe even restore some of the data it has locked.
Where Ransomware could be found:
There are different means of spreading these horrible viruses, such as:
- The attachments of the emails you get daily: Particular emails – especially the ones coming from unfamiliar sources, may be transferring Ransomware. The attachments are actually what is contagious. We advise you to avoid all the letters from strange senders, and their attachments in particular;
- Malicious pop-ups and banners (malvertising): A standard source of Ransomware is malvertising ads. In this case, your device automatically catches some malware right after you click on the contaminated ad – whether intentional or unintentional;
- Fake update requests: Another possible Ransomware source could be various forms of fake and misleading online update requests: the ones not provided by your operating system, but functioning in the same way as the aforementioned ads. The bad news is they are oftentimes difficult to discern between them and actual legitimate update requests. In order to avoid dangers such as Agpo, make sure to update your device manually and look for updates yourself.
Some more tips:
- Once you receive the notification – don’t make any rash decisions and don’t directly send your money. There could be other, better solutions. Your data is already in danger – do not risk your money too.
- Avoid all probable sources of this awful software – simple as that. Make an attempt to stay away from them and eventually it will become a habit.
SUMMARY:
*Agpo is a variant of Stop/DJVU. Source of claim SH can remove it.
Remove Agpo Ransomware

Rebooting your system in Safe Mode is required for the completion of this guide. This will also prevent Agpo from running any malicious processes. Please follow the instructions on the link to restart in Safe Mode and then return to this page for the rest of the instructions.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
Read more details in the first ad on this page, EULA, Privacy Policy, and full terms for Free Remover.
*Agpo is a variant of Stop/DJVU. Source of claim SH can remove it.
All Ransomware processes and their associated folders must be removed using the Task Manager. Press Ctrl + Shift + Esc at the same time and then click on the Processes tab. Processes with unusual names or those that consume with a lot of CPU and Memory usage should be investigated further. Do a Google search to discover if there are any complaints about any of these entries being dangerous. Next, right-click and access the folders associated with the processes you want to monitor (Open File Location).

Scan all files in those directories with the free scanner below. If the scanner determines that one or more of the files in a process’s folder are hazardous, you should end that process as soon as possible.

To do that, go to the Task Manager, right-click on the suspicious process and select End Process. Remove the files associated with that process from the system after that.

Next, you can open a Run dialog box by pressing the Start key and R together on your keyboard. In it, copy and paste the following and then press OK:
notepad %windir%/system32/Drivers/etc/hosts
The Hosts file will be opened in Notepad as a result of this action. Look at the IPs listed under Localhost to check if there are any strange ones. If you come across anything that you find suspicious, please copy and paste it in the comments section. We’ll inform you what to do in the event of a threat.

Enter msconfig in the Start Menu search field, press Enter to launch the System Configuration window, then check to see which startup items are activated on your computer.

Turn off anything you don’t recognize or that doesn’t seem trustworthy, then click OK to save your settings.

Read more details in the first ad on this page, EULA, Privacy Policy, and full terms for Free Remover.
*Agpo is a variant of Stop/DJVU. Source of claim SH can remove it.
Start the fourth step by typing regedit.exe in the Start Menu search box. Windows will ask your permission before starting the application. To proceed, simply click Yes.
After that, click Edit at the top of the Registry Editor window, then click Find, type Agpo in the search field that opens, then click Find Next again to start searching. Remove the found entry from your computer. It is also important to remove any other items that are linked to Agpo from the search results. This search may have to continue until all traces of Agpo are eradicated from your system.
Type “Folder Explorer Options” into the Start Menu search field, then enter the Folder Options settings and choose the View option. Tick the box next to Show hidden files, folders, and drives. Then go to the Windows search field, carefully type each of the following locations one by one and hit Enter to open them:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
You can then sort the content of the newly opened folders by their dates of creation. Remove anything that was added to the system at the time of the Ransomware attack. Additionally, you can erase all of the files in the Temp folder by selecting them all and deleting them. To speed things up, simply use Ctrl + A to select all Temp files, then press Del to delete them.

How to Decrypt Agpo files
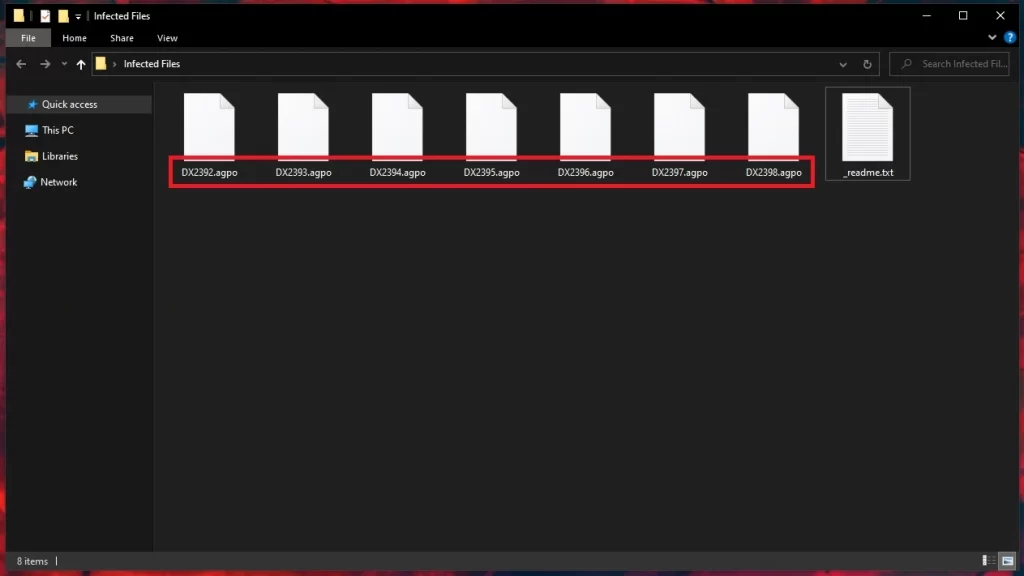
Encryption placed by ransomware threats can be difficult to remove for even the most experienced users. Some file recovery programs, on the other hand, may be able to decrypt encrypted data. If you want to be successful in this task, you first need to know what variant of Ransomware you’re dealing with. To get this information, look at the end of the encrypted files and their file extensions.
A new Djvu Ransomware
STOP Djvu Ransomware is the most recent Djvu ransomware variant that you may encounter. The .Agpo suffix added to the encrypted files separates this specific threat from others, so take a look at the end of your encrypted files to find out if you have been attacked by this variant.
The encouraging news is that the decryption tool found in the URL below may help you recover data encoded by this specific ransomware variant. You can download it by clicking the link.
https://www.emsisoft.com/ransomware-decryption-tools/stop-djvu
Decryption
Start the decryption program by running it as an administrator. Before you begin, please read the included instructions and the license agreement. After pressing the Decrypt button, the decryption procedure should begin.
Please keep in mind that if you try to decode files encrypted with unknown offline keys or online encryption, using this program may fail to recover them. Please feel free to submit any questions or concerns in the comments section below.
Important! Make a full search for ransomware-related files and dangerous registry entries before attempting to restore encrypted data. In some cases, despite your best efforts, you may be unable to manually remove Agpo from your computer because of a Trojan or Rootkit. So, if you’re still having problems with Agpo, we’ve included a link to a professional removal application and a free online virus scanner in this guide, and we strongly recommend that you use it to eliminate all traces of the infection and any other hidden malware.



Leave a Reply