Agvv may expose your browser to redirects, ads, and persistent unwanted components. Install SpyHunter Pro to scan for risks, remove related threats, and enable real-time protection.
*Source of claim SH can remove it. Trial w/Credit card; image is for illustration; full terms.
*Agvv is a variant of Stop/DJVU. Source of claim SH can remove it.
Agvv
Agvv is an extortion malware tool from the Ransomware file-encrypting type. Through the use of an advanced encryption algorithm, Agvv is able to make you unable to open your files, thus forcing you to pay a ransom for the corresponding decryption key.
Agvv Ransomware is one of the latest Ransomware infections which circulates around the web. The reason you are now on this page is probably because you have had the misfortune of having your files encrypted by its secret algorithm. If this is the case and you are wondering what to do, in the next lines, you will find instructions on how to detect and remove the malware from your system in order to make your PC safe again as well as some suggestions on how to recover some of the encrypted files. Keep in mind that there is no guarantee that all of your files will be returned, however, we advise you to try our methods below before proceeding to more radical measures.
The Agvv virus
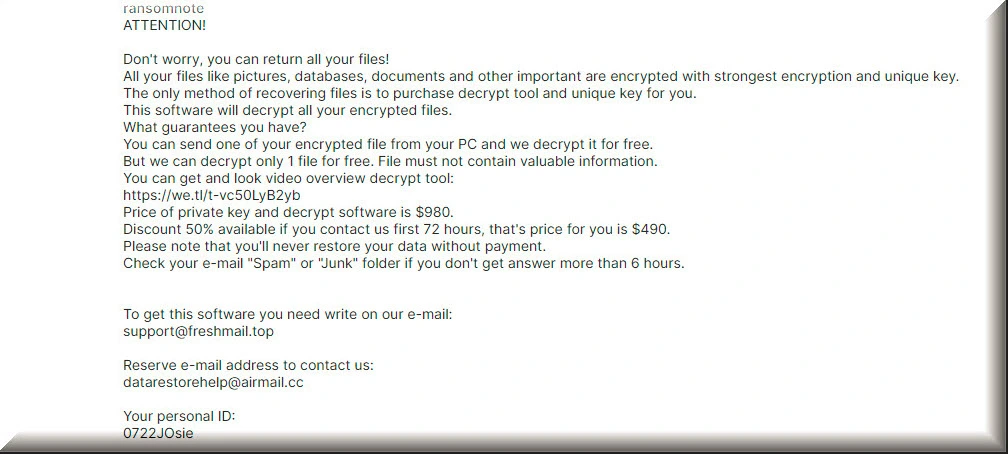
The Agvv virus is a new Ransomware file-encrypting threat that can silently place encryption on all data files present on your PC. The Agvv virus will then display a message on your screen, where are told that your only way of recovering the locked data is through the payment of a ransom.
Agvv Ransomware is a typical representative of the Ransomware family which can secretly infect the victim’s system and encode the most valuable files in it. Upon completion of the file-encryption process, the virus places on the infected machine’s desktop a notification regarding what has just happened to your personal files. Inside this notification, you are given an ultimatum – either you pay a ransom to the hackers and they allow you to regain the access to the sealed files or you lose the access to your data forever.
The most likely distribution methods used by Ransomware threats like this one and Tgpo, Tgvv or Tghz are fake malicious advertisements which usually appear like completely ordinary-looking and harmless online ads, banners or pop-up messages. Another very common method of infecting unsuspecting users is different kinds and forms of online spam. There are still many people who tend to fall for this very old and well-known malware distribution technique. In most cases, the malware is included in the spam message under the guise of some seemingly harmless attachment file. In other instances, it is a Trojan virus that has already entered the PC that allows the Ransomware to get automatically activated in the targeted machine and then encrypt the files. The encoding process typically begins immediately after the cryptovirus enters the computer.
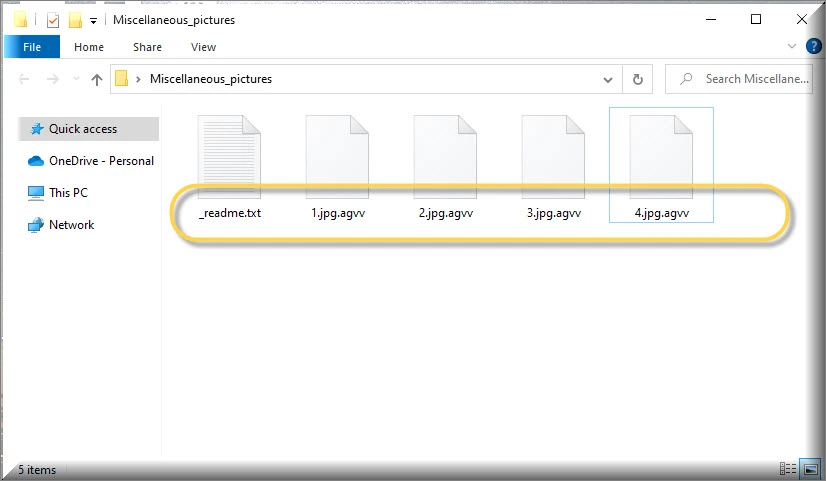
The .Agvv file
The .Agvv file is any personal user file that has been encrypted by the advanced algorithm used by this virus. The .Agvv file has a file extension that is unique for this Ransomware and no regular program can recognize it, which results in the file being inaccessible.
Despite the fact that it is extremely rare for the Ransomware victims to spot the infection on time, before the encryption has been fully completed, it may still happen in some cases. This is because the file-encrypting process, especially if you have many files and your processor is not one of the most powerful, requires a large amount of system resources and also some time to complete. Therefore, in some cases, this can lead to a significant slowdown of the computer, which can and should make you suspicious. However, in most of the cases, there are no particular symptoms, which is why a lot of victims get caught by surprise and tend to get panicked.
Pay or not pay the ransom?
If you ask us, we do not believe that immediately paying some anonymous crooks a certain amount of money is the best way to approach this problem. And while the decision is entirely yours, we need to warn you that fulfilling the ransom demands of the hackers may still not make your computer safe for use in the future and does not guarantee the full recovery of your data. If you remove the Ransomware, however, you will clean your PC and may have a chance to use your file backups safely or try some alternative ways of restoring your data which do not involve the payment of a ransom requested by anonymous Internet crooks.
SUMMARY:
*Agvv is a variant of Stop/DJVU. Source of claim SH can remove it.
Remove Agvv Ransomware

The first step of this guide explains how to restart the compromised computer in Safe Mode. If you do this, the removal of the virus from your system may be much easier, which is why we recommend that you begin by clicking on the Safe Mode link and following the steps there.
Before doing that, however, please save this page in your browser’s bookmarks, so you don’t have to seek for Agvv removal instructions again when you restart your computer.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
Read more details in the first ad on this page, EULA, Privacy Policy, and full terms for Free Remover.
*Agvv is a variant of Stop/DJVU. Source of claim SH can remove it.
Agvv is a form of ransomware that is difficult to detect because of its stealth. This threat may go undetected for lengthy periods of time, and it might inflict significant harm to the system.
When this ransomware infects your computer, detecting and ending its malicious operations will be one of the most challenging tasks you’ll have to face. We recommend that you carefully follow the steps below to protect the safety of your computer.
Press CTRL+SHIFT+ESC on your computer’s keypad at the same time. Then, search for processes that seem to be related to the danger. Windows Task Manager’s Processes tab is where you’ll see this information.
You can check suspicious processes by right-clicking on them and selecting “Open File Location” from the fast menu.

In order to check that the files linked with this process are clear of any potentially harmful code, you may use the free online scanning tool provided below.

If the scanner detects a risk in any of the scanned files, the right-click menu can be used to end the associated process first. Afterwards, go back to the harmful files and remove them from where they were located.
![]()
As a next step, we’ll show you how to remove any malicious startup items from your PC.
Type msconfig in the Windows search field to find System Configuration. Go to the Startup tab and have a look at the startup items listed there:

What you should be doing here is unchecking any startup items that seem to be related with the ransomware. Keep an eye out for any startup components that aren’t associated with the applications that normally execute when the system boots up. If you uncover enough evidence to support their deactivation, uncheck their checkboxes. However, make sure you don’t disable any operating system or trusted software components.
![]()
Read more details in the first ad on this page, EULA, Privacy Policy, and full terms for Free Remover.
In the fourth step of this guide, you’ll have to delete any harmful registry entries found in your registry editor in order to completely remove the ransomware and ensure that it does not resurface or leave any hazardous components behind.
Use the Windows search field to search for the Registry Editor and press Enter to launch it. You may use the CTRL and F keyboard shortcuts to search for ransomware-related files in the Registry Editor, then click Find Next to find them. You can remove a dangerous entry by right-clicking on it.
Attention! Remove only the registry entries associated with the ransomware. Your system and installed programs might be at danger if you make other modifications to the registry or delete other unrelated to the threat components and entries. In case of confusion, please note that this article provides a link to an expert malware cleanup tool that can help you remove Agvv and other viruses from your computer.
When you’re done, close the Registry Editor and check the locations below for any other potentially harmful files and subfolders. Each one may be opened by typing its name into the Windows search bar and pressing the Enter key to search for it.
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Each location should be thoroughly searched for any suspicious-looking files or subfolders that have recently been added. In order to rid your computer of any possibly harmful temporary files, empty the Temp folder and erase everything inside.
Next, check your system’s Hosts file for any malicious modifications as the following step. You can open the Hosts file by first opening a Run dialog box, (hold down the Windows key and the R key at the same time) and then copy/pasting the following command in the Run box and clicking OK:
notepad %windir%/system32/Drivers/etc/hosts
If the Hosts file has a number of suspicious IP addresses under “Localhost”, as seen in the sample image below, please let us know. If you notice any additional changes in your Hosts file, please let us know in the comments as well, so that we can investigate further. Feel free to get in touch if you have any queries or issues.

![]()
How to Decrypt Agvv files
When dealing with the aftermath of a ransomware attack, there may be a variety of methods for decrypting encrypted files can be employed. Depending on the ransomware variant that has infiltrated the system, some of the available file-restoration options may not work. That’s why the first thing that you need to figure out when you need to decide how to recover your files is what variant of Ransomware you’re dealing with. This information may be found simply by looking at encrypted files for specific file extensions that have been added to them.
New Djvu Ransomware
STOP Djvu is one of the most recent Djvu Ransomware versions. If your encrypted files have the .Agvv file extension at the end, this is an indication that you have been attacked by this variant.
The good news is that if the encryption used by this ransomware is based on an offline key, there may be some chance for people who have had their data encrypted to recover it. If you need help with that, please click on the link below, and you will have access to a file-decryption tool designed for this specific ransomware variant.
https://www.emsisoft.com/ransomware-decryption-tools/stop-djvu
Decryption
After you download the decryption tool file, click on it and select “Run as Administrator”, then select “Yes” to launch it. Make sure you read the instructions and the license agreement on your screen before proceeding. You can start the decryption process by clicking on the Decrypt button.
This tool may be unable to decrypt data encrypted with unknown offline keys or online encryption, so keep that in mind. Also, feel free to use the comments area below this post if you have any queries or concerns.
Important! Prior to decrypting encrypted data, please ensure that your computer has been thoroughly searched for ransomware-related files and malicious registry entries. The recommended anti-virus software and the free online virus scanner on this page may be used to remove the Agvv-related malicious files from your computer.



Leave a Reply