ALPHV Ransomware
ALPHV Ransomware is a recently released Windows virus capable of making all personal data on your computer inaccessible. ALPHV Ransomware is intended to blackmail you for a ransom payment that you are asked to pay in order to get your locked files restored.
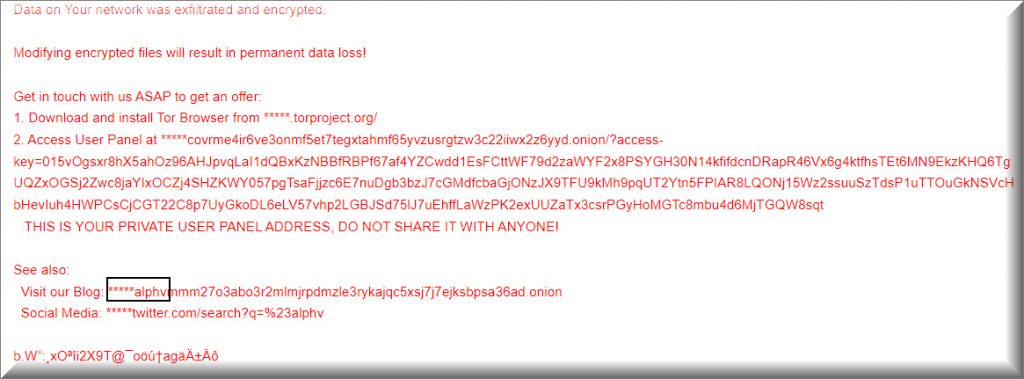
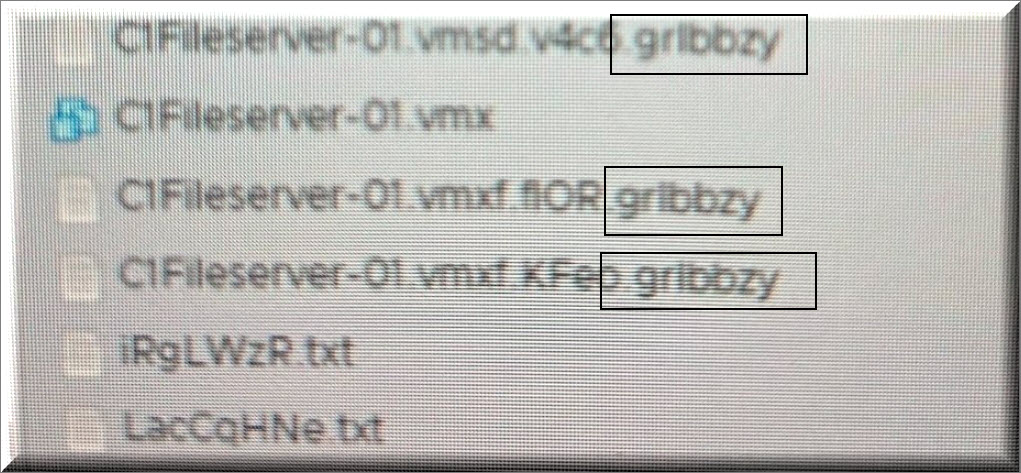
Viruses like this use what is known as data-encryption in order to prevent their victims from accessing the files stored on the attacked computers. According to the criminals, the only way you could restore a file encrypted by ALPHV Ransomware is by paying a certain amount of money to the hackers by sending the sum to a specified virtual purse. Instructions on exactly how you are supposed to make the transactions are provided inside a message that the virus shows on your screen once it is done encrypting your files. The message states that you must pay a certain amount of money or else you’ll never receive the decryption key for your locked data.
One thing we must point out here is that there’s no guarantee you’ll get the promised key even if you pay the ransom so keep that in mind when deciding what to do about the encryption of your files.
In order to avoid having their anonymity uncovered, the hackers behind ALPHV Ransomware and other similar viruses demand that the ransom is paid using the Bitсoin cryptocurrency or another similar cryptocurrency. Such currencies are very difficult to trace, ensuring that the chances of revealing the hacker’s true identities are brought to a minimum.
The ALPHV Ransomware Group
ALPHV is a ransomware group initially detected in November 2021. Experts have proposed that the ALPHV ransomware group could possess robust affiliations with REvil, DarkSide, BlackMatter, and Conti collectives. The ALPHV Ransomware group virus creates a special decryption key, stores it on the hacker’s computers, and then asks the user to pay for it.
If the user refuses to complete the payment, they are threatened to never again be able to access or use their files. However, as we mentioned in the previous paragraph, even if you pay the ransom, this doesn’t really guarantee that the correct decryption key would be provided to you. Therefore, it is pretty much always a better option to not leave the ransom payment as a last resort and to first focus on potential alternatives that do not involve interacting with the cybercriminals who are trying to blackmail you.
The ALPHV Ransomware file decryption
The ALPHV Ransomware file decryption is a data-recovery method that requires you to use the decryption key that the Ransomware has generated during the encryption. The ALPHV Ransomware file decryption is the primary way of restoring the locked data but there may also be alternative options.
We will explore and explain some of the potential alternatives in the guide you will see below after we give you instructions to remove ALPHV Ransomware. Removing the virus is crucial because, even if this doesn’t automatically set your files free, it will ensure that no more data would get locked up in your computer. After you are done removing the Ransomware, you can check out our file-recovery suggestions and see if any of them allow you to recover your data.
SUMMARY:
| Name | ALPHV Ransomware |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Symptoms | Ransomware may cause the system to become sluggish due to an increase in the use of system resources, but most users don’t notice this symptom on time. |
| Distribution Method | Illegal sites that distribute pirated software are usually the ones that contain Ransomware viruses disguised as regular programs. |
| Detection Tool |
Remove ALPHV Ransomware

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:
After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Type msconfig in the search field and hit enter. A window will pop-up:

Go in Startup —> Uncheck entries that have “Unknown” as Manufacturer.
- Please note that ransomware may even include a fake Manufacturer name to its process. Make sure you check out every process here is legitimate.

Type Regedit in the windows search field and press Enter. Once inside, press CTRL and F together and type the virus’s Name.
Search for the ransomware in your registries and delete the entries. Be extremely careful – you can damage your system if you delete entries not related to the ransomware.
Type each of the following in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete everything in Temp. The rest just check out for anything recently added. Remember to leave us a comment if you run into any trouble!

How to Decrypt ALPHV Ransomware files
We have a comprehensive (and daily updated) guide on how to decrypt your files. Check it out here.
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment