REvil Ransomware
REvil is a malicious program created to generate profits for its criminal developers through money-extortion. The typical way REvil attacks the system is through encrypting the files found on it and keeping them hostage for a ransom.
Today, the Internet is by no means a safe place. It has many serious threats that can turn the users’ online experience into a nightmare. In this article, we will address a new ransomware-based infection called REvil. This threat can encrypt all of your important documents, projects, databases, images and other personal files found on your computer, and ask you to pay money to decrypt them. If you have already been faced with a threatening ransom-demanding message on your screen, we suggest you read through the information that follows as, in the next paragraphs, we will offer some methods to avoid the ransom payment. What is perhaps even more important is how to remove REvil, that’s why, below the article, you will find a removal guide and a professional program that can help you do that. Just don’t let the panic take you over and get informed about all your possible alternatives that can help you handle this infection.
The REvil virus
The REvil virus is a ransom-demanding malware that slips into a system without being noticed and encrypts the files stored there. After doing so, the REvil virus generates a message that requests a ransom payment from the victims in order to provide the decryption key for their files.
First and foremost, such a virus operates in secret. It is almost impossible to detect it and to stop its file-encrypting activity on time since most security programs simply let it slip under their radar. Possible sources of the REvil infection may include spam emails and malicious attachments sent from unknown senders, false update notices, malicious online ads, infected web addresses, torrents, shareware, and compromised websites. If you visit or open any of the above-mentioned potential transmitters, the virus will creep directly into your PC (as a drive-by download) and the infection will not be detected.
After the threat has infected your computer, it starts to work as per its plan. First, it scans all the locations where you store your files. Second, it decides precisely which data you are especially interested in using. Then, the ransomware begins the encryption process and converts your files into unreadable bits of data that cannot be opened without a decryption key.
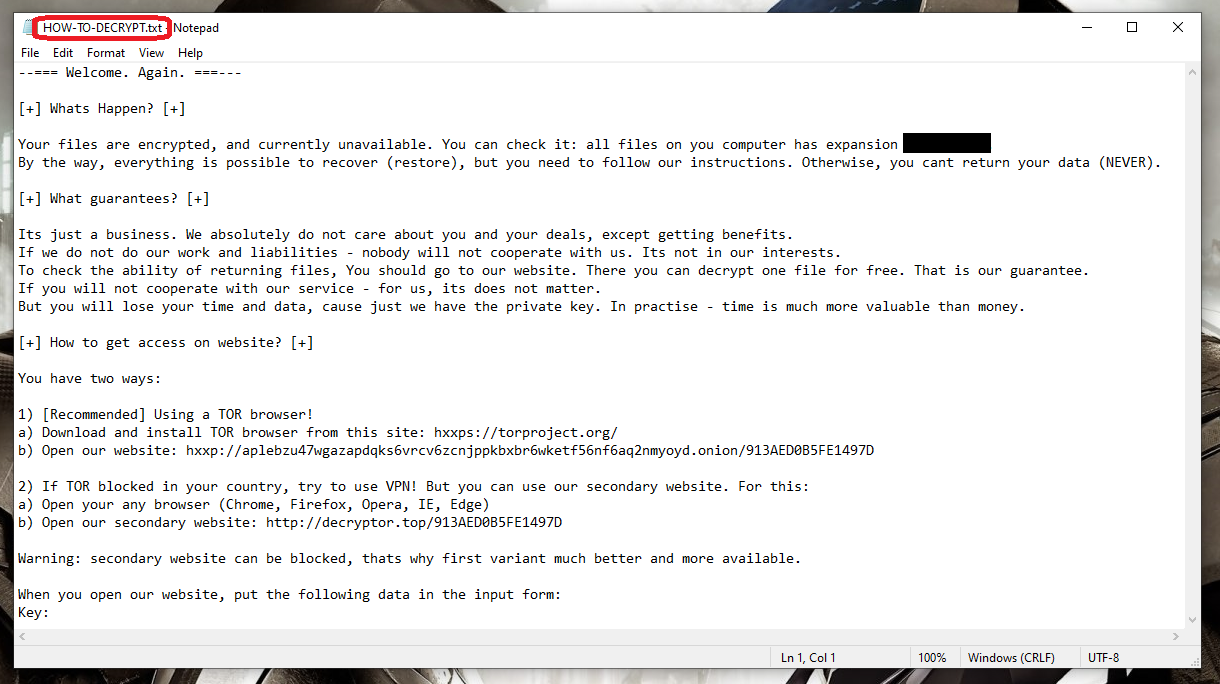
The victims usually have no clues about the ongoing process of encryption. They are informed about the attack after the encoding process is completed. Typically, a warning message appears on their screen and provides ransom payment details, deadlines and threats that try to convince you to pay the required ransom as soon as possible.
The REvil file recovery
The REvil file recovery is an elaborate process that typically requires a special file-decryption key that is kept in secret for a ransom. The REvil file recovery can happen without a decryption key only if the victims have external backup copies, from where they can restore the encrypted files.
You can be a little shaken and concerned about the future of your system and your encoded information after you receive such a threatening screen notification, particularly if you really need to use your computer and your data. But before you take any decision, you must take into account that it is very difficult to remove ransomware infections and it is even harder to decrypt the data that has been affected. The choices you have include hiring a professional in the field of Ransomware recovery, buying a special program that can help you remove the malware and recover some files, or simply writing off your files and reinstalling your operating system. We can also provide you with a possible solution to remove the virus and extract some files from system backups. This is an option that is certainly worth checking out and you can consult the Removal Guide below if you want to give it a try.
SUMMARY:
REvil Ransomware Removal
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Leave a Reply