Approximately few months ago I have gained access
Many security experts have recently been warning about a popular email Bitcoin scam related to a specific type of a Trojan horse infection that’s called “Approximately few months ago I have gained access”. Typically, emails like “Approximately few months ago I have gained access” are just a scam and only aim to trick you.
The “Approximately few months ago I have gained access” Email is designed to scare users.
“Approximately few months ago I have gained access” is a very sneaky Trojan horse infection which may get inside your system without you noticing it. Many users have recently had their computers compromised by this newly detected threat and that’s why, on this page, we decided to provide everyone that needs assistance with a reliable “Approximately few months ago I have gained access” removal tool and a manual removal guide. The information that you will find below contains useful steps about the correct detection and the effective elimination of this nasty Trojan as well as some general information about the malicious capabilities of the malware and its possible harmful uses.
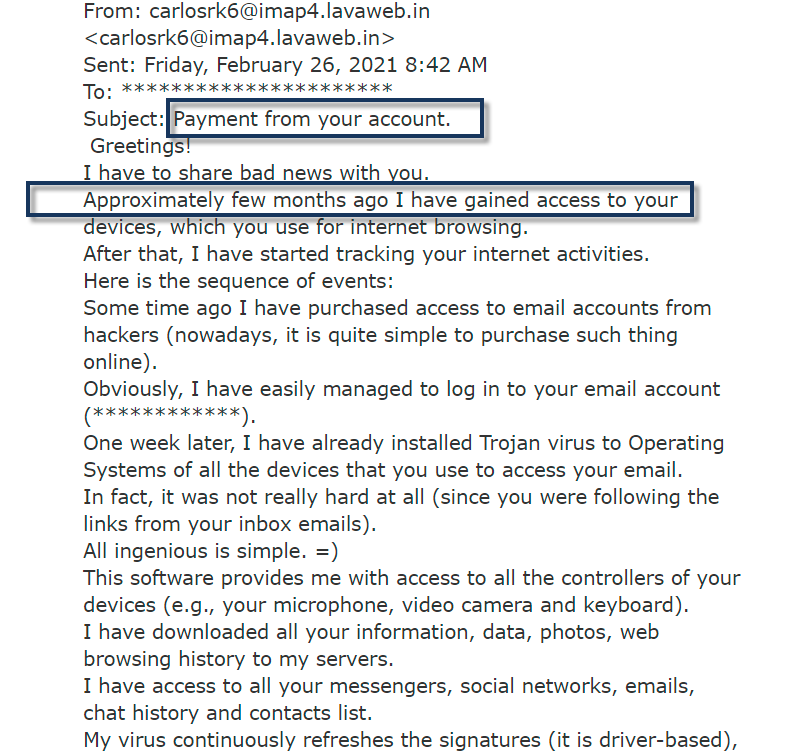
Many of our users reported to us about an ongoing email spam with the following message:
Subject: Payment from your account.
Greetings!
I have to share bad news with you.
Approximately few months ago I have gained access to your devices, which you use for internet browsing.
After that, I have started tracking your internet activities.
Here is the sequence of events:
Some time ago I have purchased access to email accounts from hackers (nowadays, it is quite simple to purchase such thing online).
Obviously, I have easily managed to log in to your email account (************).
One week later, I have already installed Trojan virus to Operating Systems of all the devices that you use to access your email.
In fact, it was not really hard at all (since you were following the links from your inbox emails).
All ingenious is simple. =)
This software provides me with access to all the controllers of your devices (e.g., your microphone, video camera and keyboard).
I have downloaded all your information, data, photos, web browsing history to my servers.
I have access to all your messengers, social networks, emails, chat history and contacts list.
My virus continuously refreshes the signatures (it is driver-based), and hence remains invisible for antivirus software.
Likewise, I guess by now you understand why I have stayed undetected until this letter…
While gathering information about you, I have discovered that you are a big fan of adult websites.
You really love visiting porn websites and watching exciting videos, while enduring an enormous amount of pleasure.
Well, I have managed to record a number of your dirty scenes and montaged a few videos, which show the way you masturbate and reach orgasms.
If you have doubts, I can make a few clicks of my mouse and all your videos will be shared to your friends, colleagues and relatives.
I have also no issue at all to make them available for public access.
I guess, you really don’t want that to happen, considering the specificity of the videos you like to watch, (you perfectly know what I mean) it will cause a true catastrophe for you.
Let’s settle it this way:
You transfer $1500 USD to me (in bitcoin equivalent according to the exchange rate at the moment of funds transfer), and once the transfer is received, I will delete all this dirty stuff right away.
After that we will forget about each other. I also promise to deactivate and delete all the harmful software from your devices. Trust me, I keep my word.
This is a fair deal and the price is quite low, considering that I have been checking out your profile and traffic for some time by now.
In case, if you don’t know how to purchase and transfer the bitcoins – you can use any modern search engine.
Here is my bitcoin wallet: 1GGZpqXsqKWSRnjJ1SHFaE5VPkMHHsKToX
You have less than 48 hours from the moment you opened this email (precisely 2 days).
Things you need to avoid from doing:
*Do not reply me (I have created this email inside your inbox and generated the return address).
*Do not try to contact police and other security services. In addition, forget about telling this to you friends. If I discover that (as you can see, it is really not so hard, considering that I control all your systems) – your video will be shared to public right away.
*Don’t try to find me – it is absolutely pointless. All the cryptocurrency transactions are anonymous.
*Don’t try to reinstall the OS on your devices or throw them away. It is pointless as well, since all the videos have already been saved at remote servers.
Things you don’t need to worry about:
*That I won’t be able to receive your funds transfer.
– Don’t worry, I will see it right away, once you complete the transfer, since I continuously track all your activities (my trojan virus has got a remote-control feature, something like TeamViewer).
*That I will share your videos anyway after you complete the funds transfer.
– Trust me, I have no point to continue creating troubles in your life. If I really wanted that, I would do it long time ago!
Everything will be done in a fair manner!
One more thing… Don’t get caught in similar kind of situations anymore in future!
My advice – keep changing all your passwords on a frequent basis
In case you are wondering how a threat like “Approximately few months ago I have gained access” could have sneaked inside your PC, you should know that such an advanced form of malware can trick you in many ways. What’s more, being a typical Trojan, this threat can be disguised as almost anything. According to the information that we have, the majority of infections happen when users click on intriguing spam messages or malicious emails with harmful attachments.
The Approximately few months ago I have gained access Email
If you have opened and interacted with the “Approximately few months ago I have gained access” Email, it is possible that its creators might have inserted malicious code that you might have triggered the moment you have clicked the message. That’s why it is a good idea to check your system for hidden malware by running a full scan with a reliable tool.
However, the contamination might happen even after a single click on some sketchy advert coming from a shady website or a misleading pop-up link or by visiting phishing sites or downloading compromised files and software. That’s why, even if you generally try to stay away from the typical virus transmitters (such as pirated content, free setup packages or adult sites), there is absolutely no guarantee that you won’t ever bump into a possible malicious carrier without knowing it.
“Approximately few months ago I have gained access” may infect you instantly, the very moment you get tricked into interacting with one of its numerous infected transmitters. Luckily, since you are on this page, you most probably already know that you have been compromised and now the challenge is to safely remove the infection before it manages to cause any serious harm. The fast and effective elimination of such an advanced Trojan, however, will require your full attention and caution. That’s why we suggest you carefully study the instructions below and use the assistance of a dedicated malware removal tool for optimal results.
How bad can an infection with “Approximately few months ago I have gained access” be?
The reason we urge you to immediately take actions against “Approximately few months ago I have gained access” and remove it is because the longer it remains on the system, the greater the damage that it might cause. And, unfortunately, we cannot tell you exactly how bad the consequences of the infection could be because it is typical for the Trojan-based threats to be very versatile. They may be programmed to perform specific criminal actions one after the other, which means that they can put your computer and your personal information in great danger while causing various issues on the OS.
Most new Trojans, possibly including “Approximately few months ago I have gained access”, may silently focus on performing actions of theft, espionage, fraud, system corruption and even virus insertion, without indicating any suspicious activity. They may steal all sorts of sensitive information from the infected computer, modify, replace or delete its data and secretly inject a ransomware or a spyware into the system, which can further blackmail and harass the victims. Sadly, without a reliable antivirus program which can scan the system for hidden malicious activities, it can sometimes be highly unlikely to notice and effectively remove the infection on time
SUMMARY:
| Name | Approximately few months ago I have gained access |
| Type | Trojan |
| Danger Level | High (Trojans are often used as a backdoor for Ransomware) |
| Symptoms | In some cases, unusual system issues, frequent errors and significant sluggishness may give the Trojan away. |
| Distribution Method | Most commonly distributed via malicious email links and attachments, phishing sites, torrents, infected ads and compromised downloads. |
| Detection Tool |
Approximately few months ago I have gained access Email Removal
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide
![]()
Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).
![]()
WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.
![]()
Hold together the Start Key and R. Type appwiz.cpl –> OK.

You are now in the Control Panel. Look for suspicious entries. Uninstall it/them. If you see a screen like this when you click Uninstall, choose NO:

![]()
Type msconfig in the search field and hit enter. A window will pop-up:

Startup —> Uncheck entries that have “Unknown” as Manufacturer or otherwise look suspicious.
- Remember this step – if you have reason to believe a bigger threat (like ransomware) is on your PC, check everything here.
Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
![]()
Type Regedit in the windows search field and press Enter.
Once inside, press CTRL and F together and type the virus’s Name. Right click and delete any entries you find with a similar name. If they don’t show up this way, go manually to these directories and delete/uninstall them:
- HKEY_CURRENT_USER—-Software—–Random Directory. It could be any one of them – ask us if you can’t discern which ones are malicious.
HKEY_CURRENT_USER—-Software—Microsoft—-Windows—CurrentVersion—Run– Random
HKEY_CURRENT_USER—-Software—Microsoft—Internet Explorer—-Main—- Random
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment