The Diavol Ransomware
A new ransomware dubbed “Diavol” has been linked to the threat actors behind the TrickBot virus, according to a new cybersecurity discovery.
In an unsuccessful attack against one of the customer’s systems earlier this month, malware payloads associated with Diavol and Conti ransomware were installed on several computers, researchers from Fortinet’s FortiGuard Labs revealed.
Ever since it first appeared, back in 2016, TrickBot has been a malware primarily written for Windows systems. Various modules within the malware have been utilized to perform a wide range of malicious activities on targeted networks, including theft of sensitive information as well as ransomware attacks.
Despite law enforcement’s best efforts during the years, the botnet has proved to be robust. This is because of the nature of the malware, which is always developing, frequently coming up with new tools and tactics to carry out new attacks.
So far, there have only been one instance in which the Diavol malware has been used in the wild. At this time, the source of the breach remains unclear. What has been revealed, however is that the payload’s source code appears to have similarities with that of Conti.
The researchers went on to say that the malware uses user-mode Asynchronous Procedure Calls (APCs) without a symmetric encryption method, but instead relies on a rather unusual process for encryption. Typically, most Ransomware developers tend to try to apply encryption as quickly as possible. Asymmetric encryption methods, however, are much slower than symmetric algorithms, which makes them less common choice.
Also notable is the obsufication technique that Diavol uses to hide its traces. The malware conceals its code in bitmap images, which hide the code’s routines and also conceal the manner in which the routines are loaded into a buffer with execute rights.
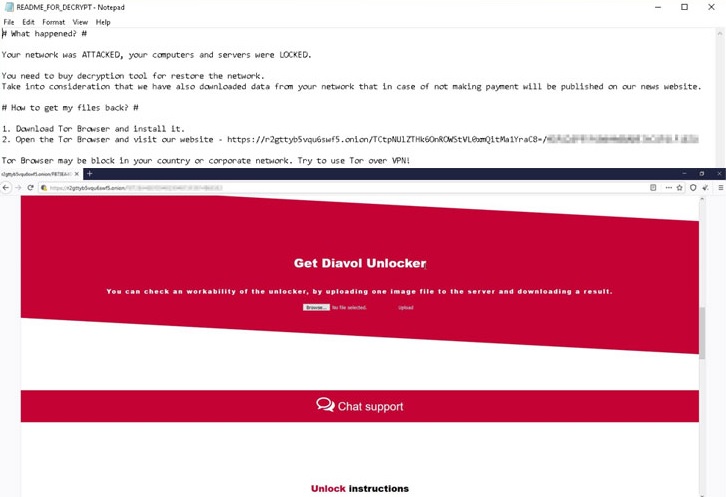
The first actions Diavol does as soon as it sneaks inside the infected computer include establishing a connection to a remote server, stopping existing processes, scanning for local disks and data to encrypt, and removing any recovery techniques by erasing shadow copies. Next, the malware moves into locking the detected files and then changing the desktop wallpaper with a ransom-demanding message.

Leave a Comment