EvilQuest Ransomware
This week, online security researchers have found a new strain of ransomware for macOS users. The threat is called OSX.EvilQuest, and is quite different than other known ransomware infections that target Mac computers. Aside from encrypting the victim’s files, EvilQuest installs a keylogger, and a reverse shell, and steals cryptocurrency wallet-related files from infected hosts.
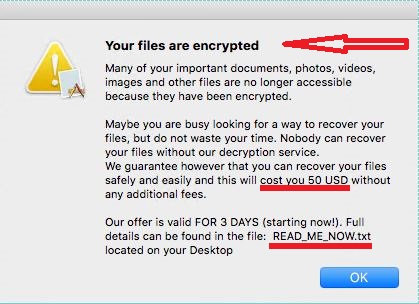
EvilQuest pop-up notification
Patrick Wardle, Principal Security Researcher at Jamf, said that, with the help of this malware, the intruder can establish full control over the infected machine. What this means is that even if the victim pays the demanded ransom, the malicious actor will still have access to the compromised computer and can continue to steal files and keep track of keyboard strokes.
A number of reputed macOS safety investigators are currently analyzing this new threat. The professionals are seeking for a bug or a weakness in the ransomware’s encryption code that they could exploit to create a decryptor that could help the victims who have already been attacked.
So far, what is known about EvilQuest is that it is mainly distributed via pirated macOS applications that can be found on torrent sites and web forums. The ransomware has been spotted in a software package named Google Software Update, as well as hidden inside the installer of a macOS security tool named Little Snitch. However, it is suspected that the malicious OSX.EvilQuest file is broadly distributed across the web with the help of many other applications and legitimate-looking transmitters.
An in-depth technical analysis of EvilQuest reveals that the ransomware is pretty fast and straightforward as it starts to directly encrypt user files as soon as it infects the system. The moment the secret file-encryption process ends, a notification appears on the screen, informing the victims that their files have been encoded and cannot be recovered unless they pay a ransom. The victims are told to open a ransom note in the form of a text file on their screen for more instructions.
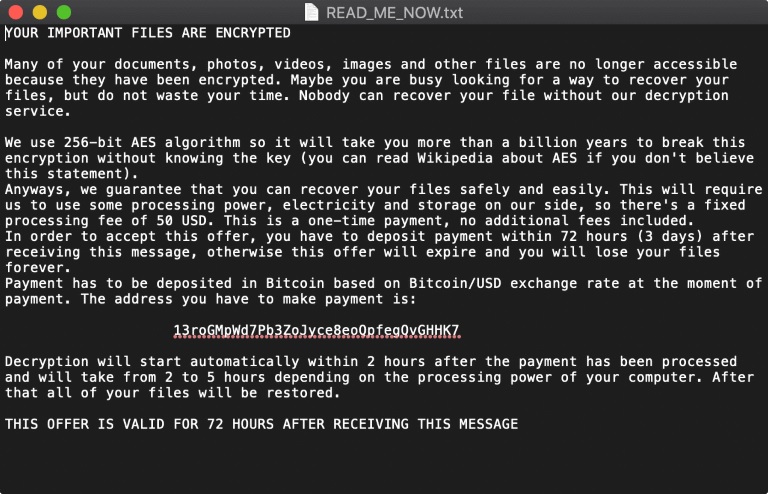
The EvilQuest Ransom note
The files that EvilQuest targets with its encryption may include the following extensions:
.pdf, .doc, .jpg, .txt, .pages, .pem, .cer, .crt, .php, .py, .h, .m, .hpp, .cpp, .cs, .pl, .p, .p3, .html, .webarchive, .zip, .xsl, .xslx, .docx, .ppt, .pptx, .keynote, .js, .sqlite3, .wallet, .dat
After the file-encryption process completes, the malware installs a keylogger to record the user’s keystrokes. It even installs a reverse shell which allows the attacker to connect to the compromised host and to execute custom commands.
But this is not everything. EvilQuest will also look to steal files employed by cryptocurrency wallet applications such as:
- “wallet.pdf”
- “wallet.png”
- “key.png”
- “*.p12”
The ransomware is also reported to attempt to change Google Chrome upgrade files and use them as a method of persistence on infected hosts. The idea of this move is when either of the modified files is executed, the malicious code to run. However, Chrome can see the modified files, and replace them with clean copies as soon as they are running, so it is not quite clear what is the ultimate goal of these changes.
After KeRanger and Patcher, EvilQuest is the third strain of ransomware that is targeting specifically macOS users. Leading security software providers are taking actions to update their software for Mac to detect the new ransomware and stop it before it causes damage.

Leave a Comment