ExcludeProc
In the article below you will find some essential information about ExludeProc Virus. Probably you already know that ExludeProc is a virus from the Trojan horse family.
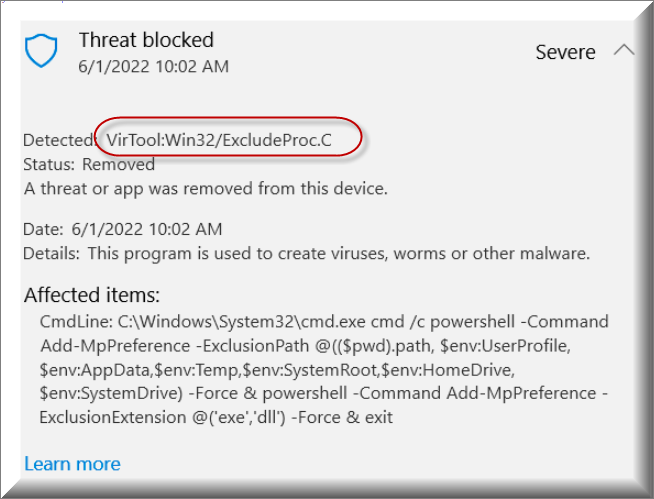
What you may not know is what to expect from it, how you have caught it; and how you are expected to remove it from your computer. Fortunately, we have some basic tips about all of these.
What is a Trojan horse virus?
Trojans are the most widely spread computer threats – they make up almost 75+ per cent of the entire number of malware-infected machines worldwide. The reason for their commonness is that they could be programmed to perform a great number of malicious tasks while on your computer. Actually, what makes them a family is not the way they might affect you and your machine, but the way they get distributed and the way they infect your computer. Generally, every single Trojan might install itself on your PC – it does not have to look for your indirect approval and trick you into incorporating it into your system. Also, the most popular sources of this kind of malware may be numerous but they are almost always the same, when it comes to the majority of the infections.
The most common ways hackers distribute ExludeProc Virus
Basically, there may be countless opportunities when it comes to the distribution of ExludeProc or Energy.exe virus (and any other Trojan horse virus, by the way). Nevertheless, the majority of the recorded infections have come from some particular sources, which we are going to describe below. In case you are dealing with ExludeProc Virus, you have probably caught it from:
- Malicious ads popping up around the Internet:
Such malware could be injected into your system when you accidentally click on a malicious advertisement. Probably you know that most of the ads online are merely marketing tools, produced by annoying, yet more or less harmless software like Adware and browser hijackers. However, some of them might be generated by malware-based programs and might automatically infect you with serious threats like ExludeProc Virus.; - Illegal web pages, sharing torrents, movies, software, videos… etc.:
Very often hackers spread Trojans by putting them together with torrents and sharing them through illegal websites, most commonly the ones which violate various copyright policies. Logically, in case you use such movie and software sources, you are likely to catch a form of malware from there.; - Emails:
Improbable as it sounds, each email that you receive may contain Trojans. What’s worse, not only could it include viruses like ExludeProc Virus, but it can also contain Ransomware. By the way, Trojans could be the most common viruses ever developed, but the versions of Ransomware the most awful ever created. This ransom-requiring malware encrypts all of the data that matters to you and then wants you to pay for its recovery. To top it all, even if you pay, you still get no decryption guarantee. Often the Ransomware-Trojan pack is distributed inside emails and their attachments.
Of course, there could be many more potential sources, but please, make sure that you avoid the aforementioned ones to prevent possible contamination.
ExludeProc Virus is typically used for:
This paragraph discusses the probable ways of exploiting such a Trojan horse virus, which might also be numerous, but there are some typical ones and we are going to mention exactly them.
- Deleting data/ formatting disks and drives:
Once your machine has caught a Trojan, the virus could completely erase all the files on your disks and drives. Actually, some hackers do not personally target you or your data, they just have fun in this way. - Spying:
Unfortunately, such malware is often used for spying on a particular individual. If this is the case, the virus may perform many spying-oriented activities such as enabling your webcam remotely and watching you live; copying and keeping detailed data of your keystrokes, account credentials and banking details; and even turning on your mic and recording your personal conversations. This is probably the most horrible usage a virus may have. - Spreading other viruses:
As we have mentioned above, Trojans are sometimes bundled with Ransomware. What they do is to automatically infect your machine with themselves and with the corresponding Ransomware. Again, this one is among the most awful usages. ; - System crash / data corruption and modification:
Any Trojan could make your system completely unusable by crashing it, slowing it down ; or corrupting and modifying some important data and software on it.
Fighting ExludeProc Virus
Luckily, it is NOT impossible to get rid of ExludeProc Virus. All you need to do is to scroll down and use our Guide. Simply make sure that you read it once or twice to figure out how to best implement each instruction. Break a leg!
SUMMARY:
| Name | ExludeProc |
| Type | Trojan |
| Detection Tool |
Remove ExludeProc Virus
If you are looking for a way to remove ExludeProc you can try this:
- Click on the Start button in the bottom left corner of your Windows OS.
- Go to Control Panel -> Programs and Features -> Uninstall a Program.
- Search for ExludeProc and any other unfamiliar programs.
- Uninstall ExludeProc as well as other suspicious programs.
Note that this might not get rid of ExludeProc completely. For more detailed removal instructions follow the guide below.
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide
![]()
Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).
![]()
This is the most important step. Do not skip it if you want to remove ExludeProc Virus successfully!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.
![]()
Hold together the Start Key and R. Type appwiz.cpl –> OK.

You are now in the Control Panel. Look for suspicious entries. Uninstall it/them. If you see a screen like this when you click Uninstall, choose NO:

![]()
Type msconfig in the search field and hit enter. A window will pop-up:

Startup —> Uncheck entries that have “Unknown” as Manufacturer or otherwise look suspicious.
- Remember this step – if you have reason to believe a bigger threat (like ransomware) is on your PC, check everything here.
Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
![]()
Type Regedit in the windows search field and press Enter.
Once inside, press CTRL and F together and type the virus’s Name. Right click and delete any entries you find with a similar name. If they don’t show up this way, go manually to these directories and delete/uninstall them:
- HKEY_CURRENT_USER—-Software—–Random Directory. It could be any one of them – ask us if you can’t discern which ones are malicious.
HKEY_CURRENT_USER—-Software—Microsoft—-Windows—CurrentVersion—Run– Random
HKEY_CURRENT_USER—-Software—Microsoft—Internet Explorer—-Main—- Random
If the guide didn’t help you, download the anti-virus program we recommended or ask us in the comments for guidance!

Leave a Comment