*Fatp is a variant of Stop/DJVU. Source of claim SH can remove
Fatp
Fatp is a cryptovirus of the ransomware type that uses an incredibly complex encryption algorithm to prevent access to important user data. Fatp secretly seals up a number of file types that are stored on the infected system, and in return for their decryption, demands a ransom payment from the victim.
Ransomware viruses such as Fatp, Zate and Zatp have the ability to invade any computer without being detected and encrypt its data or lock the access to the main screen. In the recent years, this kind of malware has become one of the most terrifying security challenges on the Internet. Security analysts have experienced a spike in ransomware attacks over the span of a short time and, in this article, we will concentrate on one of the latest representative of this malware group’s that is named Fatp.
The Fatp virus
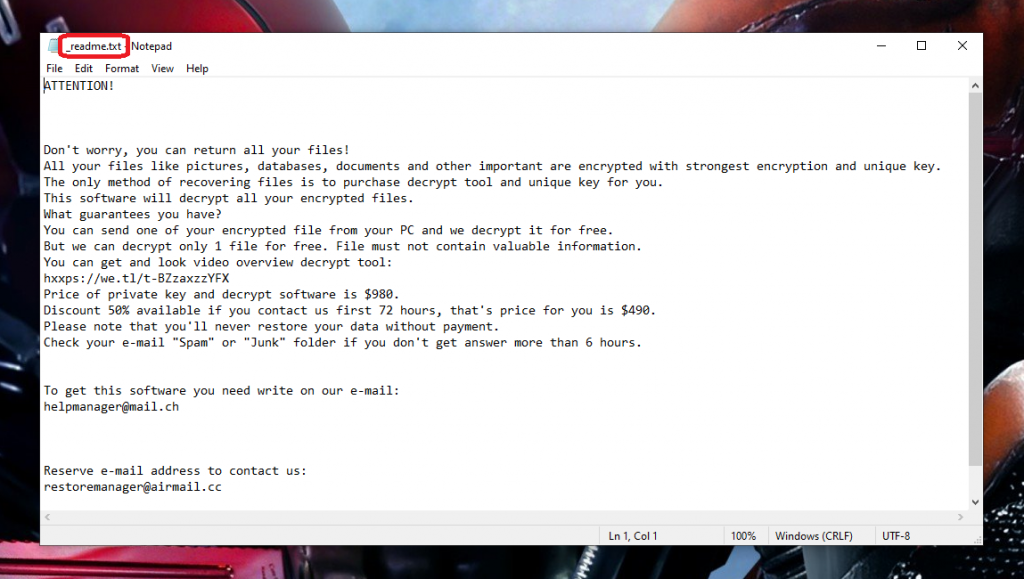
The Fatp virus is an infection that will display a scary ransom-demanding note on your computer as soon as it renders your files unavailable through a complex encryption. Usually, the hackers behind the Fatp virus ask for some fixed amount of money (mostly in the form of a cryptocurrency) and promise to provide the victims with a file-decryption key in return for receiving the payment.
Sadly, there are several things that you need to consider regarding this blackmailing plan. Firstly, the decryption key that the hackers promise may not always work and even if you pay for it, that may not recover all of your information. Secondly, there is a high chance the hackers never send you anything in return for your money. In many cases the crooks simply vanish once they receive the payment. There are also cases where the criminals return with a demand for more money and ask for another ransom payment and you basically cannot really trust them. Therefore, it is advisable to explore other alternatives that may help you remove Fatp and recover some of your data without paying a ransom.
The Fatp file encryption
The Fatp file encryption is a highly advanced algorithm used for encrypting a variety of commonly used digital data. The process of Fatp file encryption typically happens in the background of the system and does not show any visible symptoms that allow its identification.

This is the reason why, in most cases, the victims of ransomware are taken by surprise and hardly can do anything to stop or remove the infection on time. What makes matters worse is that although the virus removal is very critical for your system’s protection, it will typically take additional measures to potentially restore your data from the applied encryption.
Unfortunately, the successful data recovery solutions may not be many. You would usually have to depend on your external backup copies. However, in the removal guide that you can find below, we have also included a separate file recovery section with a range of recommendations which may help you restore some of the sealed information.
We should warn you, though that, that whatever course of action you decide to take, there is no assurance that you can recover entirely from the attack of the ransomware threat. Therefore, we highly recommend that you take measures to protect your PC and data with reliable security software and frequent file backups of the most critical information.
SUMMARY:
| Name | Fatp |
| Type | Ransomware |
| Detection Tool |
*Fatp is a variant of Stop/DJVU. Source of claim SH can remove
Remove Fatp Ransomware

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Fatp is a variant of Stop/DJVU. Source of claim SH can remove
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Type msconfig in the search field and hit enter. A window will pop-up:

Go in Startup —> Uncheck entries that have “Unknown” as Manufacturer.
- Please note that ransomware may even include a fake Manufacturer name to its process. Make sure you check out every process here is legitimate.

*Fatp is a variant of Stop/DJVU. Source of claim SH can remove
Type Regedit in the windows search field and press Enter. Once inside, press CTRL and F together and type the virus’s Name.
Search for the ransomware in your registries and delete the entries. Be extremely careful – you can damage your system if you delete entries not related to the ransomware.
Type each of the following in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete everything in Temp. The rest just check out for anything recently added. Remember to leave us a comment if you run into any trouble!

How to Decrypt Fatp files
The removal of Fatp will improve the security of your computer and prevent the virus from encrypting any of your information in the future. However, it will not decrypt any files that have already been encrypted. You still need to make a decision between paying the demanded ransom to unlock the files or attempting to restore the data using alternative techniques. We are able to provide you with a tool that specializes in how to decrypt Ransomware without paying the ransom, and we highly recommend that you check it out and try to recover your files with it.
Before anything else, you must ensure that the malicious software has been completely removed from your computer. If you don’t do that, there’s a good possibility that the data you tried so hard to recover may become encrypted again. The professional malware removal program that is provided on our website is one tool that could assist you in determining whether your computer still has any traces of the Fatp virus. If there are any files that may contain malicious data, you can check them with the free online virus scanner.
Deciphering data that has been encrypted by ransomware isn’t easy. Even for experienced professionals in the area of cyber security, there is no one-size-fits-all solution when it comes to this type of malware. The process of retrieving data may be further complicated by the fact that the methods for decrypting various ransomware versions might differ from one another. One of the first things you need to do to have a chance of being successful in data recovery is to accurately recognize the variant of ransomware that has attacked your computer. You can do this by looking at the file extensions of the files that were encrypted.
New Djvu Ransomware
Recently, a new variant of ransomware called STOP Djvu ransomware was found, and according to sources, it has been shown to encrypt data by appending the .Fatp suffix at the end of the file name. Those who were targeted by the threat were sent a demand for a ransom payment in return for a key that may potentially restore their data. However, victims who have lost data as a result of the .Fatp encryption should not pay the ransom. There is a decryption tool at the URL below that might help them get their data back without giving money to the hackers.
https://www.emsisoft.com/ransomware-decryption-tools/stop-djvu
If you are a victim of Fatp, all you need to do is go to the URL and download the STOPDjvu executable file from the page. Please carefully read the license agreement and the instructions for use before you begin using the application. Both of these documents can be found on the website. The next step is to pay attention to what the application needs you to do, then proceed to click the Decrypt button.
Please bear in mind that this program, despite the fact that it seems to have a great deal of potential to recover Fatp-encrypted data, does have some restrictions. For instance, it may not be able to decode files that have been encrypted using a key that is not stored in its database or with an online algorithm.
Final notes
The elimination of all traces of the Fatp virus should be possible if all the steps outlined in this guide are carried out completely. On the other hand, if you have a reason to believe that the Ransomware may still be active on your computer, it is strongly recommended that you scan your machine with the powerful anti-malware tool that has been provided on this page. With its assistance, you should be able to locate and remove any remnants of the Ransomware that may still be present. The program also has the potential to be helpful in the future since it will keep your computer safe against other potential attacks. Last but not least, the comments area on this page is always open for our readers, so if you have any questions or want more help from us, feel free to leave us a comment there whenever you like.

Leave a Comment