*Zate is a variant of Stop/DJVU. Source of claim SH can remove
Zate
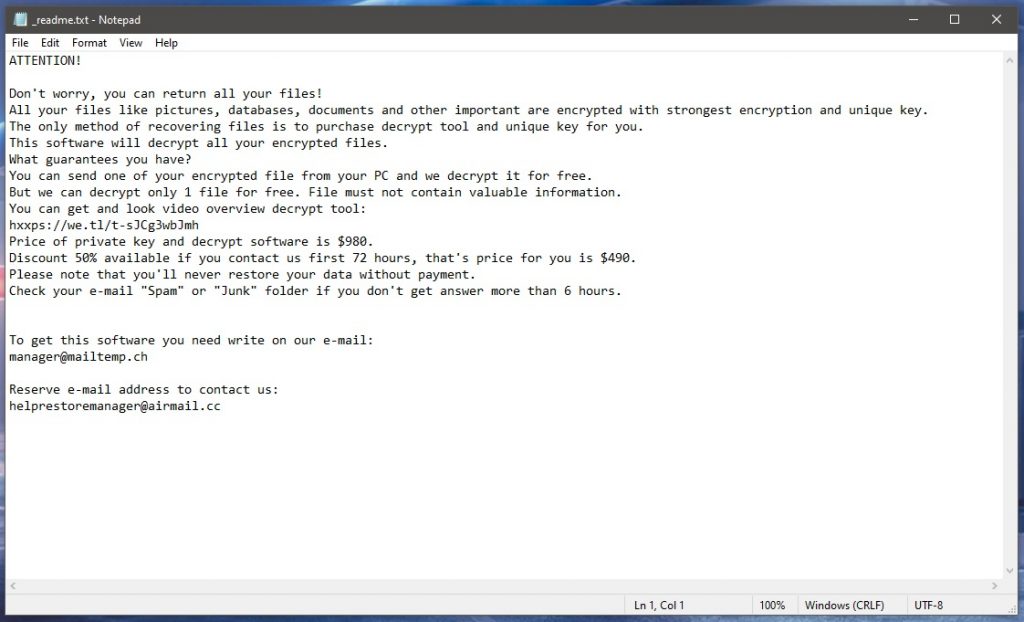
Zate is a malicious program that attacks Windows computers with the aim to make the files stored on them unavailable. Zate locks users’ data with its advanced encryption algorithm, which renders all affected files inaccessible to any regular program that the user may have.
If your system has bee invaded by Zate, there are several things you should know about this threat. The first one is the fact your system probably won’t get damaged by the virus itself. The goal of this threat is to extort money from you using your locked files as leverage. It doesn’t need to damage the system of the attacked computer in order to achieve this goal. What this means is if you don’t have any highly important data on your computer that you can’t afford to lose, the attack from this threat shouldn’t be such a huge problem. Ransomware viruses can be removed and we will help you get this particular one off of your computer.
One thing to bear in mind, though, is that Ransomware infections like Zate, Zatp, Bozq this one oftentimes get distributed with the help of a Trojan infection. Trojans are versatile malware tools and if one such piece of malware has inserted the Ransomware in your computer, it is possible that the Trojan can damage your system. That is why it’s advisable to scan your computer with a dependable security program (such as the one linked in our removal guide) in order to detect any additional threats that may potentially currently be in your computer alongside the Ransomware.
The Zate virus
The Zate virus is a file-encrypting malware threat used for money extortion. The Zate virus is programmed to sneak silently in the computer of its target and then initiate an encryption process that locks the user’s files.
The main problem most people encounter when faced with Ransomware is the potential loss of data that the virus may cause. As we said, if none of the files on your computer that the Ransomware has managed to encrypt are important to you, then all you need to do is remove the virus using the guide from below. However, what if the files are important to you? Should you go for the ransom payment in such a case? Well, though there cannot be a universal answer to this question and it really depends on the specific situation, we usually advise our readers to try some other methods before they consider paying the ransom. This is mainly because of the risk of losing the money without getting a key that can restore your data.
The Zate file decryption
The Zate file decryption is the process of restoring access to the encrypted files through the use of a decryption key. The Zate file decryption is usually not possible if you do not have the required key.

That being said, there may be other ways to restore your data, even though there can’t be guarantees on how effective the said ways would be. In the second part of the next guide, you will find some possible recovery solutions that we advise you to try as an alternative to the ransom payment.
SUMMARY:
| Name | Zate |
| Type | Ransomware |
| Detection Tool |
*Zate is a variant of Stop/DJVU. Source of claim SH can remove
Remove Zate Ransomware

To begin, we suggest that you bookmark this page by clicking on the bookmark icon (top right). This will save you time and allow you to access the Zate removal guide quickly after the system reboot that follows.
The next thing that you need to do is to restart your computer in Safe Mode. After restarting the system (you can click the link for assistance), please return to this page for the rest of the Zate removal instructions.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Zate is a variant of Stop/DJVU. Source of claim SH can remove
Malware infections, like Zate, often carry out their damaging actions invisibly in the background. The good news is that if you follow the instructions in this step, you should be able to detect and end any suspicious processes that may be running on your computer.
The easiest way to do that is to access the Windows Task Manager, (CTRL+SHIFT+ESC) and then click the Processes Tab. Take note of processes that use a lot of resources, have an unusual name, or otherwise look suspicious, and which you cannot associate with any of the software you have already installed.
Right-click on any suspicious process and select “Open File Location” from the context menu to inspect its files.

The next step is to run a virus scan on the process files using the scanner provided below:

If any potentially hazardous files are detected during the scan, you should stop the process related to them from running by right-clicking on it and selecting End Process. And then the files themselves should be deleted from their File Location.
The same should be applied for each process that contains risky files until you are certain that the system is safe, and no dangerous processes are running in the background.
![]()
Aside from stopping the Zate-related processes in the Task Manager, victims of this ransomware should also disable any startup items created by the threat.
This can be done by starting System Configuration (you can type msconfig in the Windows search field and open the result) and check out what’s listed under the Startup tab:

Any startup item with an “Unknown” manufacturer or a random name should best be researched online and unchecked if you find out enough evidence that it is related to Zate. Also, you should research any entries that don’t seem to be related to any of the trusted software on your computer and uncheck them as well.
![]()
*Zate is a variant of Stop/DJVU. Source of claim SH can remove
The next step is to run a registry scan to see whether the ransomware has inserted any hazardous entries there without your knowledge. To access the Registry Editor, enter Regedit in the Windows search bar and hit Enter. If you don’t want to waste time, press and hold CTRL and F on your keyboard together and type the name of the ransomware exactly as it is inside the Find box. Click on Find Next to search for entries that match the name of the threat, and then delete everything that appears in the results.
Please be aware that removing anything that isn’t directly related to Zate in this step might do more damage than help to your system, so proceed with extreme caution. Zate and any other ransomware-related files should be removed from your registry using professional removal tools to prevent any further damage.
Next, search your computer’s Hosts file to see whether any changes have been made in there. Windows and R key combination may be used to access the file. Simply paste the following command into the Run box that opens and press Enter:
notepad %windir%/system32/Drivers/etc/hosts
Please leave us a comment if the Hosts file has been updated to include suspicious-looking IP addresses under Localhost like those seen in the example image below. We’ll take a look at them and propose the best course of action.

There are few more locations where you should search for suspicious files or folders associated to Zate. We recommend you open the following locations in Windows Search by typing them in the search bar exactly as they appear in the text below.
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Remove just the files that look harmful from these locations. At the end, delete everything in the Temp folder.
![]()
How to Decrypt Zate files
It is important to note that when you are dealing with ransomware, you may need to take a different approach and use different methods, depending on the variant of ransomware that has infected you. Unfortunately, there is no universal solution for all variants of ransomware that exist, therefore, below we will try to be more specific and offer a solution for Zate. You can easily recognize that you have been infected with Zate if you look at the Zate extensions that it adds to the encrypted files.
However, please keep in mind that in order to decrypt ransomware-encrypted data, you must first ensure that the infection has been entirely removed from your computer. Professional anti-virus software, such as the removal program and the free online virus scanner on this website, may be used to get rid of Zate and other sophisticated infections.
New Djvu Ransomware
STOP Djvu Ransomware is the latest variant of the Djvu Ransomware family. Victims of this variant can recognize it because it adds the .Zate file extension to the files it encrypts. While, generally, it can be next to impossible to decrypt files encoded by new variants, there is a means to decrypt files that have been encrypted by Zate if those files have been encrypted with an offline key. Below we have linked a decryption program that may assist you get your data back. You can download it for free by clicking on the link below and then selecting the Download button on the page:
https://www.emsisoft.com/ransomware-decryption-tools/stop-djvu
Decryption
After clicking “Run as Administrator,” the decryptor will launch. The licensing agreement and any brief instructions that show on the screen must first be read in full before moving on. Then click on the Decrypt button to start the process of decrypting your data. Please keep in mind that this tool is unable to decode data that has been encrypted using unknown offline keys or online encryption.
Let us know what you think in the comments section below or if you have any questions or concerns.

Leave a Comment