Formgrabber
Trojans are the most dangerous and complex forms of malware you might face. Speaking of them, Formgrabber is a relatively recent Trojan horse virus, that has been causing trouble for a growing number of web users and needs to be removed.

The purpose of this article and the Formgrabber removal guide that follows is to educate you about the risks associated with this Trojan, the most common entry points, and the best practices for removing it from your machine. After reading it, you should have a better grasp of the malware at hand and the steps you can take to avoid such threats in the future.
Formgrabber disconnected
Malwares like “Formgrabber disconnected” have many characteristics that can be used to distinguish them from the rest of the malware, but one of the most striking is their versatility. We can’t say for sure what type of harm a threat like “Formgrabber disconnected” may cause on your machine, but we can outline the most common ways in which a Trojan like this one may be employed.
The most typical results of a Trojan attack are the corruption and destruction of data. This might be the case in a variety of business settings, such as if a rival company needs to get rid of confidential information that you have. A Trojan might easily remove everything from your hard drive by formatting it.
Formgrabber disconnected, killing connection
Invasion of privacy and theft. Trojans like “Formgrabber disconnected, killing connection” allow hackers to secretly monitor your computer’s activity. The “Formgrabber disconnected, killing connection” malware might potentially spy on you using your webcam and microphone from a remote location. The hackers behind the malware might use this information to get insight into your life and use it against you in the form of extortion, theft, and harassment.
Exploitation of the system’s resources. Having a Trojan horse called Formgrabber installed on your PC may put your computer at risk of becoming part of a botnet and being used to infect other computers on the same network or distribute spam. Another potential use for this kind of malware is cryptocurrency mining, with the crypto being sent to the attackers who control the Trojan.
Insertion of malicious software. Formgrabber is a Trojan that may operate as a go-between for you and other viruses, such as ransomware crypto-viruses that seek to encrypt your data for a ransom. In this case, the Trojan will first get into your computer, and then, with its help, another infection will be inserted without your knowledge.
Trojans’ infection techniques
The Trojans’ infection techniques are as diverse as their versatile uses. Social engineering is often employed to spread viruses like Formgrabber and Altruistics through the Internet by tricking unsuspecting web users into downloading the infection.
Another common method of spreading this infection is via spam emails. The spam emails could seem to come from trusted companies like banks, utility companies, or well-known online stores. Most of these spam emails will instruct the recipient to do something in order to get them infected. For instance, it could be to download or open the attached file or follow a specific link that is infected.
Cybercriminals commonly distribute Formgrabber through different low-quality websites, software cracks, keygens, and free downloads. The malicious software might be hidden in a piece of media downloaded from the internet, such as a video file, a game, or a torrent. It might even be hidden as a pop-up or a banner ad. If you click on it, you’ll be redirected to a page where the malware will be automatically downloaded without your knowledge.
This being said, staying away from anything that could be malicious and investing in professional antivirus software are your best bets for keeping your computer safe.
SUMMARY:
How to Remove the Formgrabber disconnected Virus?
To remove the Formgrabber virus, you must perform each of the following actions on your computer:
- Delete any questionable programs that got recently installed on your computer, especially if they got installed without your approval.
- Look at the list of processes in the Task Manager and quit the processes that could be from the virus.
- Check the system for changes in its settings introduced by the Trojan and revoke such changes.
- To fully remove the Formgrabber virus, you should also go to the computer’s Registry Editor and delete from it anything that may be linked to the malware.
To get a better idea of how these steps should be performed, we advise you to read everything from the next lines.
Detailed Formgrabber Removal Instructions
One thing we recommend that you do before you start completing the guide is to disconect your computer from the web. In some cases, malware threats can communicate with their servers over the Internet and this could potentially make their removal from the system more difficult.
Step 1
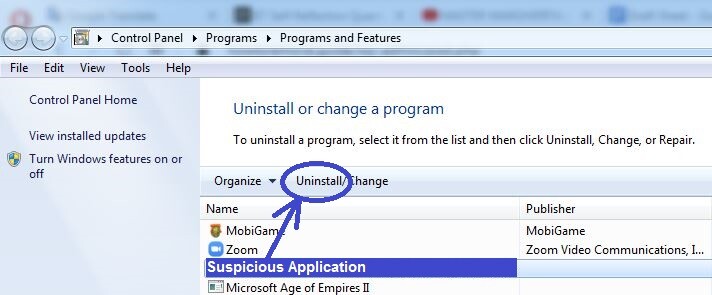
As we said above, the first important thing is to ensure that no rogue programs are present on the computer The easiest way to clean your system from potentially unwanted programs is to go to the Start Menu, click on the Control Panel icon/tile (or search for Control Panel using the search bar if you don’t see it at first), and to then select the Uninstall a Program button.
In there, you will see what programs are installed on your computer and what their installation date is. If there’s anything installed just before the Trojan Horse infection occurred, and you think that the program in question could be responsible for the malware attack, select the suspected program, then click Uninstall from the top, and complete whatever steps get shown to you in the uninstallation manager. Just make sure that you do not agree to any options that offer you to keep anything from the program on your computer.
Step 2
WARNING! READ CAREFULLY BEFORE PROCEEDING!
Next, it is time to search for hazardous processes and stop them. You can do that from the Task Manager – to open it, press Ctrl, Shift, and Esc together, and then select Processes to see the list of currently running processes.
Here, you will have to use your own discretion to figure out which of the listed items may be malicious. Look for ones with high Memory and/or CPU usage that also don’t seem to be coming from any of the normal programs that are running on your computer at the moment. Also, pay attention to the names of the different processes – don’t expect to see Formgrabber in that list but if, for instance, you see a process with an odd-looking name, you may want to further investigate it. Another possible giveaway sign is if there are two processes with very similar/nearly identical names (for instance, Chrome and Google Chrome). In such cases, it is highly likely that one of the two processes is a disguised Trojan Horse process that is attempting to remain unnoticed.
If you do come across an item that raises your suspicion, look for more information about it on the Internet – in most cases, this should let you know if the process is harmful. Just make sure that you are getting your information from reputable security forums and sites that can be trusted.
Another suggested method to check whether a process is harmful is to go to its Location folder and scan the files contained there. To do that, right-click the process, select the File Location option (the first one), and when the folder opens, scan the files in there. We can offer you a powerful online malware scanner show right below that you can use for free on our site and that requires no installation.


If you do find malware files in the location folder of the process, immediately right-click on the process and quit it by selecting the End Process option.
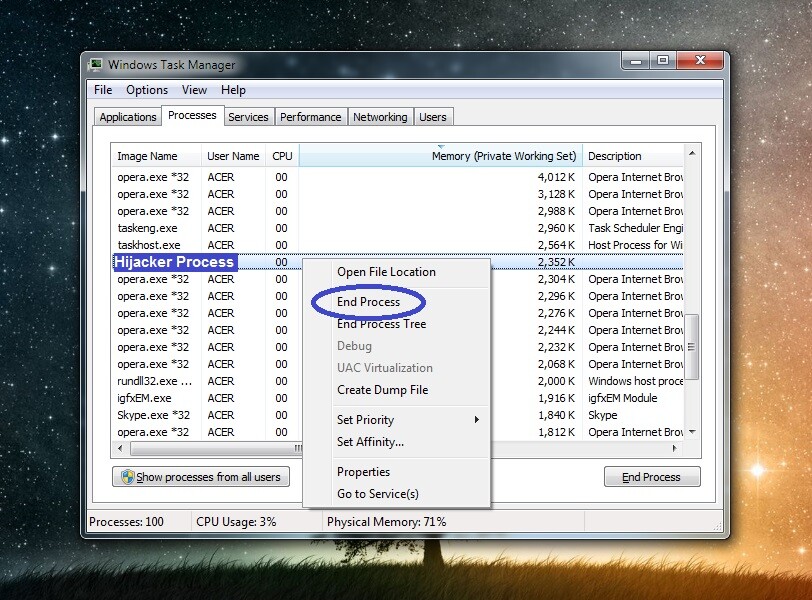
After that, make sure to delete the location folder where its files are. If you are unable to do that now because an error message shows up when you attempt the deletion, delete whatever files you can from within the folder and return to it later, once the other steps have been completed, to try to delete the folder once again.
Step 3
It is possible that Formgrabber may try to re-launch its process (or processes) – to stop it from doing that, boot your computer in Safe Mode.
Step 4
For this step, start by pressing the Winkey + R keyboard combination, which will evoke the Run window. In that window, type ncpa.cpl and then click on OK.
This will open a window with different networks icons in it – right-click the icon of the network you typically use and select Properties. In the following window, click on Internet Protocol Version 4 from the list, then select Properties again, and check the Obtain an IP address automatically and Obtain DNS server address automatically options. Following that, click on the Advanced settings button, open the DNS tab and there delete anything that may be present in the DNS server addresses list, after which click OK in each window.
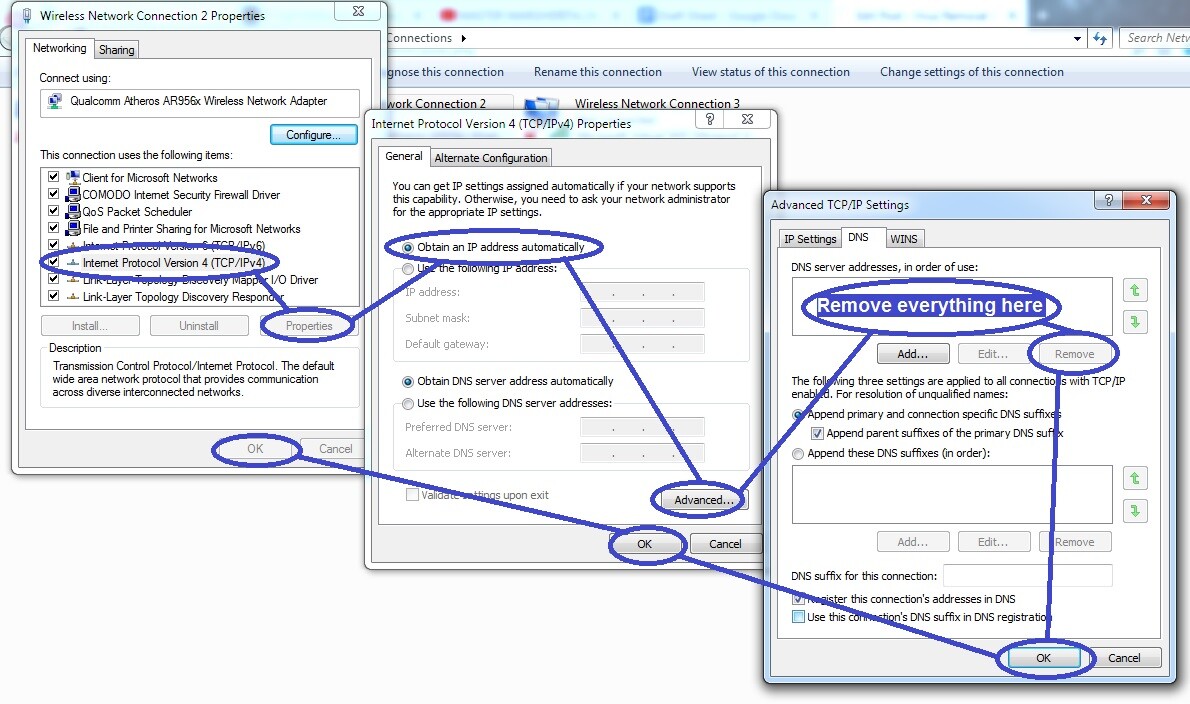
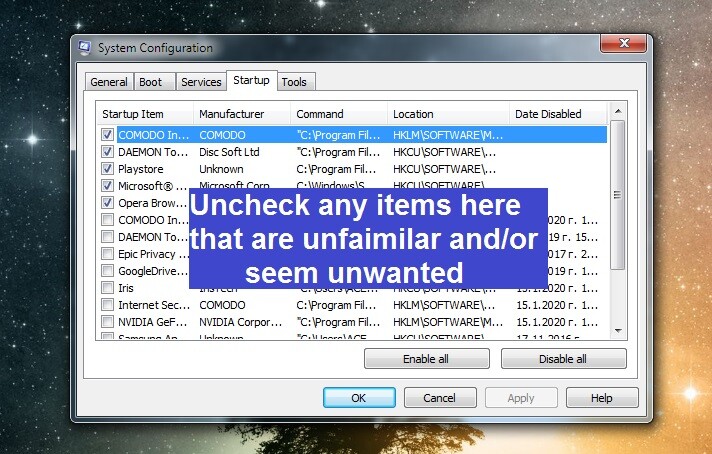
Go back to the Run window, this time type msconfig in it, and hit Enter to open the System Configuration window. In it, select Startup and if there are any questionable items or ones with unknown developers (according to the list) shown in that tab, uncheck them and click on OK.
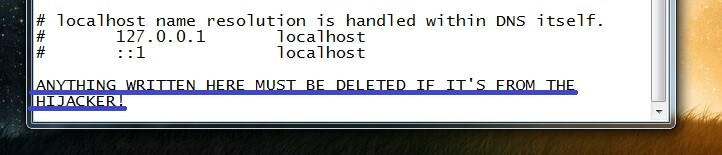
Go to the Run window yet again and copy-paste in it this line “notepad %windir%/system32/Drivers/etc/host“. Click on OK and a file named Hosts should appear in front of you. In that file, you must copy everything that may be written after “Localhost” and post it in a comment below this guide. We will look at the text from your Hosts file and tell you if anything needs to be done about it. If there was nothing after “Localhost“, then you should directly proceed to the next step.
Step 5
Now you will need to clean the system Registry – to do that, open Run as shown in the previous step, type regedit, hit Enter from the keyboard, and when you get asked for Admin confirmation (you need to be using an Admin account) click on Yes.
This should get you to the Registry Editor tool, in which you must select Edit and then Find from the menu. In the small search window that pops-up, type the name of the Trojan virus (Formgrabber) and search for related items. Even if there are multiple Formgrabber items in the Registry, the search will only show you the first one, so you must delete it and search again to find the second, third, etc., and to delete them as well.
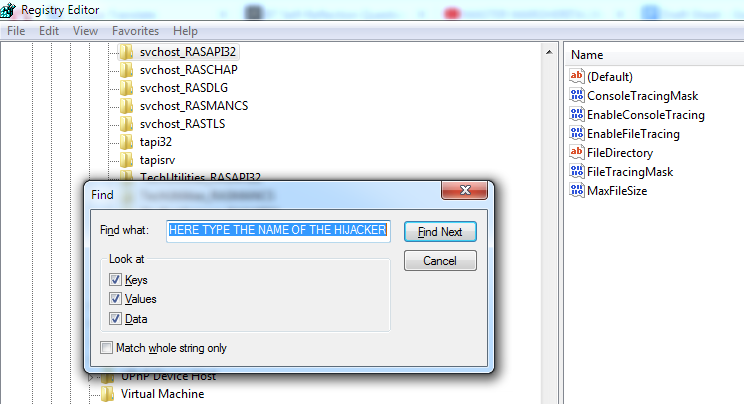
After you’ve made sure that everything from Formgrabber is deleted, use the left panel to find the following three folders:
- HKEY_CURRENT_USER/Software/Random Directory
- HKEY_CURRENT_USER/Software/Microsoft/Windows/CurrentVersion/Run
- HKEY_CURRENT_USER/Software/Microsoft/Internet Explorer/Main
Carefully look through the items/subfolders contained in them and tell us in the comments if any of them have strange names. For instance, if you see an item with a name such as this one “892ryd9j982t983e2dj984tu32r89” (or something similar), it’s probably not supposed to be there and must be deleted. However, it’s better to first ask us about any such items, because if you end up deleting something that’s not from the virus, this could lead to problems with your system.
Step 6
The Trojan Horse viruses are a very widespread category of malware, and some of the representatives of this category can be very advanced and nearly impossible to remove manually. If Formgrabber still appears to be in your system even after all the steps shown here have been completed on your computer, then it might be time to either take your machine to a professional or to use a specialized program to clean the system. The advantage of the latter option is that it has the potential to save you a large amount of time because if you use a reliable and effective anti-malware tool, your computer could get cleaned in a matter of minutes.
Therefore, in this post, we’ve included one such malware-removal tool that we recommend to our readers, especially to those of them that haven’t managed to manually delete the problematic software/malware that has been bothering them. If Formgrabber is still giving you trouble, we advise you to give this tool a go and take care of the Trojan virus with its help.

Leave a Reply