Altruistics is a crypto-mining malware that I’ve been around for over four years and is still somehow managing to infect people’s PCs and drain their resources. It’s certainly not the most harmful malware in existence, but its sheer persistence and ability to slow down your PC make it a very annoying problem that can be surprisingly difficult to get rid of.
Over the years since I first encountered this malware, it has had many reskins – other versions that basically do the same thing and are just as frustrating to eliminate. The most noteworthy among them are Altrousik and Altrsik, so if you currently have Altruistics, you may also want to check your system for these two as well.
Altruistics may expose your browser to redirects, ads, and persistent unwanted components. Install SpyHunter Pro to scan for risks, remove related threats, and enable real-time protection.
*Source of claim SH can remove it. Trial w/Credit card; image is for illustration; full terms.
Obviously, until you get rid of Altruistics, it won’t stop dragging your system resources. Additionally, its very presence in the system creates potential vulnerabilities and security risks. Therefore, I urge you to follow the detailed removal steps provided in the next guide to get rid of this malware. Alternatively, if the manual instructions seem too challenging, you can instead opt for the SpyHunter 5 removal tool, which is linked on this page.
Altruistics Removal Tutorial
To completely eliminate the Altruistics virus, you’ll need to follow a structured series of steps. Don’t worry—it’s totally manageable, and with a little patience, you’ll be able to clean your system thoroughly. Here’s an overview of what you need to do:
- Install LockHunter and reveal hidden files and folders.
- Use the Task Manager: Identify suspicious processes, trace them to their location, delete their associated files, and then terminate the processes.
- Locate and remove leftover malware files in key system directories, such as:
C:\ProgramData\Microsoft\Windows\Start Menu\Programs\StartupC:\Users\YourUsername\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup
- Clear the Task Scheduler to ensure no rogue tasks are set to relaunch malware components.
- Clean the System Registry to eliminate lingering entries tied to the virus.
These steps are outlined in detail below, but there’s one thing you should do first: Open your Start Menu, navigate to Settings > Apps, and sort your installed programs by date. Look for anything unfamiliar or suspicious – Altruistics, Altrousik, Altrsik, or anything else that was installed recently – and uninstall it. This simple action can often remove the source of the problem before you even begin the deeper cleanup.
Take your time, follow the steps carefully, and your system will be virus-free in no time.
SUMMARY:
Although I did my best to make this guide as easy to follow as possible, some users may find it a bit too advanced or time-consuming. In case you’d rather delete the virus using a quicker method, I recommend trying SpyHunter 5. This professional anti-malware tool, linked on the current page, can take care of a wide range of threats and should make quick work out of the Altruistics Trojan miner.
How to Remove the Altruistics Virus
There are two main prerequisites you must first meet before engaging with the following removal steps. Without performing these preparations, you may not be able to successfully find and delete everything that’s linked to the Altruistics malware. Here’s what to do:
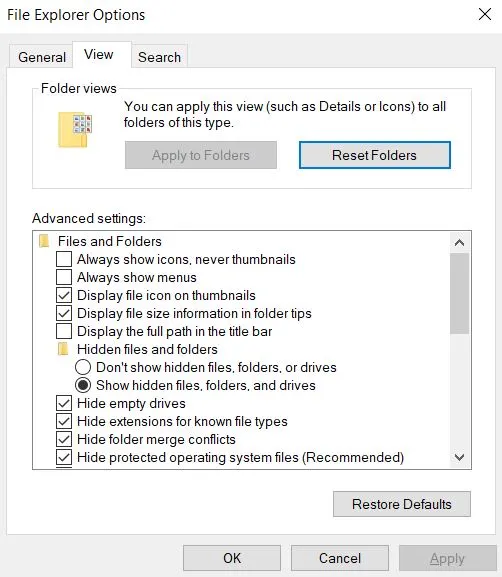
First, go to Folder Options via the Start menu, switch to the View tab, and check “Show hidden files and folders.” Save the changes by clicking OK.
Now, let’s talk about the ones that won’t budge – the ones that give you “File in use” error. That’s where LockHunter comes in—a lifesaver when dealing with files that refuse to go quietly. Install it before moving forward. Trust me, you’ll thank yourself later.
Video walkthrough for this step:
Get Rid of Altruistics Background Processes
Ever wonder why your computer feels sluggish? Malware could be quietly hogging resources in the background. Open Task Manager by hitting Ctrl + Shift + Esc. Click “More Details” if needed, then sort processes by CPU or Memory usage. See something fishy? Right-click it, choose Open File Location, and check if it’s tied to Altruistics.
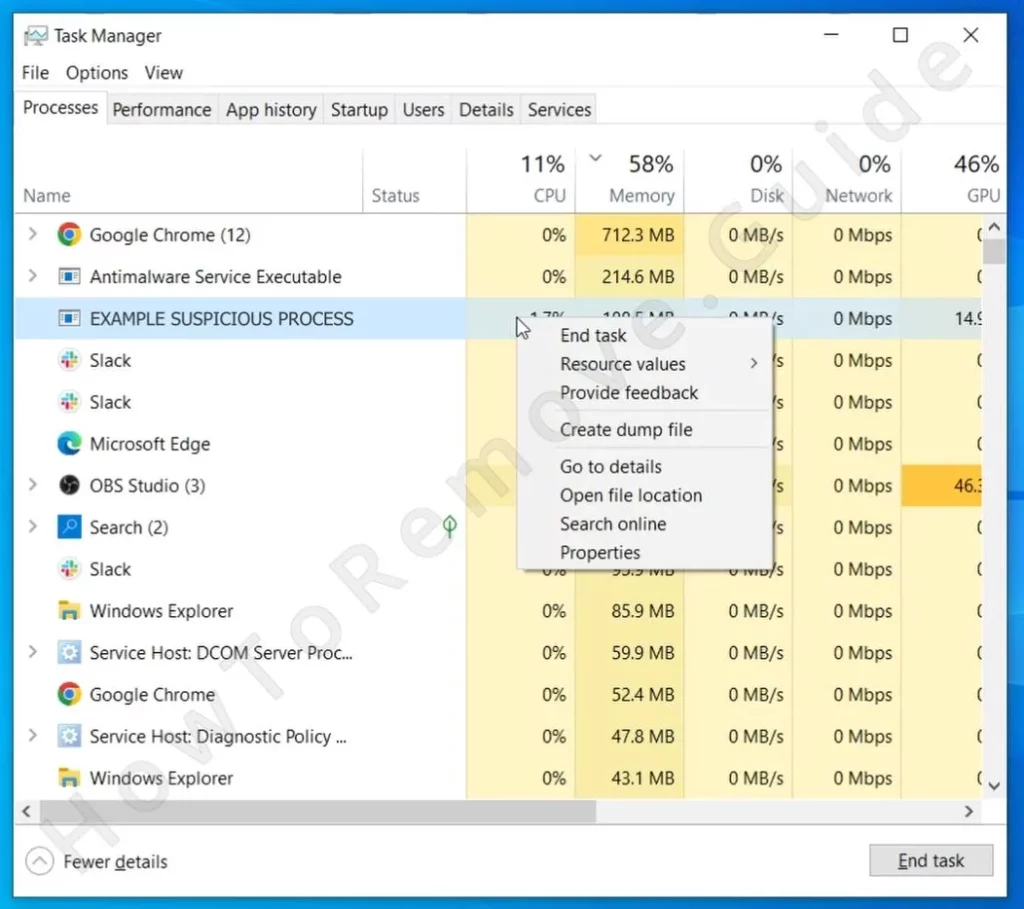
If it is, delete it. If that doesn’t work, LockHunter can lend a hand. Use it to unlock the file and delete it, then return to Task Manager and hit End Task on the same process. This ensures the malware doesn’t spring back to life.
Pro tip: If you’re unsure about a process, look it up online before deleting anything. The last thing you want is to remove something critical to your system.
Video walkthrough for this step:
Altruistics may expose your browser to redirects, ads, and persistent unwanted components. Install SpyHunter Pro to scan for risks, remove related threats, and enable real-time protection.
*Source of claim SH can remove it. Trial w/Credit card; image is for illustration; full terms.
Delete Altruistics Virus Files
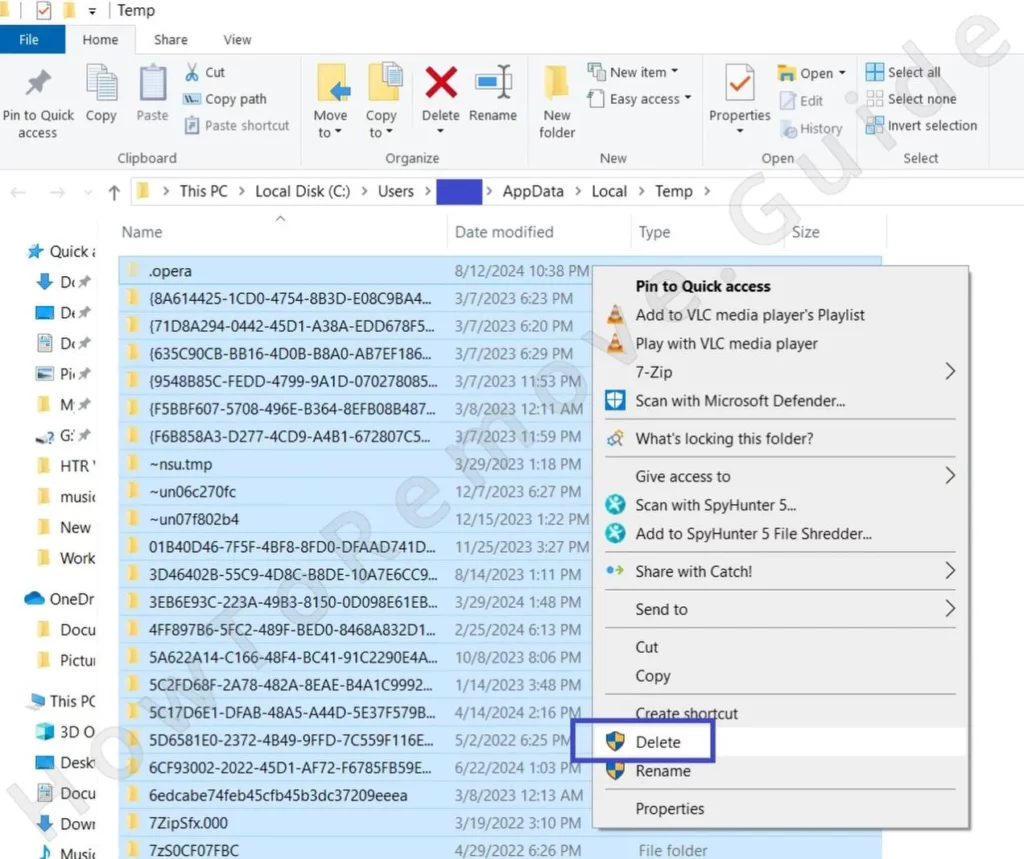
Malware like Altruistic doesn’t stop at a single folder. It spreads. Your next mission is to comb through several directories. Start with the Startup folders located at:
C:\ProgramData\Microsoft\Windows\Start Menu\Programs\StartupC:\Users\YourUsername\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup
Delete everything except desktop.ini—that one’s harmless. Next, revisit Program Files, Program Files (x86), and your AppData subfolders. Delete any folder that looks linked to Altruistics. And don’t forget the Temp folder (C:\Users\YourUsername\AppData\Local\Temp). Clear everything there, then empty your Recycle Bin to make it final.
How to Delete Persistent Files with Lock Hunter
Get Rid of Altruistics Scheduled Tasks
Here’s the thing about malware—it plans ahead. Altruistics might have set up scheduled tasks to reinstall itself or run automatically. Open Task Scheduler via the Start menu and check the Task Scheduler Library. Look closely at each task. In the Actions tab, you’ll find clues about what the task is doing.
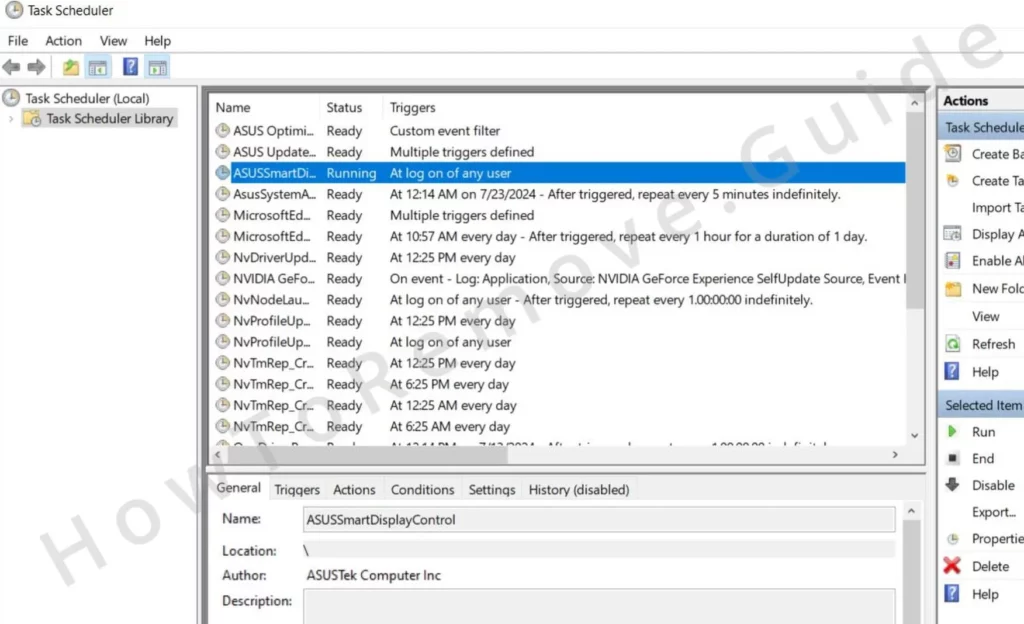
If you spot something leading back to Altruistics, delete the task and manually remove any associated files. The key is patience—missing even one malicious task can undo your progress.
Video walkthrough for this step:
Uninstall the Altruistics Malware Through the System Registry
For malware, the Registry is the last line of defense. To access it, press Win + R, type regedit, and hit Enter. Use Ctrl + F to search for entries linked to Altruistics. Found something? Delete it, then search again to ensure nothing’s left behind.
Also, manually check these keys for anything suspicious:
HKCU\Software\Microsoft\Windows\CurrentVersion\RunHKCU\Software\Microsoft\Windows\CurrentVersion\RunOnceHKLM\Software\Microsoft\Windows\CurrentVersion\RunHKLM\Software\Microsoft\Windows\CurrentVersion\RunOnceHKLM\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer\RunHKCU\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer\RunHKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunServicesHKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunServicesOnceHKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce\SetupHKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services
Only delete what you’re sure is linked to malware. Guesswork here can lead to major system issues, so proceed carefully.
Video walkthrough for this step:
Final Sweep to Remove Altruistics
If you want to ensure Altruistics is gone for good, there’s one last step to take. Think of this as a final cleanup to catch anything that might have slipped through the cracks. Keep in mind, that this won’t prevent the service from recreating files if you haven’t already followed the earlier steps. But if there are any remnants left behind, this should take care of them.
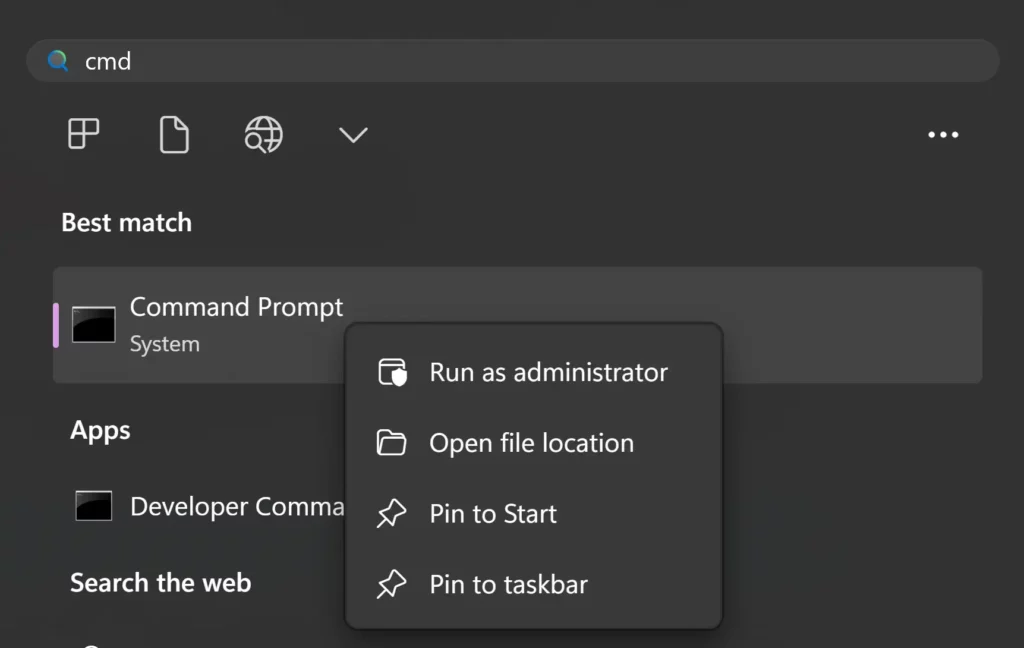
First, press the Win key and type cmd. When the Command Prompt appears in the search results, right-click it and select Run as administrator.
Next, type the following command exactly as shown:sc delete altruistics
Hit Enter to run the command. If successful, you’ll see a confirmation message letting you know the service was found and deleted. If nothing is found, don’t worry—that’s actually good news. It just means your earlier efforts have already removed the service.
Finally, restart your computer to finalize the changes. A reboot ensures nothing from Altruistics is still lingering in your system’s memory. Over the next few days, keep an eye on your system. If any unusual behavior continues, consider using a professional tool like SpyHunter 5 to double-check and give you peace of mind.
How to check if Altruistics is removed completely
At this point, you should feel good enough to stop. BUT! There is the possibility Altruistics has downloaded and installed something else on your PC. We recommend restarting your PC, then opening the Task Manager again.
Look for other processes you may have missed. A good way to gauge this is in the Details Tab.

Arrange the processes by User Name.
The reason you want to do this is so that anything with your user name is displayed, together with its description on the right. This makes it relatively easy to spot fishy processes. If you find any, right-click them and delete them like you did earlier in the guide.
When Manual Efforts Aren’t Enough
Sometimes, no matter how thorough you are, malware persists. That’s when it’s time to call in reinforcements. Anti-malware tools like SpyHunter 5 are designed to handle what manual methods can’t. Think of them as professional exterminators for your system.
Run a full system scan and let the software do the heavy lifting. This ensures no remnants of Altruistics are left behind, giving you peace of mind.
Securing Your System for the Future
Congratulations—you’ve cleared your system! But the best defense is a good offense. Keep your operating system and applications updated to patch vulnerabilities. Be cautious with downloads and links. If something feels off, trust your instincts and avoid it.
Invest in reliable antivirus software with real-time protection. It acts as a digital security guard, catching threats before they can do harm. And don’t forget to back up your data regularly. Whether you use an external drive or cloud storage, backups are your safety net against both malware and hardware failure.
The Finish Line: A Safer, Stronger System
By following these steps, you’ve not only removed Altruistics but also fortified your system against future attacks. Digital hygiene isn’t a one-time task—it’s a habit. Keep your system clean, stay vigilant online, and you’ll enjoy a faster, safer computing experience.
Great job taking control of your system—you’re on your way to becoming a digital security pro!


Leave a Reply