*Source of claim SH can remove it.
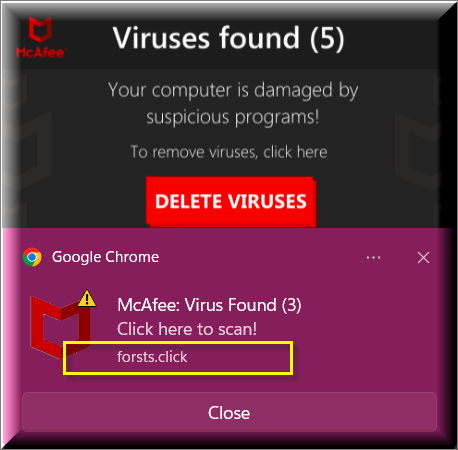
Forsts.click mcafee
Forsts.click mcafee is a browser hijacker that uses fake notifications and pop-ups to make you believe Mcafee has discovered viruses on your system. Forsts.click mcafee uses fraudelent methods to trick the affected users into downloading additional suspicious software.
In other words, this piece of potentially unwanted software is a tool for the online promotion of different types of content, sites, products, services, and more. Its main goal is to generate as much profit as possible by implementing the infamous Pay-Per-View and Pay-Per-Click methods. This app isn’t intended to damage your computer so there’s no need to get panicked at the sight of the unwanted changes that it has made inside your Firefox, Chrome, Edge, or another browser.
Keeping Forsts.click on your computer for long periods of time is not recommended because it doesn’t give you any control over the frequency and content behind its ads. You may end up getting Forsts.click advertising messages that are linked to less-than-reliable web locations without your permission.
Needless to say, this could potentially get you exposed to more serious software threats which is why it is always better to simply rid your computer of such browser hijackers as soon as you realize that they have been added to your browser.
Forsts.click
Forsts.click is a browser-redirecting software that “steals” the homepage, toolbar, and search engine of the user’s browser and forces them to reroute the user’s traffic. Forsts.click also monitors your online history to determine your interests and customize its ads accordingly.
How dangerous is Forsts.click? The answer to this question entirely depends on what content this app advertises within your browser. If the ads it shows are legit and the sites it tries to redirect you to are not harmful, then this app would be little more than a mere annoyance inside your browser. However, there is no guarantee that you will always get legitimate offers that won’t be linked to unsafe content or that all the sites Forsts.click reroutes you to would be legitimate. Unfortunately, this means that the very presence of this software on your machine increases the chance of landing some dangerous malware threat such as a Trojan Horse. If such a malicious program enters your computer, it could take over the whole system, corrupt your data, and even download additional threats such as Spyware or Ransomware. In other words, though Forsts.click is not damaging in itself, it can indirectly cause lots of security problems. Obviously, the proper solution here would be to make sure that this undesirable app gets uninstalled as soon as possible.
What is Forsts.click?
Forsts.click is a potentially unwanted app categorized as a browser hijacker – it can “steal” the settings of your browser and start spamming you with aggressive advertisements and page redirects. In some cases, the presence of Forsts.click in your browser could lead to security issues.
The main red flags indicating that there could be a browser hijacker such as Forsts.click in the computer are the constant generation of obstructive ads, pop-ups, pop-unders, and page redirects in the browser and unwanted changes to certain browser settings such as the default starting page or search engine. If you’ve noticed anything like that happening in your browser, chances are that a browser hijacker has been attached to it without your knowledge. If Forsts.clickis indeed on your computer, attached to your browser, the best advice we could give you is to follow the instructions you will find on the current page to delete the unwanted app before it has caused any serious problems.
The Forsts.click Virus
Forsts.click virus is not very dangerous because it cannot directly harm the user’s computer or the data stored there. However, the Forsts.click virus can still potentially expose your system to danger if you allow it to stay in the browser and spam you with its ads.
If one or more of your browsers have the Forsts.click hijacker added to them, you must make sure to delete the undesirable software. In addition to the changes it is likely to make in your browser, this unwanted app will also likely spam you with sudden redirects to questionable sites and put aggressive ads on your screen. This could, in turn, lead to the exposure of your PC to a variety of malware dangers such as Trojan Horse viruses, Ransomware, and Spyware. Another very common risk associated with the ads displayed by browser hijackers is the potential for having your browser rerouted to scam sites designed to trick you into providing personal data, including credit or debit card numbers.
Dealing with Forsts.click
The instructions from down below will allow you to promptly remove this hijacker and make sure it no longer has control over your browser. However, it is also important to remember to keep similar apps (McAfee virus popup) away from your system in the days to come. Obviously, staying away from sketchy web content, spam emails, clickbait ads, and questionable file-sharing sites is important in order to keep your PC safe and clean. However, something lots of users forget about is to check the settings of the setup wizards of programs that they are about to install. Oftentimes, even legitimate software would have some unwanted elements such as a browser hijacker added to its installer that gets installed by default alongside the main program. You could, however, prevent this from happening by simply unchecking the added component from within the setup settings before you launch the installation. Do this every time from now on with bonus features in installers that you don’t think are needed or wanted and you will greatly decrease the chances of getting another hijacker in the future.
SUMMARY:
| Name | Forsts.click |
| Type | Browser Hijacker |
| Danger Level | Medium (nowhere near threats like Ransomware, but still a security risk) |
| Symptoms | Users who have hijackers inside their browsers complain from constant page-redirects that occur automatically, aggressive ads in every browser tab, and changes in important browser elements such as the toolbar or homepage. |
| Distribution Method | The main method used to spread these undesirable apps is the use of third-party apps that carry the hijacker as a “bonus” feature. |
| Detection Tool |
*Source of claim SH can remove it.
Remove Forsts.click
To try and remove Forsts.click quickly you can try this:
- Go to your browser’s settings and select More Tools (or Add-ons, depending on your browser).
- Then click on the Extensions tab.
- Look for the Forsts.click extension (as well as any other unfamiliar ones).
- Remove Forsts.click by clicking on the Trash Bin icon next to its name.
- Confirm and get rid of Forsts.click and any other suspicious items.
If this does not work as described please follow our more detailed Forsts.click removal guide below.
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Source of claim SH can remove it.
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab (the “Details” Tab on Win 8 and 10). Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold together the Start Key and R. Type appwiz.cpl –> OK.

You are now in the Control Panel. Look for suspicious entries. Uninstall it/them.
Type msconfig in the search field and hit enter. A window will pop-up:

Startup —> Uncheck entries that have “Unknown” as Manufacturer or otherwise look suspicious.

*Source of claim SH can remove it.
Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Open the start menu and search for Network Connections (On Windows 10 you just write it after clicking the Windows button), press enter.
- Right-click on the Network Adapter you are using —> Properties —> Internet Protocol Version 4 (ICP/IP), click Properties.
- The DNS line should be set to Obtain DNS server automatically. If it is not, set it yourself.
- Click on Advanced —> the DNS tab. Remove everything here (if there is something) —> OK.


- After you complete this step, the threat will be gone from your browsers. Finish the next step as well or it may reappear on a system reboot.
Right click on the browser’s shortcut —> Properties.
NOTE: We are showing Google Chrome, but you can do this for Firefox and IE (or Edge).

Properties —–> Shortcut. In Target, remove everything after .exe.

![]() Remove Mybetterck from Internet Explorer:
Remove Mybetterck from Internet Explorer:
Open IE, click ![]() —–> Manage Add-ons.
—–> Manage Add-ons.
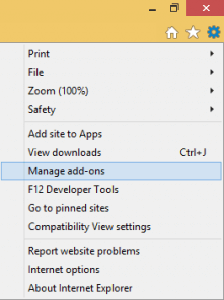
Find the threat —> Disable. Go to ![]() —–> Internet Options —> change the URL to whatever you use (if hijacked) —> Apply.
—–> Internet Options —> change the URL to whatever you use (if hijacked) —> Apply.
 Remove Mybetterck from Firefox:
Remove Mybetterck from Firefox:
Open Firefox, click ![]() ——-> Add-ons —-> Extensions.
——-> Add-ons —-> Extensions.

 Remove Mybetterck from Chrome:
Remove Mybetterck from Chrome:
Close Chrome. Navigate to:
C:/Users/!!!!USER NAME!!!!/AppData/Local/Google/Chrome/User Data. There is a Folder called “Default” inside:
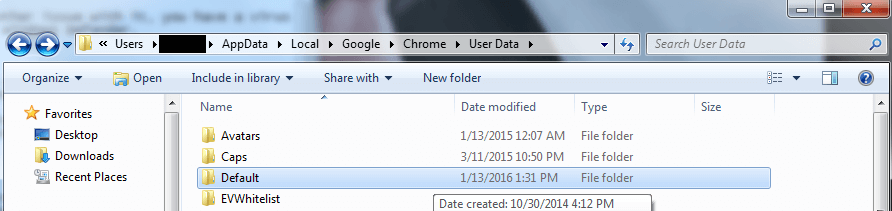
Rename it to Backup Default. Restart Chrome.

Type Regedit in the windows search field and press Enter.
Inside, press CTRL and F together and type the threat’s Name. Right click and delete any entries you find with a similar name. If they don’t show up this way, go manually to these directories and delete/uninstall them:
- HKEY_CURRENT_USER—-Software—–Random Directory. It could be any one of them – ask us if you can’t discern which ones are malicious.
HKEY_CURRENT_USER—-Software—Microsoft—-Windows—CurrentVersion—Run– Random
HKEY_CURRENT_USER—-Software—Microsoft—Internet Explorer—-Main—- Random
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment