This article will help you remove the Hummingbird Android Malware from your device. Inside, you’ll also find useful information about what exactly is HummingWhale Malware, how dangerous it is and what steps you can take to prevent future infections.
HummingWhale is an Android Malware that has been recently discovered by researchers. Even though the software in question has been released fairly recently, it has already infected a significant amount of devices. HummingWhale is the successor of the HummingBird malware rootkit for Android devices and it shares similar traits with it. However, the malware we will be focusing on here is more evolved and improved in comparison to its predecessor which means that it has the potential to cause even more trouble to users that have fallen prey to it. In the following article, you will be given information regarding what it actually does once it infects somebody’s smartphone, how it works once inside and what methods of distribution are employed to spread this nasty piece of software.
Characteristics of the Android malware
Once the malware gets installed onto the user’s device, it launches a background process which issues monitoring sessions on the smartphone every 10 seconds until a set of conditions has been met. One of the main conditions is a connection to the internet. When all the aforementioned conditions are met, the main malware process is triggered which results in the generation and display of banners that cover the whole screen of the device and promote other sketchy apps. Any attempts to close those nagging banners/ads would be in vain since a tap on their close button would either result in a redirect to some shady website or the popping-up of an installation button for the previously advertised app.
Sometimes an application that is promoted within the banner might directly get installed should the user tap onto the obstructive advert in an attempt to remove it, which is why we strongly advise you to avoid doing that regardless of how invasive the advertising materials might get.
How dangerous could it be?
So far, the creators of this piece of malware have been primarily using this unwanted software as means of gaining revenue through the pay-per-click scheme. Each ad that gets tapped upon results in a small amount of money being gained by the developers of the software. However, since a huge number of devices are getting infected each day and at least some of the users would tap onto the obnoxious banners, the end result is that the total amount of income is actually quite substantial. On its own, this is not all that harmful to a device nor the online security of the affected user. However, the mere fact that HummingWhale is so effective at getting installed on so many smartphones and eventually compromising their systems means that should someone decide to use the malware for a more harmful task, they would have no difficulty whatsoever at implementing this new priority into the application’s functions. Therefore, all users that have gotten their Android device infected by the nasty app are strongly advised to see to its removal ASAP or else their virtual safety and security might be compromised. We can help you remove the problematic app with our removal manual that you can find at the bottom of this article.
Methods of installation and precaution tips for future protection
The main method used for the installation of malware on Android smartphones/tablets is via the help of another application that appears to be safe on the outside. Most of the times, HummingWhale is implemented within the said application and gets installed along with it without the user knowing about it. Usually, applications that might potentially compromise the security of the device are not allowed into Google Store. However, when it comes to HummingWhale, it has been reported that a number of applications in the Store have had the malware inside them. So far, Google seems to have managed to remove those apps but one can ever be one hundred percent sure.
Here, we will give you a brief list of rules to help you avoid landing the malware on your device. Be sure to read them carefully and use them from now on.
- Unless you are absolutely sure about the safety of an application outside of Google Store, do not download it. Generally, it is not advisable to install software that comes from outside Play Store since the chance of getting some sketchy and potentially harmful piece of software drastically increases that way.
- Avoid visiting websites that look suspicious while surfing the internet on your phone. Any site that has way too many big and obstructive banners should be avoided at all costs!
- Even when installing something from the Google Store, take a few moments to look at its rating and read some of the user reviews. As we already made it clear, malware the likes of HummingWhale is perfectly capable of making it inside the Store. Additionally, it has been reported that this particular malware also tends to conduct false reputation and rating via fake comments and upvotes issued through devices that have already been infected by it. Therefore, as an additional precaution, it is always a good idea to look-up less known products and see what results come up after you search for their name online.
Here is also a list from of the apps that have been reported to serve as carriers for the HummingWhale infection so that you know to avoid them:
com.bird.sky.whalecamera – Whale Camera
com.op.blinkingcamera – Blinking Camera
com.fishing.when.orangecamera – Orange Camera
com.note.ocean.camera – Ocean camera
io.zhuozhuo.snail.android_snails -蜗牛手游加速器-专业的vpn,解决手游卡顿延迟问题
com.cm.hiporn – HiPorn
com.family.cleaner – Cleaner: Safe and Fast
com.wall.fast.cleaner – Fast Cleaner
com.blue.deep.cleaner – Deep Cleaner
com.color.rainbow.camera – Rainbow Camera
com.ogteam.love.flashlight – com.qti.atfwd.core
com.wall.good.clevercamera – Clever Camera
com.well.hot.cleaner – Hot Cleaner
com.op.smart.albums – SmartAlbums
com.tree.tiny.cleaner – Tiny Cleaner
com.speed.top – Topspeed Test2
com.fish.when.orangecamera – Orange Camera
com.flappy.game.cat – FlappyCat
com.just.parrot.album – com.qti.atfwd.core
com.ogteam.elephanta.album – Elephant Album
gorer – File Explorer
com.with.swan.camera – Swan Camera
com.touch.smile.camera – Smile Camera
com.air.cra.wars – com.qti.atfwd.core
com.room.wow.camera – Wow Camera-Beauty,Collage,Edit
com.start.super.speedtest – com.qti.atfwd.core
com.best.shell.camera – Shell Camera
com.ogteam.birds.album – com.qti.atfwd.core
com.tec.file.master – File Master
com.bird.sky.whale.camera – Whale Camera
cm.com.hipornv2 – HiPorn
com.wind.coco.camera – Coco Camera
global.fm.filesexplorer – file explorer
com.filter.sweet.camera – Sweet Camera
com.op.blinking.camera – Blinking Camera
com.mag.art.camera – Art camera
com.cool.ice.camera – Ice Camera
com.group.hotcamera – Hot Camera
com.more.light.vpn – Light VPN-Fast, Safe,Free
com.win.paper.gcamera – Beauty Camera
com.bunny.h5game.parkour – Easter Rush
com.fun.happy.camera- Happy Camera
com.like.coral.album – com.qti.atfwd.core
com.use.clever.camera – Clever Camera
com.wall.good.clever.camera – Clever Camera
HummingWhale Malware Android Removal
Method one
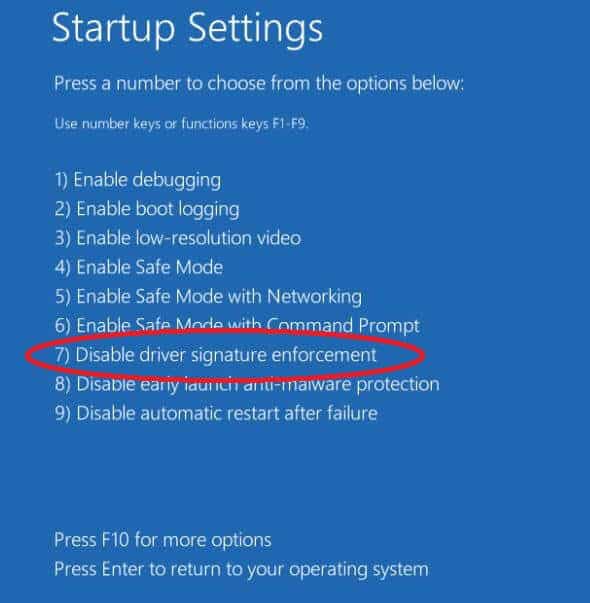
To start off need to reboot your Android device in safe mode.
To do that hold the power button on your Android phone until you see the turn off button on your screen. Press and hold the button until you get a prompt that will allow you to reboot in safe mode.
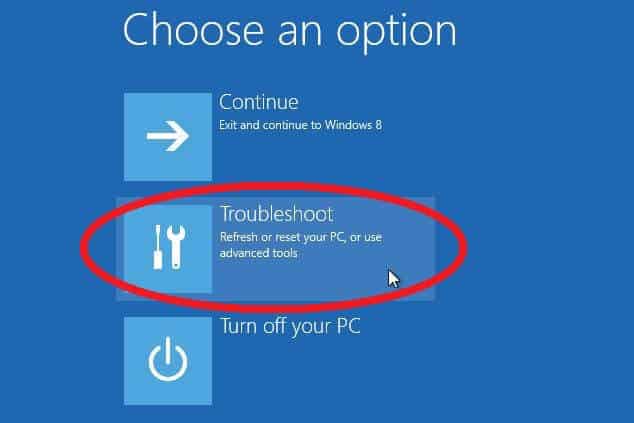
You should now see Safe mode written on the bottom of your screen. If that is the case proceed with step 2.
What to do if the instructions above didn’t work to turn on safe mode:
The malware may be blocking the software option to turn on safe mode. To bypass the block you can use the hard safe mode reset.
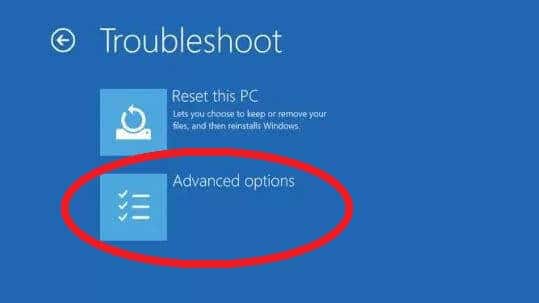
Press and continuously hold the Volume Down and the Power Button until the phone turns off and reboots. Some devices require that you hold both buttons until the device fully reboots, other devices may require that you only hold the power down key. If your Android device is a particularly old one you may have to hold Volute Down, Volume Up and the power key until it reboots into Safe Mode.
Try all the combinations in the order we’ve written them until you get the proper one for your device.
Locating and uninstalling the malware infected application is next on the list. As a rule of the thumb you are looking for a recently installed application that will most probably not be present in the Google Play Store list of installed applications, but will be present on the device itself.
Navigate to Settings->Applications->Installed Apps and look for suspicious entries there. It could be anything, but the most likely culprit is an app whose name you don’t recognize and don’t remember installing yourself, or two entries of what appear to be the same app.
- Any app you downloading and installed without the assistance of the Google Play Store is an immediate suspect and you should uninstall it immediately.
To uninstall an app just tap on it, then click on the Clear Cache, Clear Data and Uninstall buttons, in that order.
When you are done cleaning suspicious apps remember to reboot your Android device in order to turn off Safe Mode. If the malware symptoms persist then you need to repeat this step again and perform a more throughout app pruning.
Method two
If you were unable to locate and uninstall the malware using the instructions above, then there is one last method you can use in order to clean your device – a Factory Reset.
- IMPORTANT! A factory reset will wipe your phone clean of any contacts, apps, settings and files you have on it! Back up everything important by uploading in to your PC or with the help of a cloud service! The Android backup service will back-up service can be of great help too!
- EVEN MORE IMPORTANT! Resetting your phone is always done at your own risk and may void the warranty of the phone with some distributors. Make sure your device has sufficient battery strength to finish the operation or keep it plugged in.
Try this first: Perform a factory reset using the settings menu
- Begin by opening Settings .
- Located under “Personal,” tap Backup & reset. You’ll probably have to input your PIN or password, if you have set up one.
- Find the Factory data reset button, under Personal Data. Read the instructions and press Reset phone.
- For best results select Erase everything.
- When the reset is ready reboot your device.
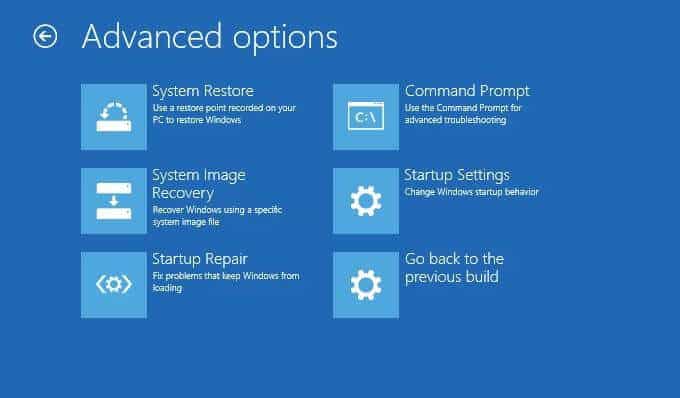
Try this if the above didn’t work: Reset device in Recovery mode
- Important! Android devices using Android version 5.1 and later are protected from theft and subsequent hard reset by requiring the user to enter his Google account name and password. Make sure you know what they are before attempting the reset.
- Turn off your phone
- Press and hold Volume up and Power button at the same time until you see the logo of the manufacturer and the device is turned on.
- Immediately press Volume down in order to select “Recovery mode.” You can navigate through the menus by clicking on Volume up button and confirm your choice with Volume down button.
- The Android robot will appear with a “No command” Message.
- While you hold down the Power button, press the Volume up button, then release it..
- Again you need to use the volume buttons to select the “wipe data/factory reset” and confirm your pick by pressing the Power button.
- Confirm the reset to exit the menu and begin the process itself.
Once the factory reset is complete your phone will reboot itself and it will be free of any third party applications, files and settings. Use your backups to restore your device and keep away from dangerous sites in the future!
If you run into any trouble – ask us for help in the comments section!

Hello and thank youfor the article. Even as i am writting this the virus keeps closing the page. Well im not sure which virus i do have but the o e you described above sounds like its it. My problem is that is has gotten so deep into my tablet and phones that it has created its own set of rules and only reboots from there i have downloaded all sorts of bootloaders and diffrent things and it has takenover i am exsocited to the bone please help. It even llo.s like im seeing my tablet thru a mirror another divice.
Did you try using the guide’s instructions. Remember that when trying to remove the unwanted software, you should do it from Safe Mode as this should prevent the unwanted software piece from operating and from disrupting you.