*Jzie is a variant of Stop/DJVU. Source of claim SH can remove it.
Jzie File
There is a rising number of users reaching out to us with issues related to the Jzie file. Most of them report that when they attempt to access a document or another file on their system, they encounter an unexpected Jzie file format, which cannot be recognized by the system. This unfortunate event signifies a ransomware attack. If you have also been faced with the same issue, then most probably an insidious ransomware has encrypted your files, rendering them unreadable to your system. As a result, you have end up with a bunch of useless data (including but not limited to pictures, official documents, videos, and audio files) that cannot be opened or used with any program without the application of a decryption key.
If you want to decrypt Jzie ransomware files, your initial move should be to disconnect the infected device from the internet. The identification of the exact ransomware variant is crucial to the decoding process since the approach to decryption varies across the different ransomware strains. Next, search online in trusted cybersecurity forums and websites to discover solutions for file decryption, and seek out tools or keys specifically designed to counteract your specific ransomware variant. Exercising caution while downloading and executing these tools, coupled with strict adherence to the provided instructions, may increase your chances of successful decryption.
To remove Jzie ransomware virus and restore your files, start with disconnecting the internet connection of the infected computer. Next, perform a comprehensive scan of your system with a reliable antivirus program and locate and eradicate the harmful software. Once the system is ransomware-free, resort to backup files stored on external devices or cloud services for file restoration. If there are no file backup sources, consider seeking help from professional data recovery services or cybersecurity experts.
Jzie Virus
The Jzie virus is a notorious variant of ransomware engineered by cybercriminals. The primary goal of this virus is to encrypt valuable user files and demand a ransom for their release. Threats like the Jzie virus find their way into systems via various distribution channels, such as spam messages, torrents, cracked software installers, harmful attachments in instant messaging or emails, malicious advertisements, and Trojan viruses. Regardless of the infection pathway, the ransomware starts its malicious work immediately upon infiltrating the system. It identifies and encrypts your most frequently used files, leaving you with an alarming ransom demand in the form of a text file or an on-screen notification.

Jzie
As a new and sophisticated ransomware infection, Jzie, Yzqe or Yzaq is designed to restrict access to your files and demand a ransom for their release. Typical operations of ransomware like this one involve placing complex encryption on your most frequently used files and displaying a ransom demand on your screen. The victims may be given a short deadline to comply with the ransom demand and if they don’t, they are threatened to never recover the encrypted files. While all ransomware operates on a similar principle of demanding money for reversing the done damage, there are alternative solutions to recover your files and remove Jzie without paying the ransom. The removal guide that you will find below provides some of these alternatives.
.Jzie
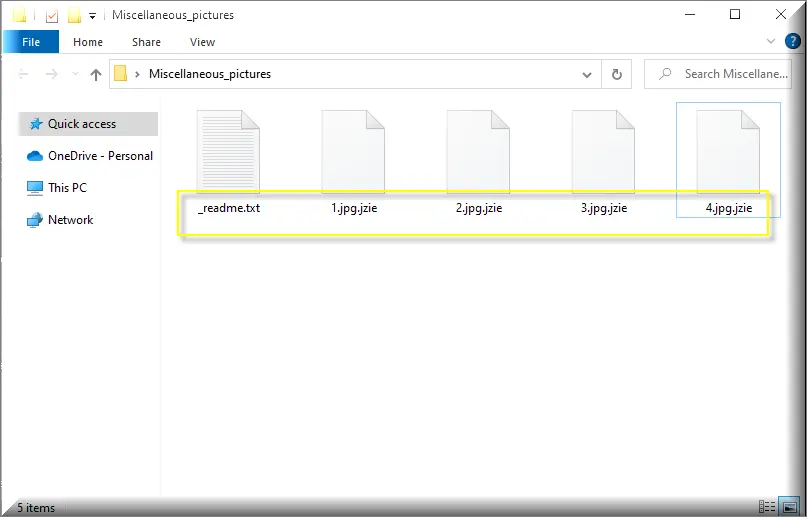
The .Jzie file extension is a special file extension that no installed software can recognize. If you notice this extension attached to your files, it signals a ransomware attack. The .Jzie extension is typically added to the name of the files but this isn’t merely a name change; it represents a significant transformation at the core of your files which renders them unreadable by your system and useless to you. The ransomware that has compromised your computer has essentially rewritten the foundational structure of your files, and only the corresponding decryption key can undo this process and bring the files that are affected to their normal state.
Jzie Extension
The Jzie extension is not a regular extension that can be easily converted, changed or removed in the same manner that you would normally do with other file extensions and formats. It signifies a deep-seated change brought on by a ransomware encryption and cannot be reversed without the right decryption key. For this reason, tampering with the Jzie extension without being equipped with the proper knowledge or professional ransomware decryption software could potentially make things worse and add more damage to the affected files. So it’s recommended to approach encrypted files with caution and seek reliable decryption solutions or professional software.
Jzie Ransomware
Unlike other malicious types of software which can be extremely hard to remove from a system, a threat like the Jzie ransomware can be eliminated with a proper manual removal guide or a reliable antimalware program. However, the removal of the threat doesn’t automatically equate to the restoration of your files. You may need additional help, like personal backups, system files extraction or professional in order to get your files back to their unencrypted state. It’s important, however, not to bend over to the demands of the Jzie ransomware operators, who are audacious enough to infect your system and then demand payment for file recovery. Refraining from paying the ransom is crucial, as this discourages the criminals from victimizing others.
What is Jzie File?
An Jzie file is essentially a regular file on your computer that has been subjected to encryption by the Jzie ransomware. This file could be a beloved photo of yours, a video or audio, or an important work document, but the file is essentially locked away by the ransomware and cannot be opened or used by your system or any software that you have installed on it. Contrary to what one might think, the Jzie file isn’t inherently dangerous; it doesn’t propagate the infection or harm your system further. It is merely a file trapped in the grips of a complex encryption algorithm, awaiting the proper decryption solution in order to be released.
SUMMARY:
| Name | Jzie |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Detection Tool |
*Jzie is a variant of Stop/DJVU. Source of claim SH can remove it.
Jzie Ransomware Removal

We suggest that you bookmark this page in your browser’s Favorites so that you can keep it and use it until you complete all the steps from the ransomware removal guide.
Next, you should restart the computer that has been infected with the Jzie ransomware in Safe Mode (see this link for how to do this). Safe Mode will make sure that only the most basic programs and processes are running on your computer. In this way, you should be able to find and stop the Jzie-related processes more quickly.
After you restart the system as explained above, click the Start menu and type “msconfig” into the search field. Then press Enter. You will see System Configuration on the screen after you do this. Check the list of items that start up when you start your computer to see if any of them are linked to the malware by going to the Startup tab.

If there are entries on your computer that have Unknown Manufacturers, strange-looking names, or otherwise can’t be linked to any legitimate programs that you normally run on your computer, you need to research them online. If you find enough reliable information that they are dangerous, the best thing to do is check off the relevant box for them in order to disable them.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Jzie is a variant of Stop/DJVU. Source of claim SH can remove it.
In the next step, look for malicious Jzie processes that are running on the computer. This can be done in the Task Manager window that shows up when you press CTRL + SHIFT + ESC. In it, click the Processes Tab to see if there are any suspicious processes running in the background. Look at the CPU and Memory Use columns and by looking at their names.
Right-click on any process that looks dangerous and choose Open File Location from the menu that pops up.

After that, you can use the virus scanner below to check the files in your File Location folder for malware.

End the process whose files were found to be harmful by the scanner. Then, remove those files and their directories from the computer.

Using the Windows Key and R key on the keyboard, start a Run command window. Then, copy the following line:
notepad %windir%/system32/Drivers/etc/hosts
After you copy the line, click OK. Find Localhost in the text of the Hosts file that appears on the screen. If your computer has been hacked, you’ll see a bunch of IP addresses at the bottom of your file under Localhost that look strange, just as seen in the sample image below.

If there’s anything suspicious in your Host file, leave us a comment below this article. If we find something disturbing, we’ll let you know what to do and how to fix it.

*Jzie is a variant of Stop/DJVU. Source of claim SH can remove it.
When a system is compromised, malicious entries can be added in the registry without the victim’s knowledge. This makes it hard to get rid of ransomware threats like Jzie. If there are files in your computer’s registry that need to be removed, in the next paragraphs, you will learn how to search for them.
First, type Regedit in the Windows search bar and hit Enter on the keyboard. The Registry Editor will appear on the screen. Use CTRL and F to search for entries that are related to the virus. Type the ransomware’s name into the Find box that pops up and click the Find Next button.
Don’t delete files and directories that aren’t linked to Jzie because doing so could damage your operating system. It is better to use a professional removal tool, like the one on this page, to avoid any damage to your computer. This program is good at finding and removing malware from places like the registry that are very important to your computer.
In the search bar at the bottom of the Start menu, type in each of the lines listed below and press Enter to open them one by one:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Look for files and folders with strange names that were added around the time of the ransomware attack in each location. If you think something should be removed, carefully research it or use a powerful scanner to help you decide on your action.
When you go to Temp, select everything in that folder and then delete it. This will get rid of any temporary files that the ransomware has added on your computer.

How to Decrypt Jzie files
Ransomware viruses are notorious for making it hard to get your encrypted data back, so you might need to use a number of different methods to decrypt some of your information. One of the first things that you need to figure out, however, is what variant of ransomware has attacked you, and, based on that, you will have to decide on your available file-recovery alternatives. The quickest way to do that is by looking at the extensions of the files that have been encrypted.
New Djvu ransomware
STOP Djvu, the most recent variant of the Djvu ransomware strain, encrypts data by attaching the .Jzie suffix to the encoded files. So, if you’ve been attacked by this latest variant, check out the suffix of your files. The good news is that, at the time of this writing, it is possible to decrypt files that have been encrypted with an offline key. So, if you want to get your data back, you can check out the link below for a file-decrypting program that might be able to do that:
https://www.emsisoft.com/ransomware-decryption-tools/stop-djvu
Follow the link above and choose “Download” to get the STOPDjvu.exe decryptor.
After the file has been downloaded, select “Run as Administrator” and then press the Yes button to start the app. You can start decrypting your data after you read the license agreement and a few short instructions. Please be aware that this tool may not be able to decrypt files that have been encrypted with unknown offline keys or online encryption.
If you want to get rid of Jzie and other infections, it is recommended to use professional anti-virus software, like the one on this site. You need to remove the ransomware prior to attempting any data recovery methods. You can use the anti-virus software on this page or the free online virus scanner for more help. It’s also okay to ask a question in the comments below.

I need a decryption tool for jzie ransom ware if you can help me on that
Hi Omar M. Rashed,
on Step 5 there is a decryptor that can help you.