The LockFile Ransomware
One of the latest variants of ransomware known as LockFile uses a unique method dubbed “intermittent encryption” to avoid ransomware protection software.
A recent research uncovered two major vulnerabilities, tracked as ProxyShell and PetitPotam, which ransomware operators are using to manipulate Windows servers and distribute file-encrypting malware that scrambles every other 16-byte chunk of a file, helping it to avoid detection.
Sophos head of engineering Mark Loman said that partial encryption has been used by ransomware creators such as BlackMatter, DarkSide, and LockBit 2.0. Unlike the others, LockFile is unique because it does not encrypt the initial few blocks, instead, it encrypts every other 16-byte block of a document.
Loman points out that this technique is a great option for bypassing ransomware protection software that depends on statistical analysis for content inspection in order to identify encryption. This is because with this method of intermittent encryption, it’s possible to maintain a text file’s partly legible look, as well as close to the original’s statistical look. Additionally, this method of encryption is much quicker.
As soon as being deployed in the system, the virus then terminates virtualization software and database activities via the Windows Management Interface (WMI) and then starts to encrypt important files and objects.
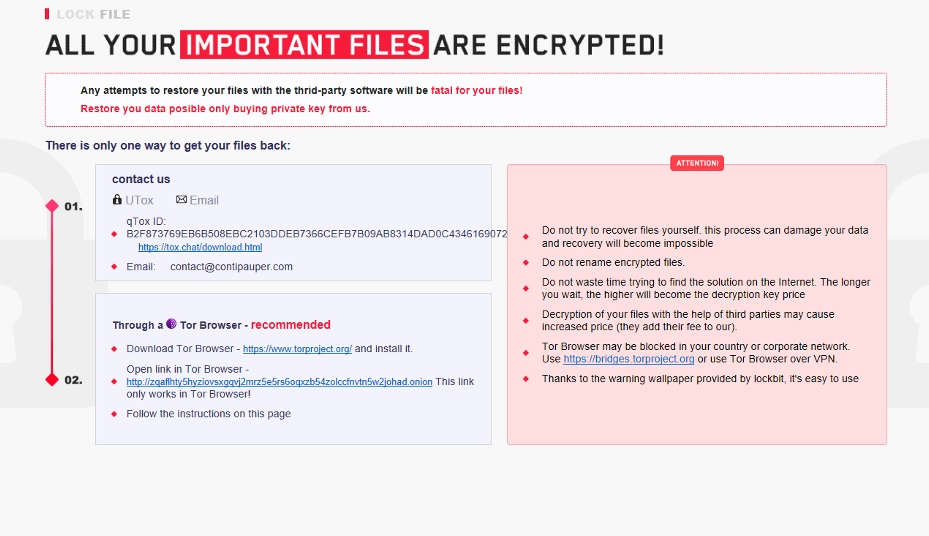
The ransomware note that LockFile displays after the successful encryption resembles the one displayed by LockBit 2.0 ransomware. The message informs the victim that it must reach out to a particular email address, “[email protected],” which is believed to be a reference to a rival ransomware organization named Conti.
The ransomware goes even farther, deleting itself from the computer after encrypting all the data on it, so antivirus software can’t locate or clear up the ransomware code. The findings made by Sophos about LockFile were derived from a file submitted to VirusTotal on August 22, 2021.
When it comes to defense, the conclusion is that the cyberthreat environment is always changing, and the cybercriminals will use any weapon or opportunity to launch a successful attack, compromise business networks, steal data, and lock out victims’ files. Therefore, prevention is the best protection and keeping your files regularly backed up is still one of the best methods to avoid significant data loss.

Leave a Comment