
*Source of claim SH can remove it.
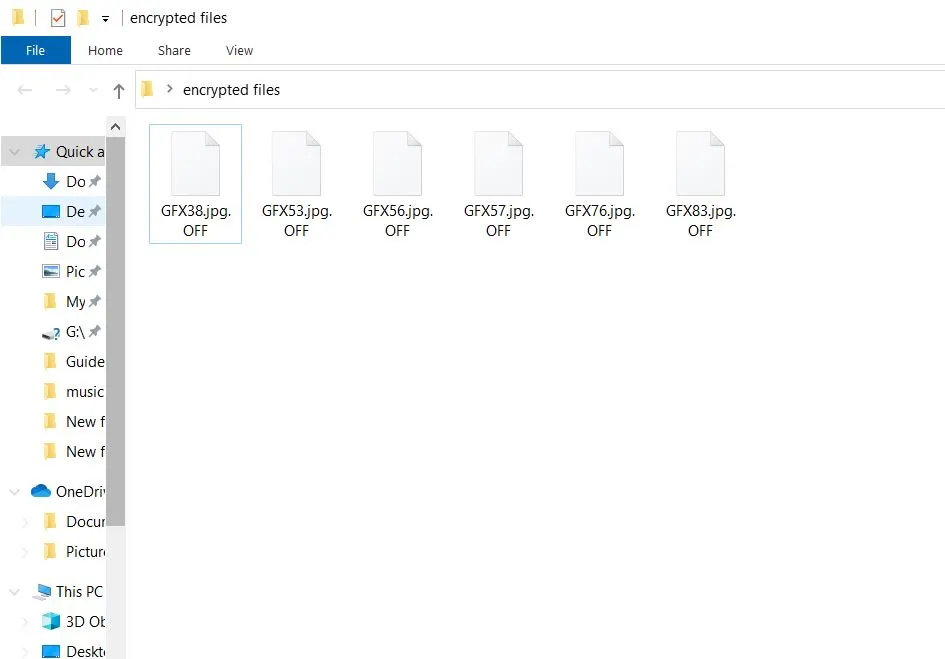
.OFF
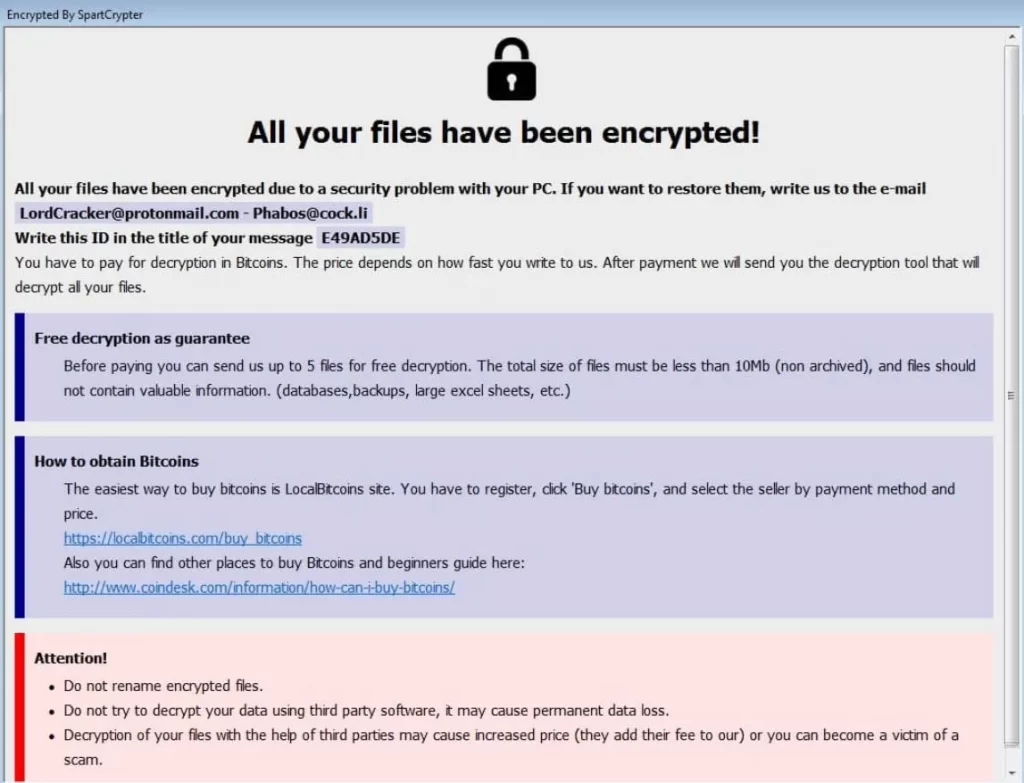
.OFF is a malicious software that encrypts victims’ files, rendering them inaccessible. Like many ransomware threats, once it infects a system, it typically changes the file extensions to its specific signature, in this case, appending .OFF to the end of each filename. Victims then receive a ransom note demanding payment, often in cryptocurrency, in exchange for a decryption key. Ransomware attacks, such as this, can be particularly devastating for both individuals and businesses. The main motive is financial gain, but the aftermath can lead to significant data loss and downtime. Preventive measures, like regular backups and updated security software, are essential to protect against these threats.
The .OFF virus
The .OFF virus typically infiltrates systems through common distribution methods that many cybercriminals employ. Deceptive phishing emails with malicious attachments or links are a favorite approach, tempting unsuspecting users to unknowingly initiate the malware infection. Furthermore, compromised websites or drive-by downloads can stealthily download the ransomware without the user’s knowledge. Exploit kits, which take advantage of unpatched software vulnerabilities, can also serve as a gateway for the .OFF virus and similar threats, such as the Itrz Virus and the Ptrz Virus. Moreover, downloading software from unofficial sources or peer-to-peer networks increases the risk of encountering such malicious payloads. To counter these methods, it’s imperative for users to be cautious of unsolicited emails, ensure regular software updates, and rely on reputable download sources.
The .OFF file
This Ransomware, once activated, targets and encrypts vital files on the victim’s computer, rendering them inaccessible. Each affected file undergoes a transformation and is appended with the “.OFF” file extension, indicating its compromised state. For instance, a document originally named “report.docx” would be renamed to “report.docx.OFF.” The alteration signifies that the file’s content has been encrypted and cannot be opened or viewed without a specific decryption key. Users confronted with these .OFF files often receive ransom notes, demanding payment in exchange for this key. Falling prey to such threats can be devastating, especially when critical documents, photos, or data are held hostage. Ensuring regular backups and employing robust security measures can help mitigate the impacts of such ransomware attacks.
The .OFF Ransomware
Upon falling victim to the .OFF Ransomware, several steps can help mitigate damage and potentially recover files. Firstly, it’s crucial to isolate the infected machine to prevent the ransomware from spreading to other devices or networks. Victims should then explore the availability of free online decryptors; the cybersecurity community often develops these tools in response to new ransomware strains. Simultaneously, individuals should check if they possess recent file backups, as restoring from them can bypass the encryption. Although the .OFF Ransomware attackers typically demand a ransom in exchange for the decryption key, this should be considered a last resort. Only contemplate payment if the encrypted data’s value justifies the financial risk, and always remember that paying doesn’t guarantee file recovery.
SUMMARY:
*Source of claim SH can remove it.
.OFF Ransomware Removal

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Source of claim SH can remove it.
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Type msconfig in the search field and hit enter. A window will pop-up:

Go in Startup —> Uncheck entries that have “Unknown” as Manufacturer.
- Please note that ransomware may even include a fake Manufacturer name to its process. Make sure you check out every process here is legitimate.

*Source of claim SH can remove it.
Type Regedit in the windows search field and press Enter. Once inside, press CTRL and F together and type the virus’s Name.
Search for the ransomware in your registries and delete the entries. Be extremely careful – you can damage your system if you delete entries not related to the ransomware.
Type each of the following in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete everything in Temp. The rest just check out for anything recently added. Remember to leave us a comment if you run into any trouble!

How to Decrypt .OFF files
We have a comprehensive (and daily updated) guide on how to decrypt your files. Check it out here.
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Reply