Re-captha-version-3-18.live may expose your browser to redirects, ads, and persistent unwanted components. Install SpyHunter Pro to scan for risks, remove related threats, and enable real-time protection.
*Source of claim SH can remove it. Trial w/Credit card; image is for illustration; full terms.
*Source of claim SH can remove it.
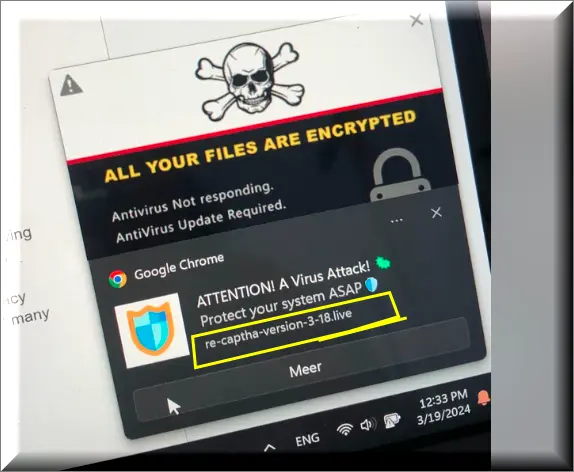
Applications like Re-captha-version-3-18.live create significant disturbances during your online activities. They modify your browser preferences without consent to direct you towards their preferred websites and advertisements, generating revenue in the process. The situation escalates as they can also pilfer your personal data and expose your computer to severe threats, such as viruses or schemes aimed at further data theft. Prolonged presence of Re-captha-version-3-18.live on your system could escalate to substantial security issues, underscoring the importance of promptly eliminating it to protect both your device and personal information.
Is Re-captha-version-3-18.live safe?
Re-captha-version-3-18.live Virus
Referring to it as the “Re-captha-version-3-18.live virus” might not be technically accurate, yet browser hijackers like these still represent a tangible risk to users. Unlike viruses, which aim to damage or erase data, hijackers primarily alter browser settings to redirect traffic for aggressive advertising. While not inherently malevolent, such modifications can compromise your system, paving the way for more serious malware attacks. This effectively turns your browser into a breeding ground for security issues, including possible malware infections, leading to the common misnomer “Re-captha-version-3-18.live virus”. Understanding this distinction is key to safer browsing and a stronger defense against diverse cyber threats.
What is Re-captha-version-3-18.live?
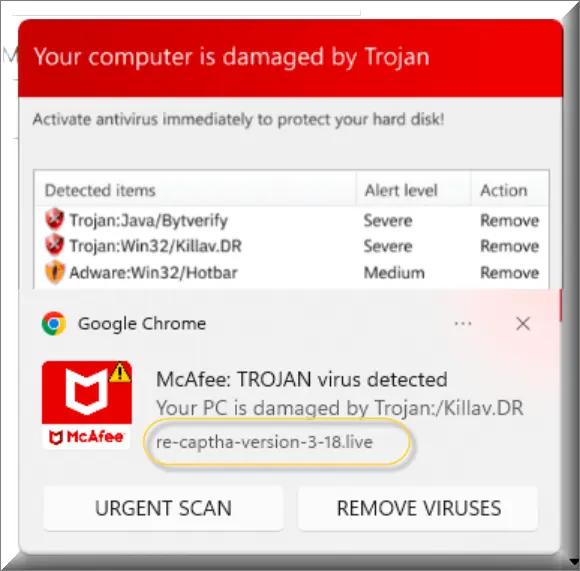
Re-captha-version-3-18.live proves to be a considerable nuisance. Beyond bombarding you with continuous pop-ups and ads, it scrutinizes your online activities to collect data on you. This data might then be sold or used to besiege you with an increased volume of targeted advertisements, special offers, promotional content, and banners. More alarmingly, it could inadvertently direct you to unsafe websites where you’re at risk of being deceived or downloading malevolent software or substandard applications from dubious sources. Thus, what starts as a mere annoyance with Re-captha-version-3-18.live can rapidly escalate into a significant security issue, emphasizing the critical need to eliminate it promptly.
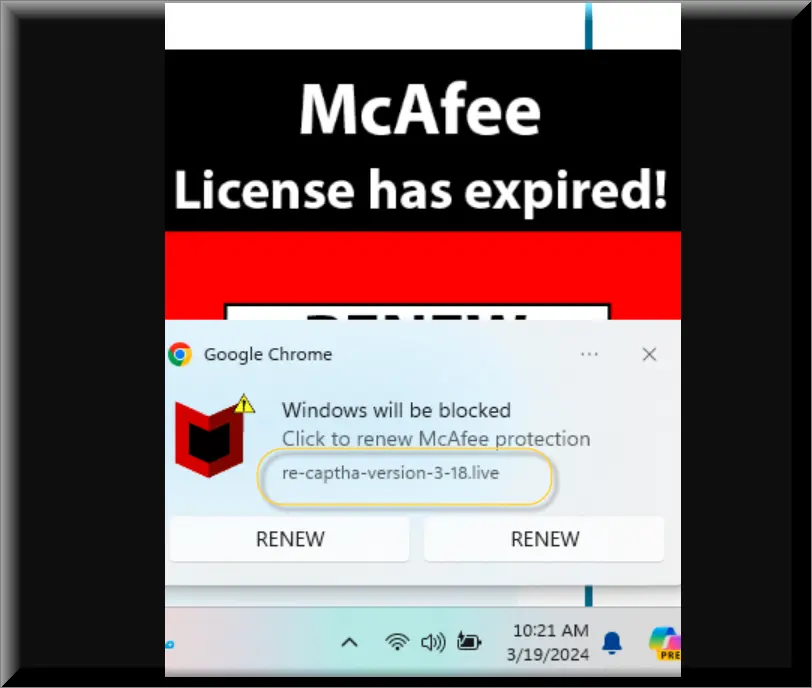
Re-captha-version-3-18.live Pop-ups
The Re-captha-version-3-18.live pop-ups serve as a revenue generation mechanism for the creators of the hijacker, leveraging a pay-per-click advertising scheme. These continual disturbances not only degrade your web surfing experience but also profit the orchestrators of this scheme. Eradicating this pervasive annoyance requires more than merely closing the pop-ups; it necessitates the complete excision of the hijacker from your system, a process that may be intricate and involve several steps. Due to the complex nature of this endeavor, a detailed guide is provided to assist in the comprehensive removal of the hijacker, ensuring the restoration of a secure and tranquil browsing environment.
Re-captha-version-3-18.live on Chrome
Addressing Re-captha-version-3-18.live on Chrome entails contending with numerous vexing issues such as incessant pop-ups, altered browser settings, and unexpected redirects to unintended websites. Attempts to rectify the situation by erasing your browsing history or removing unusual browser extensions may prove insufficient. Re-captha-version-3-18.live embeds itself deeper into your system, necessitating a thorough cleanup of your computer to completely eradicate it. It’s crucial to cleanse not only your browser but your entire system to successfully remove Re-captha-version-3-18.live on Chrome and safeguard your online browsing experience.
Re-captha-version-3-18
If your browser spontaneously navigates to Re-captha-version-3-18, Re-captha-version-3-16.live or Resultsearch.net without any action on your part, it signals that the scam has infiltrated your computer. While the website may appear benign, it could serve as a gateway to further scams or malware. It’s imperative to avoid Re-captha-version-3-18 and diligently inspect your computer to ensure the scam’s remnants are fully eradicated. Swift action is vital for the protection of your computer; follow the provided guide closely and consider employing a reputable anti-malware tool for thorough cleaning and securing your browsing activities.
SUMMARY:
| Name | Re-captha-version-3-18.live |
| Type | Adware/Browser Hijacker |
| Detection Tool |
We tested that SpyHunter successfully removes Re-captha-version-3-18.live* and we recommend downloading it. Manual removal may take hours, it can harm your system if you re not careful, and Re-captha-version-3-18.live may reinstall itself at the end if you don't delete its core files. |
*Source of claim SH can remove it.
Remove Re-captha-version-3-18.live
To try and remove Re-captha-version-3-18.live quickly you can try this:
- Go to your browser’s settings and select More Tools (or Add-ons, depending on your browser).
- Then click on the Extensions tab.
- Look for the Re-captha-version-3-18.live extension (as well as any other unfamiliar ones).
- Remove Re-captha-version-3-18.live by clicking on the Trash Bin icon next to its name.
- Confirm and get rid of Re-captha-version-3-18.live and any other suspicious items.
If this does not work as described please follow our more detailed Re-captha-version-3-18.live removal guide below.
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide.
Some of the steps may require you to exit the page. Bookmark it for later reference.
Next, Reboot in Safe Mode (use this guide if you don’t know how to do it).
 Uninstall the Re-captha-version-3-18.live app and kill its processes
Uninstall the Re-captha-version-3-18.live app and kill its processes
The first thing you must try to do is look for any sketchy installs on your computer and uninstall anything you think may come from Re-captha-version-3-18.live. After that, you’ll also need to get rid of any processes that may be related to the unwanted app by searching for them in the Task Manager.
Note that sometimes an app, especially a rogue one, may ask you to install something else or keep some of its data (such as settings files) on your PC – never agree to that when trying to delete a potentially rogue software. You need to make sure that everything is removed from your PC to get rid of the malware. Also, if you aren’t allowed to go through with the uninstallation, proceed with the guide, and try again after you’ve completed everything else.
- Uninstalling the rogue app
- Killing any rogue processes
Type Apps & Features in the Start Menu, open the first result, sort the list of apps by date, and look for suspicious recently installed entries.
Click on anything you think could be linked to Re-captha-version-3-18.live, then select uninstall, and follow the prompts to delete the app.

Press Ctrl + Shift + Esc, click More Details (if it’s not already clicked), and look for suspicious entries that may be linked to Re-captha-version-3-18.live.
If you come across a questionable process, right-click it, click Open File Location, scan the files with the free online malware scanner shown below, and then delete anything that gets flagged as a threat.


After that, if the rogue process is still visible in the Task Manager, right-click it again and select End Process.
 Undo Re-captha-version-3-18.live changes made to different system settings
Undo Re-captha-version-3-18.live changes made to different system settings
It’s possible that Re-captha-version-3-18.live has affected various parts of your system, making changes to their settings. This can enable the malware to stay on the computer or automatically reinstall itself after you’ve seemingly deleted it. Therefore, you need to check the following elements by going to the Start Menu, searching for them, and pressing Enter to open them and to see if anything has been changed there without your approval. Then you must undo any unwanted changes made to these settings in the way shown below:
- DNS
- Hosts
- Startup
- Task
Scheduler - Services
- Registry
Type in Start Menu: View network connections
Right-click on your primary network, go to Properties, and do this:

Type in Start Menu: C:\Windows\System32\drivers\etc\hosts

Type in the Start Menu: Startup apps

Type in the Start Menu: Task Scheduler

Type in the Start Menu: Services

Type in the Start Menu: Registry Editor
Press Ctrl + F to open the search window

 Remove Re-captha-version-3-18.live from your browsers
Remove Re-captha-version-3-18.live from your browsers
- Delete Re-captha-version-3-18.live from Chrome
- Delete Re-captha-version-3-18.live from Firefox
- Delete Re-captha-version-3-18.live from Edge
- Go to the Chrome menu > More tools > Extensions, and toggle off and Remove any unwanted extensions.
- Next, in the Chrome Menu, go to Settings > Privacy and security > Clear browsing data > Advanced. Tick everything except Passwords and click OK.
- Go to Privacy & Security > Site Settings > Notifications and delete any suspicious sites that are allowed to send you notifications. Do the same in Site Settings > Pop-ups and redirects.
- Go to Appearance and if there’s a suspicious URL in the Custom web address field, delete it.
- Firefox menu, go to Add-ons and themes > Extensions, toggle off any questionable extensions, click their three-dots menu, and click Remove.
- Open Settings from the Firefox menu, go to Privacy & Security > Clear Data, and click Clear.
- Scroll down to Permissions, click Settings on each permission, and delete from it any questionable sites.
- Go to the Home tab, see if there’s a suspicious URL in the Homepage and new windows field, and delete it.
- Open the browser menu, go to Extensions, click Manage Extensions, and Disable and Remove any rogue items.
- From the browser menu, click Settings > Privacy, searches, and services > Choose what to clear, check all boxes except Passwords, and click Clear now.
- Go to the Cookies and site permissions tab, check each type of permission for permitted rogue sites, and delete them.
- Open the Start, home, and new tabs section, and if there’s a rogue URL under Home button, delete it.


Leave a Reply