1P5vLEEuGawo33WLs3pVdxTuyjqt7Ymf9C
A lot of online hackers (or at least, that’s what they claim to be) try to blackmail different users all over the Internet into making a ransom payment in a bitcoin wallet like 1P5vLEEuGawo33WLs3pVdxTuyjqt7Ymf9C by threatening them to harm their systems or make some sensitive personal info publicly available through the use of a Trojan Horse virus that has already infected the targeted user’s computer.
Some of our users reached to us about an email they received with the following message:
About few months ago I have gained a full access to all devices used by you for internet browsing. Shortly after, I started recording all internet activities done by you. My Trojan virus continues refreshing its signatures in a non-stop manner (because it is operated by driver), hence it remains undetected by any antivirus software installed in your PC or device. So, I guess now you finally understand the reason why I could never be caught until this very letter… During the process of your personal info compilation, I could not help but notice that you are a huge admirer and regular guest of websites with adult content. You endure a lot of pleasure while checking out porn websites, watching nasty porn movies and reaching breathtaking orgasms. Let me be frank with you, it was really hard to resist from recording some of those naughty solo scenes with you in main role and compiling them in special videos that expose your masturbation sessions, which end with you cumming. Moreover, nothing stops me from uploading all that hot content online, so all public can watch it too. I sincerely hope, you would really not prefer that to happen, keeping in mind all the dirty things you like to watch, (you certainly know what I mean) it will completely ruin your reputation. However, don’t worry, there is still a way to resolve this: You need to carry out a $1590 USD transfer to my wallet (equivalent amount in bitcoins depending on exchange rate at the moment of funds transfer), hence upon receiving the transaction, I will proceed with deleting all the filthy videos with you in main role. Afterwards, we can forget about this unpleasant accident. Furthermore, I guarantee that all the malicious software will also be erased from your devices and accounts. Here is my bitcoin wallet for your reference: 1P5vLEEuGawo33WLs3pVdxTuyjqt7Ymf9C From now on, you have only 48 hours and countdown has started once you opened this very email (in other words, 2 days).
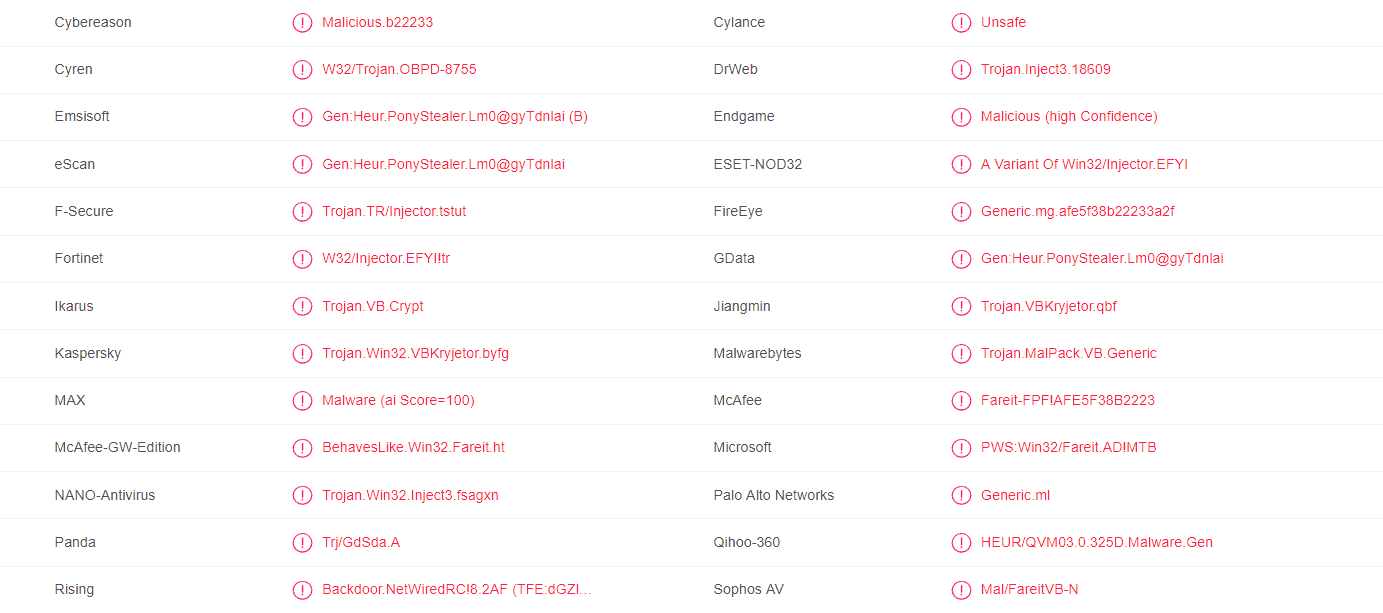
Trojan Horse malware infections are the worst and it is understandable that a lot of users tend to panic when they think such a malicious program has infiltrated their computer. Blackmailing is actually a quite common blackmailing scheme but what you should know is that oftentimes it’s all a ruse. In many cases, the hackers who are sending these blackmailing e-mails and phishing messages are actually bluffing by claiming that they have infected their victim’s computer with some scary Trojan Horse. That is why you should definitely not fall into their trap and send them any of your money. However, since Trojans are indeed a major software threat, it would still be a good idea to check your PC for any hidden malicious software. One recently detected Trojan named 1P5vLEEuGawo33WLs3pVdxTuyjqt7Ymf9C might sometimes be involved in such blackmailing schemes and in this article, we will tell you more about this infection. We will also show you how you can manually remove 1P5vLEEuGawo33WLs3pVdxTuyjqt7Ymf9C in case it has somehow sneaked inside your machine and is currently operating from it. It’s oftentimes difficult to detect a Trojan Horse threat because they might not cause anything unusual on the computer and so there may not be anything to give away their presence. That is why you can never be fully certain that your computer is totally clean in such situations and this is why we advise you to follow the next guide.
How a hacker might use a Trojan Horse
There are oftentimes a variety of ways in which a virus like 1P5vLEEuGawo33WLs3pVdxTuyjqt7Ymf9C, Plurox Backdoor or “You got infected with my malware” could get put into use. Trojans can spy on their victims, harm their systems, corrupt sensitive and important data stored on the machine and even backdoor other infections the likes of Spyware, Rootkits and even insidious Ransomware cryptoviruses. We certainly do not mean to scare you by telling you all that – you might not have anything malicious on your PC since some phishing e-mails do not prove anything. However, being prepared and having taken the right precautions is never a bad thing which is why we advise you to use our guide. Also, the recommended anti-malware tool added to the guide could also be a great asset in your PC security as it could detect hidden threats like 1P5vLEEuGawo33WLs3pVdxTuyjqt7Ymf9C Bitcoin Email which, as earlier mentioned, might often lack any symptoms that you might be able to notice. In case you have any questions, know that you can always ask them in the comments section and we will make sure to answer them. Last, but not least, make sure you stay safe online – do not answer to any spam/phishing/blackmailing e-mails (or open their attachments) and also stay away from any Internet content that you think can’t be trusted.
SUMMARY:
| Name | 1P5vLEEuGawo33WLs3pVdxTuyjqt7Ymf9C |
| Type | Trojan |
| Detection Tool | Some threats reinstall themselves if you don't delete their core files. We recommend downloading SpyHunter to remove harmful programs for you. This may save you hours and ensure you don't harm your system by deleting the wrong files. |
Remove 1P5vLEEuGawo33WLs3pVdxTuyjqt7Ymf9C Bitcoin Email Virus
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning. You can find the removal guide here.
For mobile devices refer to these guides instead: Android, iPhone



Leave a Comment