The See-me.co Virus
See-me.co is a browser hijacker program which usually affects some of the most popular browser programs such as Chrome, Edge, Firefox and others. See-me.co is often installed in the system thanks to methods like software bundling and is usually promoted as a free and helpful browsing tool.

However, some users are pretty displeased by the features that See-me.co tends to introduce into their browsers, as the hijacker is said to collect user browser data, tinker with the search engine and the homepage of the browser and also show dozens of aggressive ads, pop-ups, banners and different sponsored page redirect links.
The See-me.co Facebook messenger Virus
Based on the way See-me.co behaves is Facebook messenger, security experts consider the app to be a browser hijacker. Some users who have been affected by the aggressive ad-generation and page redirects refer to it as a virus. Technically, however, See-me.co in Facebook messenger is not actually a virus because it does not directly damage your system or target your personal files the way that real malware such as a Trojan horse or ransomware would normally do.
However, it is no surprise that many people look for ways to remove the browser hijacker. One of the main reasons is that it tends to change their default browser’s settings by installing new search engine tools, toolbars, homepage domains and unknown buttons. Fortunately, uninstalling See-me.co is not as complicated as some may think. There are some specifics, though, that need to be factored in.
It may be a bit confusing to manually remove a browser hijacker like See-me.co, Best Clever Captcha, Wave browser. Generally, there are two ways you can accomplish this: either by running a scan with a security software tool or by using the detailed instructions in the removal guide below. If you are looking for a quick way to fix the problem, we advise you to use the suggested See-me.co removal tool. In addition to uninstalling the hijacker, it can check for other possible infections if you do a full system scan.
Why is it a good idea to eliminate the browser hijacker?
Apps such as See-me.co are not akin to viruses and other malware programs but they are considered to be potentially unwanted due to a number of reasons. We briefly explained what you can expect from a browser hijacker of this type and, fortunately, none of its activities are aimed at harming your system. However, being exposed to randomly generated ads, different pop-ups and pay-per-click banners may not be the safest thing either. A security risk may occur if you happen to click on a misleading ad or a page-redirect link, which may introduce you to unreliable web content.
Therefore, the security specialists on our team would generally advise you to refrain from opening any ads, links or offers generated by the hijacker as you never know where they may redirect you to. One second of carelessness may really land you a nasty virus, and everyone knows that threats like ransomware, spyware, rootkits and Trojans often hide in seemingly harmless ads in order to infect web users. To permanently stop See-me.co from showing you ads regardless of whether you want them on your screen, we suggest you use the help of the professional See-me.co removal tool on this page or follow the manual instructions.
SUMMARY:
| Name | See-me.co |
| Type | Adware |
| Danger Level | Medium (nowhere near threats like Ransomware, but still a security risk) |
| Detection Tool |
Remove See-me.co Virus
To try and remove See-me.co quickly you can try this:
- Go to your browser’s settings and select More Tools (or Add-ons, depending on your browser).
- Then click on the Extensions tab.
- Look for the See-me.co extension (as well as any other unfamiliar ones).
- Remove See-me.co by clicking on the Trash Bin icon next to its name.
- Confirm and get rid of See-me.co and any other suspicious items.
If this does not work as described please follow our more detailed See-me.co removal guide below.
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab (the “Details” Tab on Win 8 and 10). Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold together the Start Key and R. Type appwiz.cpl –> OK.

You are now in the Control Panel. Look for suspicious entries. Uninstall it/them.
Type msconfig in the search field and hit enter. A window will pop-up:

Startup —> Uncheck entries that have “Unknown” as Manufacturer or otherwise look suspicious.

Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Open the start menu and search for Network Connections (On Windows 10 you just write it after clicking the Windows button), press enter.
- Right-click on the Network Adapter you are using —> Properties —> Internet Protocol Version 4 (ICP/IP), click Properties.
- The DNS line should be set to Obtain DNS server automatically. If it is not, set it yourself.
- Click on Advanced —> the DNS tab. Remove everything here (if there is something) —> OK.


- After you complete this step, the threat will be gone from your browsers. Finish the next step as well or it may reappear on a system reboot.
Right click on the browser’s shortcut —> Properties.
NOTE: We are showing Google Chrome, but you can do this for Firefox and IE (or Edge).

Properties —–> Shortcut. In Target, remove everything after .exe.

![]() Remove See-me.co from Internet Explorer:
Remove See-me.co from Internet Explorer:
Open IE, click ![]() —–> Manage Add-ons.
—–> Manage Add-ons.
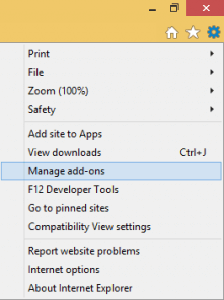
Find the threat —> Disable. Go to ![]() —–> Internet Options —> change the URL to whatever you use (if hijacked) —> Apply.
—–> Internet Options —> change the URL to whatever you use (if hijacked) —> Apply.
![]() Remove See-me.co from Firefox:
Remove See-me.co from Firefox:
Open Firefox, click ![]() ——-> Add-ons —-> Extensions.
——-> Add-ons —-> Extensions.

![]() Remove See-me.co from Chrome:
Remove See-me.co from Chrome:
Close Chrome. Navigate to:
C:/Users/!!!!USER NAME!!!!/AppData/Local/Google/Chrome/User Data. There is a Folder called “Default” inside:
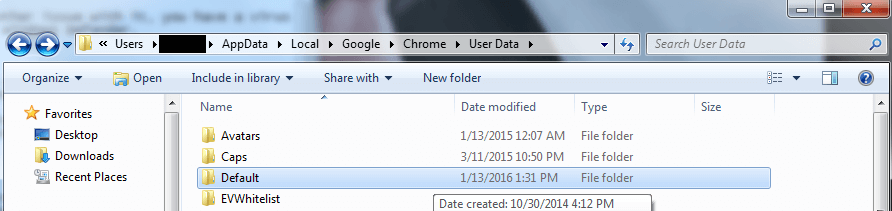
Rename it to Backup Default. Restart Chrome.

Type Regedit in the windows search field and press Enter.
Inside, press CTRL and F together and type the threat’s Name. Right click and delete any entries you find with a similar name. If they don’t show up this way, go manually to these directories and delete/uninstall them:
- HKEY_CURRENT_USER—-Software—–Random Directory. It could be any one of them – ask us if you can’t discern which ones are malicious.
HKEY_CURRENT_USER—-Software—Microsoft—-Windows—CurrentVersion—Run– Random
HKEY_CURRENT_USER—-Software—Microsoft—Internet Explorer—-Main—- Random
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment