SHTORM
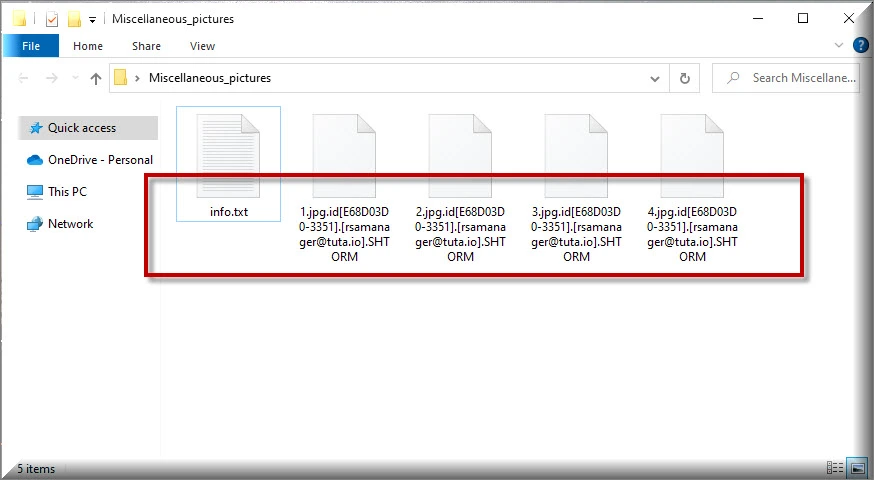
SHTORM is a harmful Windows program that locks user data and is used by its creators for blackmailing and money extortion. The main SHTORM characteristic is that this virus uses encryption to ensure you can no longer access your personal data.
Being infected by a ransomware variant can be a terrifying experience. The shock of having your property invaded and tampered with, and being robbed of your personal or professional files can both be very devastating. One of the latest versions of this malware type is called SHTORM and it can affect anyone from a private person to a large corporation and all with the same purpose – extorting money. The malicious process that viruses like SHTORM implement consists of the encryption of certain file types on the victim user’s computer, as a result of which those files becomes inaccessible to that user. In fact, unless you have a special decryption key, which the hackers then proceed to blackmail their victims for, nobody will be able to open those files with any program. That is the reason why we have designed the below removal guide. It will not only assist you in getting rid of the malicious program that has attacked you, but it may also succeed in recovering the data it has locked.
The SHTORM virus
The SHTORM virus is a terrible software threat capable of keeping you from accessing your own files until you pay a ransom. The encryption the SHTORM virus uses is nearly unbreakable and can only be removed with the help of a secret key possessed by the cybercriminals.
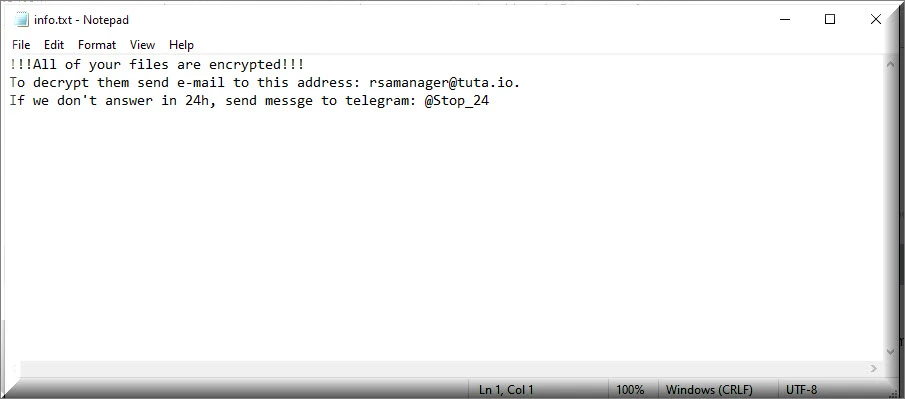
Malware like SHTORM, Wayn, Weqp or .Mkp typically relies on stealth infection methods, so as to remain unnoticed for as long as possible, until it can complete it harmful actions and then reveal itself by means of displaying a disturbing ransom note on the targeted PC’s screen. These methods usually involve various social engineering tactics and can include spam emails or other contaminated messages, as well as drive-by downloads and malvertisements (malicious online ads). Once it makes its way into your system, the virus then proceeds to create encrypted copies of certain files on your computer. The originals are then deleted and once all of this has been done, the ransom note is generated on your screen. The scary thing is that antivirus programs are often helpless against ransomware, because they don’t see the encryption process as a malicious one. And, indeed, it isn’t in itself malicious, because it serves as a means of protecting data. This is also one of the main reasons why ransomware viruses have become such an enormous problem.
The .SHTORM file encryption
The .SHTORM file encryption is the one thing that keeps you from opening or using any of the files the virus has targeted. The .SHTORM file encryption requires a special access key to be unlocked by there may be certain ways to circumvent this need.
If you have been affected by SHTORM, then you probably want to hear what you should do in order to counter this horrible infection. Of course, paying the ransom amount may be the first option that comes to mind, but you can be sure that it’s not the best one. For one, you may never receive the decryption key that the hackers have promised to send you in exchange for the ransom money. In fact, this is a fairly common situation that users, unfortunately, are faced with and that point they are still left with their locked data and nothing to show for it, but a lighter wallet. There are other options out there, like the removal guide that we have attached below. In it, you will find detailed instructions as to the removal of SHTORM, which is essential that you do anyway, so as to prevent future encryption of any further files of yet another encryption of the files you manage to save. After you have deleted the ransomware, you can refer to the instructions in the same removal guide that will help you restore your files from system backups. We cannot vouch for the success of this process, but it’s still worth giving a shot.
Other options are, for example, reaching out to another professional, someone who specializes in ransomware threats. Perhaps they will be able to assist you with their experience. Another thing you can try if all else fails is using one of the decryptor tools we have published here. The list is frequently updated and includes all the latest software versions that may be able to breach the encryption and restore your files. New ones are constantly developed to keep up with the ever-evolving ransomware viruses, so you never know – perhaps the one that can solve the issue in your case is just waiting for you on that list. We would also like to mention that from now on it would be smart to always keep infections like these in the back of your head and duly prepare yourself for any potential ones in the future. One of the ways you can do this is by backing up all your most important data and storing it on a separate external drive.
SUMMARY:
| Name | SHTORM |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Symptoms | Ransomware usually doesn’t get noticed until the files that it targets can no longer be opened due to encryption. |
| Distribution Method | Pirate sites and misleading clickbait ads and links are often the main methods used for spreading Ransomware. |
| Detection Tool |
Some threats reinstall themselves if you don’t delete their core files. We recommend downloading SpyHunter to remove harmful programs for you. This may save you hours and ensure you don’t harm your system by deleting the wrong files. |
Remove SHTORM Ransomware

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Type msconfig in the search field and hit enter. A window will pop-up:

Go in Startup —> Uncheck entries that have “Unknown” as Manufacturer.
- Please note that ransomware may even include a fake Manufacturer name to its process. Make sure you check out every process here is legitimate.

Type Regedit in the windows search field and press Enter. Once inside, press CTRL and F together and type the virus’s Name.
Search for the ransomware in your registries and delete the entries. Be extremely careful – you can damage your system if you delete entries not related to the ransomware.
Type each of the following in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete everything in Temp. The rest just check out for anything recently added. Remember to leave us a comment if you run into any trouble!

How to Decrypt SHTORM files
We have a comprehensive (and daily updated) guide on how to decrypt your files. Check it out here.
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Reply