*Source of claim SH can remove it. Eking Eking is recognized as a ransomware cryptovirus and is mainly distributed via spam messages, malicious email attachments, cracked software installers and malvertisements. The creators of Eking use it to...
Tag - Phobos
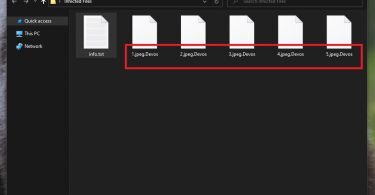
Devos Virus
Devos Devos is a ransomware infection that can block access to a large portion of the digital files stored on a computer. Devos does that through encryption that is secretly applied to each and every targeted file without the users’ knowledge. The...