Devos
Devos is a ransomware infection that can block access to a large portion of the digital files stored on a computer. Devos does that through encryption that is secretly applied to each and every targeted file without the users’ knowledge. The decryption key that the hackers behind Devos blackmail you for is what you will need to reverse the encryption. However, it is unwise to blindly trust the blackmailers’ promises of giving you this key after you pay them. There’s always a possibility that you won’t get the key even if you make the money transfer.
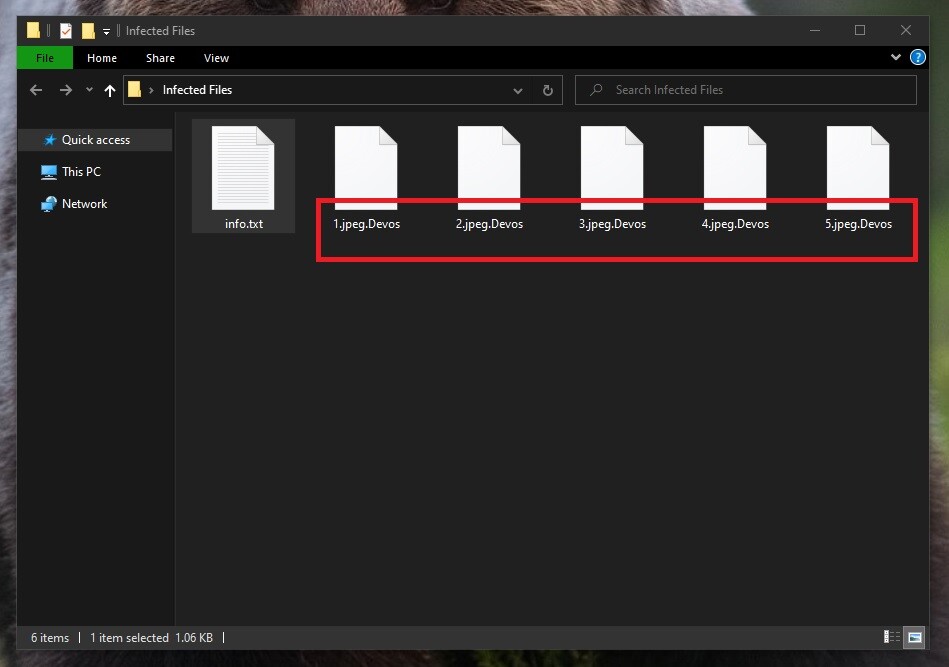
The Devos Virus will encrypt your files
In case you have found Devos on your computer, you will need some serious assistance in order to deal with it. The reason is, what you are facing is a cryptovirus Ransomware that encrypts user data with a secret code decryptable only with a special decryption key. The files that Devos targets typically get their file extension replaced with a custom one that makes them essentially unreadable for any software. The next thing the malware does after the encryption is it asks its victims for a ransom payment in order to provide them with a decryption key.
Unfortunately, because of their often irreversible and complex encryption algorithms, Devos and other similar ransomware viruses have become one of the most devastating categories of malware threats. Even if you pay the ransom that the attackers behind the ransomware request, you may not receive the key needed to recover your data.
That’s why, instead of sending your money to some ruthless cybercriminals, on this page, we would like to provide you with a possible roundabout for those files affected by Devos. In the next lines, we will give you the most relevant ransomware details along with a removal guide with instructions on how to remove the virus and a few suggestions to help you potentially get back your encrypted data.
The Devos virus
The Devos virus is a file-encrypting threat intended to encode user files and keep them hostage until a ransom is paid. The Devos virus usually encodes a list of files that are considered valuable to the victim and changes their file extension to make them inaccessible.
In case of an infection with a virus such as Devos, the first thing you should do is inform yourself about the alternative options. It is highly advisable that you do not pay the money right-away. Such a course of action is not guaranteed to yield a favorable outcome, but will definitely help finance the attackers behind the ransomware. It is possible that a decryption key will not even be provided to free your files.
That is why our recommendation is to try to find other options. For instance, you can use your personal backup sources to access copies of your most needed files, or you can try to extract file backups from your system, as suggested in the file-recovery section of the removal guide below. Contacting a local security specialist is another possible alternative. Regardless of what you decide to do to retrieve your encrypted information, one thing is certain – you should remove Devos from your system if you don’t want the recovered files to get encrypted again.
The Devos file decryption
The Devos file decryption is a process that allows the victims of Devos to recover their files. The Devos file decryption process may take some time and can be successful only if the victims apply a working decryption key. The file encryption that Devos utilizes is what ensures that the data targeted by this virus cannot be accessed or used by anyone. During the encryption, the Devos virus generates a special key that is unique for each computer. This means that you could get sent a key after you pay the ransom but if that key isn’t the one generated for your computer, it won’t work and your files won’t get released.
Before giving a try to any file-recovery method, however, the victims of ransomware have to first remove the infection from their system. This can be a tedious process, as the ransomware likes to hide deep inside the systems it infects. That’s why, if you do not feel confident enough to do everything manually, you are advised to use a professional removal tool to deal with Devos. Once you have taken care of the malware, you can then continue with different file-restoration techniques.
SUMMARY:
| Name | Devos |
| Type | Ransomware |
| Detection Tool |
Remove Devos Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Leave a Comment