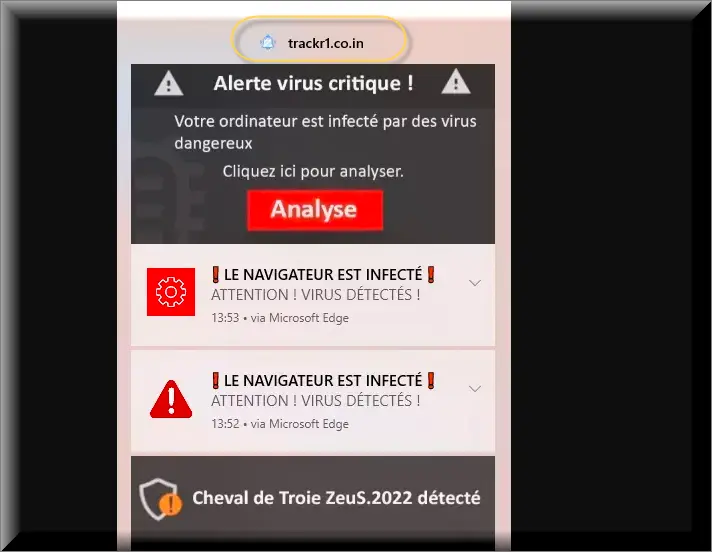
Programs such as Trackr1.co.in pose significant issues while navigating the online realm. They alter browser configurations without consent, directing users to preferred websites and advertisements to generate revenue. However, the predicament escalates as they can also pilfer personal data, rendering computers susceptible to more severe attacks like viruses or schemes aimed at further data theft. Lingering presence of Trackr1.co.in on one’s device could precipitate substantial security hazards, emphasizing the urgency of its removal to safeguard both the computer and personal information.
Is Trackr1.co.in Safe?
Trackr1.co.in Virus
While not accurately categorized as a “Trackr1.co.in virus,” browser hijackers akin to this one still present potential risks to users. Diverging from viruses, which aim to corrupt or erase data, hijackers primarily focus on modifying browser settings to divert traffic and facilitate intrusive advertising. Despite lacking inherent malice, the alterations introduced by the hijacker can introduce vulnerabilities in the system, creating openings for more severe malware exploitation. This effectively transforms browsers into fertile ground for a myriad of security concerns, including potential malware infiltrations, justifying the colloquial reference to this hijacker as the “Trackr1.co.in virus.” Understanding this critical disparity is pivotal in fostering safer browsing practices and fortifying defenses against various cyber threats.
What is Trackr1.co.in?
Trackr1.co.in proves to be a substantial nuisance, inundating users with incessant pop-ups and ads while surreptitiously monitoring online activities to gather user data. This data may be monetized or employed to bombard users with additional advertisements, sponsored content, promotional links, and banners. Moreover, it could inadvertently lead users to perilous websites where they might fall victim to scams or inadvertently download malicious software or substandard programs from dubious developers. Thus, what may initially manifest as a mere annoyance can swiftly escalate into a significant security threat, underscoring the imperative of its immediate eradication.
Trackr1.co.in Pop-ups
The Trackr1.co.in, Pakfn.co.in , Brob.co.in or Hericard.co.in pop-ups serve as a conduit for the hijacker creators to capitalize on pay-per-click advertising, generating revenue while interrupting users’ browsing experiences. Regrettably, dismissing these persistent interruptions is not as straightforward as closing the pop-ups themselves; it necessitates the complete elimination of the hijacker from the system, a potentially intricate and multistep process. Given the complexity involved, a comprehensive removal guide is provided below to facilitate a seamless and thorough elimination. Adherence to each step diligently is imperative to restore a safe and uninterrupted browsing environment.
Trackr1.co.in on Chrome
Encountering Trackr1.co.in on Chrome entails grappling with myriad vexatious issues, including incessant pop-ups, alterations to browser settings, and inadvertent redirection to undesired websites. Merely attempting to rectify the situation by clearing browsing history or removing suspicious browser extensions may prove insufficient. Trackr1.co.in embeds itself deeply into the system, requiring a thorough cleanup of the entire computer to ensure its permanent eradication. Ensuring comprehensive cleanup, not solely confined to the browser, is essential in eliminating Trackr1.co.in from Chrome and safeguarding online browsing experiences.
Trackr1.co.in
When browsers autonomously redirect users to Trackr1.co.in, sans user intervention, it serves as a glaring indication of the intrusion into the system. Although the website may appear innocuous, it could potentially ensnare users in further scams or expose them to malware. It is imperative not only to steer clear of Trackr1.co.in but also to meticulously inspect the computer to ensure no remnants of the scam persist. Prompt action is paramount to safeguarding the computer; hence, following the provided guide diligently and considering the utilization of a reputable anti-malware tool for cleanup is advisable to uphold secure browsing practices.
SUMMARY:
| Name | Trackr1.co.in |
| Type | Adware/Browser Hijacker |
| Detection Tool |
Some threats reinstall themselves if you don’t delete their core files. We recommend downloading SpyHunter to remove harmful programs for you. This may save you hours and ensure you don’t harm your system by deleting the wrong files. |
Remove Trackr1.co.in
To try and remove Trackr1.co.in quickly you can try this:
- Go to your browser’s settings and select More Tools (or Add-ons, depending on your browser).
- Then click on the Extensions tab.
- Look for the Trackr1.co.in extension (as well as any other unfamiliar ones).
- Remove Trackr1.co.in by clicking on the Trash Bin icon next to its name.
- Confirm and get rid of Trackr1.co.in and any other suspicious items.
If this does not work as described please follow our more detailed Trackr1.co.in removal guide below.
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide.
Some of the steps may require you to exit the page. Bookmark it for later reference.
Next, Reboot in Safe Mode (use this guide if you don’t know how to do it).
 Uninstall the Trackr1.co.in app and kill its processes
Uninstall the Trackr1.co.in app and kill its processes
The first thing you must try to do is look for any sketchy installs on your computer and uninstall anything you think may come from Trackr1.co.in. After that, you’ll also need to get rid of any processes that may be related to the unwanted app by searching for them in the Task Manager.
Note that sometimes an app, especially a rogue one, may ask you to install something else or keep some of its data (such as settings files) on your PC – never agree to that when trying to delete a potentially rogue software. You need to make sure that everything is removed from your PC to get rid of the malware. Also, if you aren’t allowed to go through with the uninstallation, proceed with the guide, and try again after you’ve completed everything else.
- Uninstalling the rogue app
- Killing any rogue processes
Type Apps & Features in the Start Menu, open the first result, sort the list of apps by date, and look for suspicious recently installed entries.
Click on anything you think could be linked to Trackr1.co.in, then select uninstall, and follow the prompts to delete the app.

Press Ctrl + Shift + Esc, click More Details (if it’s not already clicked), and look for suspicious entries that may be linked to Trackr1.co.in.
If you come across a questionable process, right-click it, click Open File Location, scan the files with the free online malware scanner shown below, and then delete anything that gets flagged as a threat.


After that, if the rogue process is still visible in the Task Manager, right-click it again and select End Process.
 Undo Trackr1.co.in changes made to different system settings
Undo Trackr1.co.in changes made to different system settings
It’s possible that Trackr1.co.in has affected various parts of your system, making changes to their settings. This can enable the malware to stay on the computer or automatically reinstall itself after you’ve seemingly deleted it. Therefore, you need to check the following elements by going to the Start Menu, searching for them, and pressing Enter to open them and to see if anything has been changed there without your approval. Then you must undo any unwanted changes made to these settings in the way shown below:
- DNS
- Hosts
- Startup
- Task
Scheduler - Services
- Registry
Type in Start Menu: View network connections
Right-click on your primary network, go to Properties, and do this:

Type in Start Menu: C:\Windows\System32\drivers\etc\hosts

Type in the Start Menu: Startup apps

Type in the Start Menu: Task Scheduler

Type in the Start Menu: Services

Type in the Start Menu: Registry Editor
Press Ctrl + F to open the search window

 Remove Trackr1.co.in from your browsers
Remove Trackr1.co.in from your browsers
- Delete Trackr1.co.in from Chrome
- Delete Trackr1.co.in from Firefox
- Delete Trackr1.co.in from Edge
- Go to the Chrome menu > More tools > Extensions, and toggle off and Remove any unwanted extensions.
- Next, in the Chrome Menu, go to Settings > Privacy and security > Clear browsing data > Advanced. Tick everything except Passwords and click OK.
- Go to Privacy & Security > Site Settings > Notifications and delete any suspicious sites that are allowed to send you notifications. Do the same in Site Settings > Pop-ups and redirects.
- Go to Appearance and if there’s a suspicious URL in the Custom web address field, delete it.
- Firefox menu, go to Add-ons and themes > Extensions, toggle off any questionable extensions, click their three-dots menu, and click Remove.
- Open Settings from the Firefox menu, go to Privacy & Security > Clear Data, and click Clear.
- Scroll down to Permissions, click Settings on each permission, and delete from it any questionable sites.
- Go to the Home tab, see if there’s a suspicious URL in the Homepage and new windows field, and delete it.
- Open the browser menu, go to Extensions, click Manage Extensions, and Disable and Remove any rogue items.
- From the browser menu, click Settings > Privacy, searches, and services > Choose what to clear, check all boxes except Passwords, and click Clear now.
- Go to the Cookies and site permissions tab, check each type of permission for permitted rogue sites, and delete them.
- Open the Start, home, and new tabs section, and if there’s a rogue URL under Home button, delete it.

Leave a Reply