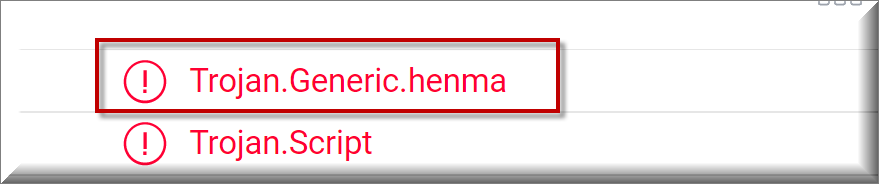
Trojan.Generic.henma
Trojan.Generic.henma is a stealthy computer infection that secretly reaches its victims’ computers using different techniques of disguise. Online security professionals recognize Trojan.Generic.henma as a Trojan horse – malware that can be used to spy on its victims, corrupt their data or steal digital information.
In general, Trojan horse viruses are a very versatile type of computer malware and are common among organized online crime gangs. As a matter of fact, nowadays a lot of malware attacks are based on the assistance of some sort of Trojan horse infection. Moreover, the Trojans often help threats such as the notorious ransomware and spyware to infect computers and to spread across the web.
An important thing to note regarding new Trojan viruses such as Trojan.Generic.henma, Wup.exe, Ground.exe is that they cannot always be detected in due time, even when the user has a reliable antivirus program on their computer. The reason for this is that most modern antivirus applications rely on their database in order to detect incoming threats and if a new threat has not been timely added to the database, it literally remains invisible for the security program. The same is valid if the user has not updated their security software for long. The outdated database does not have the new virus definitions needed to identify the new threat, thus, the antivirus program won’t do anything to stop the malware from performing its activities or remove it until it’s been updated. This over-dependence on malware databases is exactly why new Trojan versions like Trojan.Generic.henma often manage to run over some security programs and start to perform their criminal agenda inside the computer without the user knowing about their presence. What adds to the Trojans’ effectiveness is that, in most cases, there are no obvious symptoms that can serve as red flags and help you detect the malware in the system. Still, if you are observant, you may potentially notice some issues that may signal a possible Trojan horse infection.
One of the most prominent red flags that should not be ignored and could tell you that something wrong is happening on your computer is when your machine begins to crash, freeze or become unstable or unresponsive without any particular reason. If you start to face frequent BlueEntertainment.exe crashes, unusual system errors, or some strange activity that has not been authorized by you, this could mean that your computer is controlled by a Trojan such as Trojan.Generic.henma. Of course, there could be many other technical or software-related reasons for the aforementioned symptoms but it doesn’t harm to run a full scan with reliable and updated security program to check for the potential presence of malware.
The general rule is that if you detect anything unusual, you should examine the underlying problem and remove any malware that may be related to it. The removal guide which we have posted on this page will definitely help you do these two things, especially so if you think that Trojan.Generic.henma can be in your system. It is crucial to uninstall this Trojan in time because, otherwise, it could lead to a wide variety of problems and even allow other viruses like Ransomware to enter your computer.
SUMMARY:
| Name | Trojan.Generic.henma |
| Type | Trojan |
| Detection Tool |
Remove Trojan.Generic.henma
If you are looking for a way to remove Trojan.Generic.henma you can try this:
- Click on the Start button in the bottom left corner of your Windows OS.
- Go to Control Panel -> Programs and Features -> Uninstall a Program.
- Search for Trojan.Generic.henma and any other unfamiliar programs.
- Uninstall Trojan.Generic.henma as well as other suspicious programs.
Note that this might not get rid of Trojan.Generic.henma completely. For more detailed removal instructions follow the guide below.
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold together the Start Key and R. Type appwiz.cpl –> OK.

You are now in the Control Panel. Look for suspicious entries. Uninstall it/them. If you see a screen like this when you click Uninstall, choose NO:


Type msconfig in the search field and hit enter. A window will pop-up:

Startup —> Uncheck entries that have “Unknown” as Manufacturer or otherwise look suspicious.
- Remember this step – if you have reason to believe a bigger threat (like ransomware) is on your PC, check everything here.
Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.

Type Regedit in the windows search field and press Enter.
Once inside, press CTRL and F together and type the virus’s Name. Right click and delete any entries you find with a similar name. If they don’t show up this way, go manually to these directories and delete/uninstall them:
- HKEY_CURRENT_USER—-Software—–Random Directory. It could be any one of them – ask us if you can’t discern which ones are malicious.
HKEY_CURRENT_USER—-Software—Microsoft—-Windows—CurrentVersion—Run– Random
HKEY_CURRENT_USER—-Software—Microsoft—Internet Explorer—-Main—- Random
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment