
*Source of claim SH can remove it.
Wup.exe
Wup.exe is a Trojan Horse cryptocurrency miner, primarily targeting Monero – a favored digital currency among hackers. It infiltrates systems, drains substantial CPU resources, and seriously disrupts system performance. Identified by major antivirus programs like Kaspersky as not-a-virus:RiskTool.Win32.BitCoinMiner.hzkc or Microsoft as HackTool:Win32/BCoinMine, this malicious entity raises considerable security concerns. Lurking undetected, wup.exe can manipulate other programs, monitor applications, and communicate via open network ports. File location can vary; it often nests in a subfolder within the user’s profile folder or “C:\Program Files,” thereby amplifying its security threat to 97-98%. Regardless of its size, often between 3,445,248 to 4,543,488 bytes, this Trojan is not a Windows core file, remaining hidden from view, making its eradication crucial for system health.
What is Wup?
Wup is a Trojan virus that presents considerable problems for Windows users, significantly undermining system performance. This malicious file, often located in C:\Users\USERNAME\AppData\Local\Temp\wup\ or C:\Users\USERNAME\AppData\Local\Temp\csrss\wup\xarch\ folders, launches the rogue process, notorious for exhausting system resources. With resource utilization often exceeding 70% of CPU, GPU, and RAM, systems become incredibly sluggish, raising significant user concerns. But the trouble doesn’t stop at performance issues. Wup may also execute additional harmful actions on your system. Its surreptitious activities, combined with its major drain on resources, necessitate immediate elimination. The priority is not just about restoring performance; it’s also about averting potential additional threats this Trojan could initiate.

Wup in Windows
If you encounter Wup in Windows, know that there are all kinds of different methods that may have allowed the Trojan to infiltrate your system. For instance, threats like Pinaview, Taskbarify are often bundled with seemingly harmless software or concealed in email attachments. Trojans thrive on users’ casual browsing habits and lack of strong security protocols. To avoid future encounters with Wup in Windows, you need to adopt a proactive approach : install reliable, updated antivirus software that provides real-time protection, and ensure the operating system is current with all patches. Regularly scan for vulnerabilities and heed antivirus alerts. Be cautious with downloads and email attachments, particularly from unfamiliar sources. Regularly backup important data as an additional safety measure.
SUMMARY:
*Source of claim SH can remove it.
Remove Wup.exe
To remove wup.exe, you must first get rid of any recently installed program that could be related to it and then clean the system from remaining rogue data, processes, and settings.
- First, go into the Uninstall a Program window, look for sketchy programs, and uninstall anything you deem undesirable/suspicious.
- Next, search the Processes tab of the Task Manager for processes related to wup.exe, and stop them.
- Open the Hosts file, the Task Scheduler, and the Startup items list and clean them from any wup.exeentries.
- Search the System Registry for wup.exe items, such items to remove wup.exe.
If you need additional details about these removal steps, you will find them in the next lines.
Detailed removal instructions for wup.exe
Step 1
Click the Start Menu icon in the bottom-left, type Programs and Features, and press the Enter key. Search the list of programs installed on your PC for anything that looks suspicious and potentially related to the wup.exe virus, especially if it has been recently installed without your knowledge. If you find such a program there, right-click it, select Uninstall, and complete the steps in the uninstaller.

Step 2
WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Source of claim SH can remove it.
Navigate to either of the following two folders (whichever one is present on your PC) and delete the wup.exe file that should be located there.
- C:\Users\USERNAME\AppData\Local\Temp\wup\
- C:\Users\USERNAME\AppData\Local\Temp\csrss\wup\xarch\
Step 3
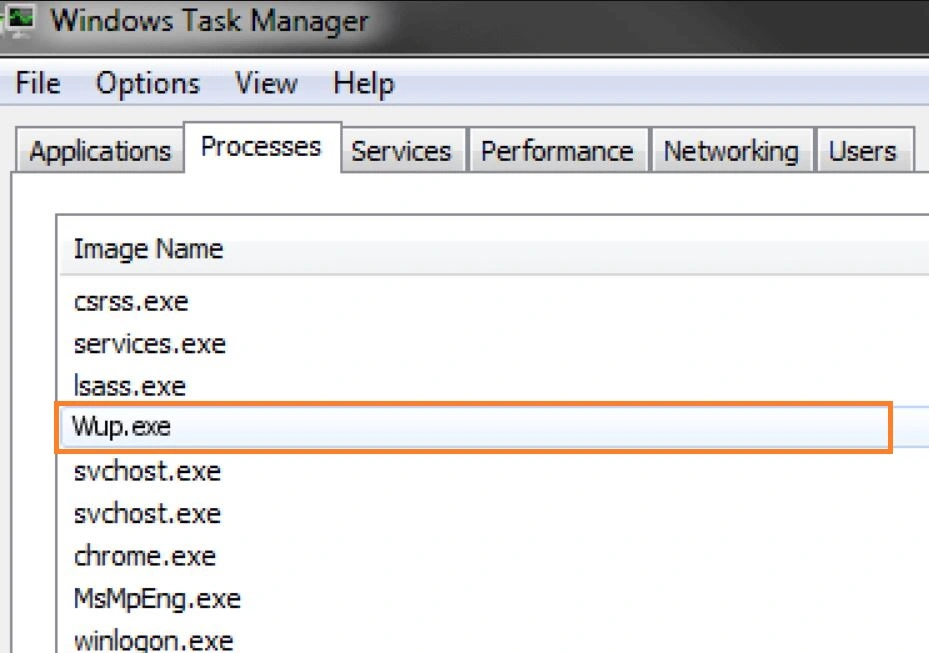
Type Task Manager in the Start Menu, open the Task Manager app that shows up and click Processes. Now look for the wup.exe process in there, right-click it when you find it, and then select Open File Location. Now right-click the process again, select End Process, and then go back to the File Location folder that opened and delete that folder. Then check once more if the wup.exe process is in the Task Manager and if it has been re-launched, end it again.
Also, look for other questionable processes in the Task Manager that could be related to wup.exe. Processes with strange names and excessive use of CPU and virtual memory are potential suspects. If you think that a certain process could be a threat and be related to wup.exe, do the following to determine whether that’s the case:
Search for the process’ name on the Internet and see if there are any search results from cyber-security forums and sites where there’s information about the process. If the process is truly a threat and is linked to wup.exe, this should help you confirm it.
Also, go to the File Location and scan each file that’s there using our free scanner available below. If any of the files turn out to be malicious, this would mean that the process is also a threat and might be related to wup.exe.

If you find out that the suspected process is a threat, end it as you did with wup.exe and also delete its folder.

Step 4
In this step, you must try to prevent the Wup Trojan from starting the wup.exe process again. Deleting the file location folder should have ensured that the rogue process doesn’t get restarted, but we also recommend booting the computer into Safe Mode to add an additional obstacle that would prevent the virus from re-launching its process(es).
Step 5
Type each of the following lines in the Start Menu, hit Enter to go to the respective item, and follow the instructions we’ve shown for it below in order to revoke any settings enforced by wup.exe:
- Msconfig – When you open this, you will be taken to the System Configuration settings. In that window, select Startup, then uncheck from the Startup list anything that looks connected to the wup.exe Trojan as well as anything that is unfamiliar to you or that is with an unknown manufacturer. After that, click OK.

- Task Scheduler – When you start the Task Scheduler, click the Task Scheduler Library from the top-left and then look at the items in the central panel. If among them, you see a task labelled wup.exe or anything similar, right-click it, and select delete. Also do the same with any other unfamiliar and suspicious tasks you may notice there.

- notepad %windir%/system32/Drivers/etc/hosts – Once the Hosts notepad file appears on your screen, scroll down to where the two “Localhost” lines are, and see if below them there are any IP addresses that may be linked to wup.exe. If you find IPs there, send them to us using the comments section below, and we will soon let you know in a reply under your comment if those IPs are related to wup.exe and whether you need to remove them from the Hosts file.

How to remove wup.exe from Windows 10?
To remove wup.exe from Windows 10, aside from uninstalling potentially unwanted programs and eliminating the rogue process and its files, you must also clean the Registry. Deleting any rogue items from the Registry is essential in order to remove wup.exe from Windows 10
Note, however, that this must be done with caution – there are many essential settings stored in the System Registry, and deleting an item that’s not from the virus can oftentimes result in harm to the system, among other problems. Therefore, while completing this final step from our guide, don’t hesitate to ask questions in the comments if you are unsure about anything.
Now, the first thing you ought to do is type regedit.exe in the Start Menu and then open the app that carries the same name. Before the app starts, you will be required to provide Admin permission to launch it – click Yes to give your permission. Next, when a window labeled Registry Editor appears on the screen, press together the Ctrl + F keys, and this will open a small search bar. Type wup in that search bar and begin the search. If a wup item is found, delete it, and search again for the next one.

Keep doing this until you’ve managed to delete all Registry items related to the Wup Trojan, and then navigate to the directories shown below (by expanding the folders in the left panel of the Registry Editor):
- HKEY_CURRENT_USER/Software
- HKEY_CURRENT_USER/Software/Microsoft/Windows/CurrentVersion/Run
- HKEY_CURRENT_USER/Software/Microsoft/Internet Explorer/Main
Each of those directories must be searched for sub-folders (called keys) that have suspicious and unusual names. Commonly, a rogue item in either of those locations would have a randomly-generated name that looks like this “309urjd309tj3e0ir09tgj039d32rjd093j0e”, so if you see anything similar, tell us in the comments about it, and we will tell you if it’s a threat and if you need to delete it.
If the wup.exe process is still running
If the wup.exe process keeps running on your system even after you’ve completed everything shown in the guide, it’s likely that the Trojan behind it has entrenched itself too deep within your system and manual removal may not be feasible. In such cases, we recommend that users employ the help of a reliable security tool that can perform a deep scan of the system and find all rogue wup.exe settings and data related to the virus, and then delete them. The tool mentioned in the guide has been tested against threats of the Trojan Horse variety, and it can quickly identify what needs to be removed and then remove it in no time. We recommend giving it a try if you are still struggling with the removal of wup.exe.

Leave a Reply