W32.AIDetectMalware is one of the most common Trojan Horse detections nowadays, together with Malicious.moderate.ml.score and Malicious.high.ml.score, which leads many people to believe that this is simply a false positive and not a real threat.
In many instances W32.AIDetectMalware is indeed a false positive triggered by some non-harmful app. But this is still a heuristic malware detection, so something in the behavior of a given program or file must have triggered it. It could be something harmless, but do you really want to risk it?
Since you are already reading this, I assume you are at least partially concerned about your system’s safety because one or more files on your PC got flagged with this detection.
If that’s the case, I recommend performing the steps shown in the following removal guide to delete anything potentially dangerous from your PC.
How to Remove the W32.AIDetectMalware Virus
As I said, the W32.AIDetectMalware is often triggered by a file or app that isn’t particularly dangerous, yet it could still be unwanted. If you know what file/app is getting flagged as a Trojan and you aren’t totally sure it’s a safe one, it’s best to delete it. Either go to the file and simply send it to the Bin or, if it’s an app, uninstall it in the following way:
- Go to the Start Menu, search in it for Apps & Features, and open it.
- Sort the list by “Install Date” and see what’s been recently installed.
- Find the app in question, click it, click Uninstall, and go through the removal prompts.
- I also recommend checking the list of installed programs for other questionable items and uninstalling anything suspicious you find.
- Then go to the directory where the removed app used to be installed, see if its folder is still there, and delete it’s been removed during the uninstallation.
If you were unable to perform any of those steps or if despite completing them you are still getting the W32.AIDetectMalware warning, then you’ll need to resort to the more advanced removal method that I’ve explained below.
SUMMARY:
The next steps provide detailed guidance on how to clear your system from malware that security tools identify as W32.AIDetectMalware. However, since there are thousands of threats of various complexity and danger levels that could trigger this detection, I can’t promise that this tutorial will always be enough to fully clean your PC.
For this reason, I strongly recommend combining the manual steps with the use of a professional security tool that can run a comprehensive scan of your system and find any malware remnants that you might have missed. A reliable tool that can help you against any W32.AIDetectMalware threats is SpyHunter 5, which can be accessed through this page.
How to Get Rid of W32.AIDetectMalware
There are two prerequisites for the completion of this guide that you must fulfill before continuing to the actual removal steps:
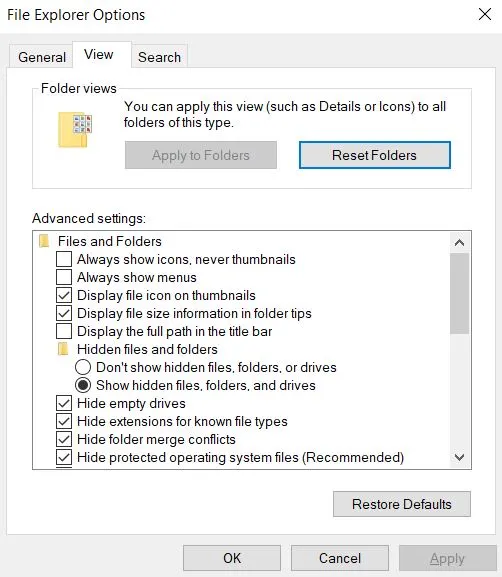
- Make your hidden files and folders visible: Go to the Start Menu, search for Folder Options, open it, enable the Show Hidden Files and Folders option in the View tab, and save the changes.
- Install LockHunter: This is a very helpful free tool you can get from the provided link. It lets you delete files locked by the malware and could prove essential in the completion of some of the next steps.
Once these two conditions are met, you are ready to continue.
Video walkthrough for this step:
How to Delete W32.AIDetectMalware Through the Task Manager
If you are dealing with actual malware, then there will almost certainly be rogue processes that you need to disable.
Open the Task Manager with the Ctrl + Shift + Esc keys by pressing them together, and then expand the list of processes by clicking More Details (unless it’s already been clicked).
Click CPU or Memory from the top to sort the list by usage of the respective resource. Then look for any unfamiliar names among the most resource-intensive processes.
If you spot a suspiciously named process, access its folder by right-clicking it and selecting Open File Location.
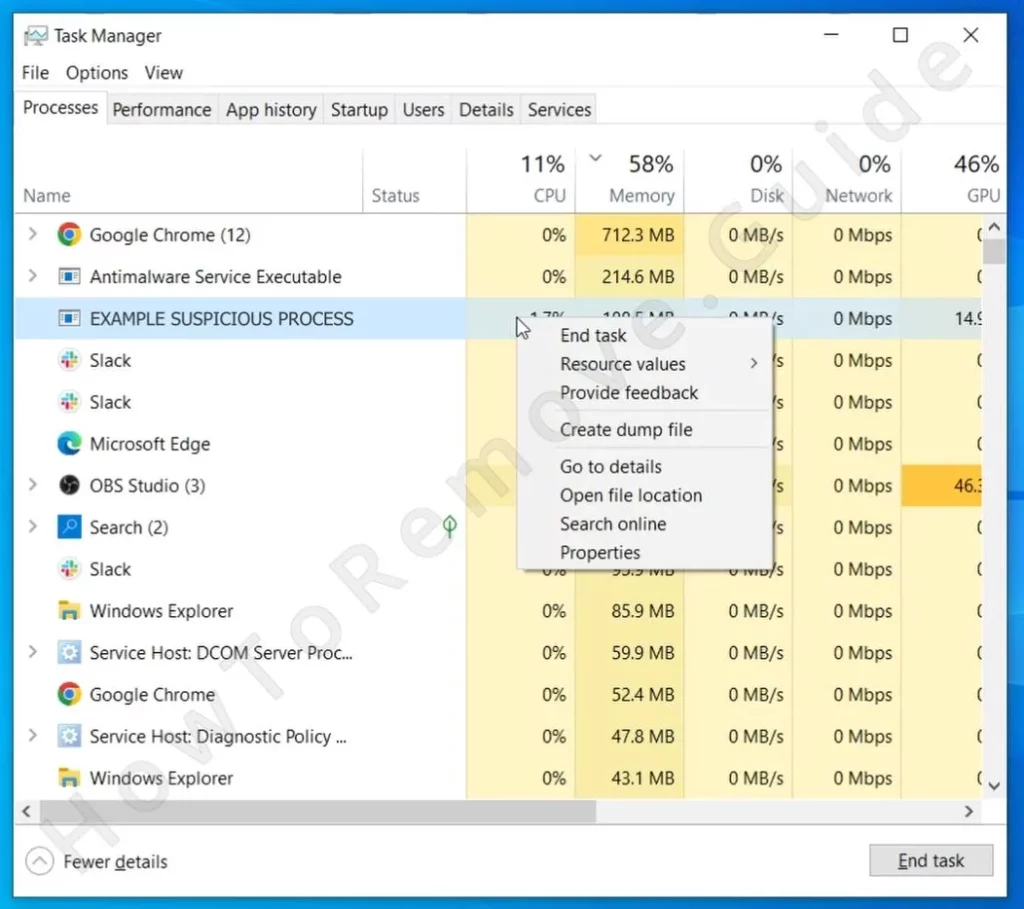
Alt + Tab back to the Task Manager, right-click the suspicious process again, and click End Task.
In the folder you just opened, click the upward arrow in the top-left to go back to its parent folder, and then delete the process folder.
If you can’t delete it because some of its files are in use by other software you first need to make sure that LockHunter is installed on your PC. If you already have it, right-click the folder, click the “What’s locking it?” option, and then click Delete in the next window.
Perform this step for all suspicious processes that might be linked to W32.AIDetectMalware.
W32.AIDetectMalware may expose your browser to redirects, ads, and persistent unwanted components. Install SpyHunter Pro to scan for risks, remove related threats, and enable real-time protection.
*Source of claim SH can remove it. Trial w/Credit card; image is for illustration; full terms.
Video walkthrough for this step:
How to Delete Persistent Files with Lock Hunter
How to Delete W32.AIDetectMalware Virus Files
Even if the rogue processes are gone together with their folders, there are almost certainly more malware files left in various places in your system. Here’s how to find and delete them:
First, go to this directory in your file system:
- C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Startup
Look for suspiciously-named folders that you don’t recognize and if you spot something sketchy, delete it, using LockHunter if needed.
Do the same in this folder:
- C:\Users\YourUsername\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup
Note that if you aren’t sure what to delete in these two folders, just delete everything except a file called Desktop.ini (if you see it there).
Also go to the C:\Users\*YOUR USERNAME*\AppData\Local\Temp folder and there delete everything. Just press Ctrl + A and then Del to send all of its contents to the Bin.
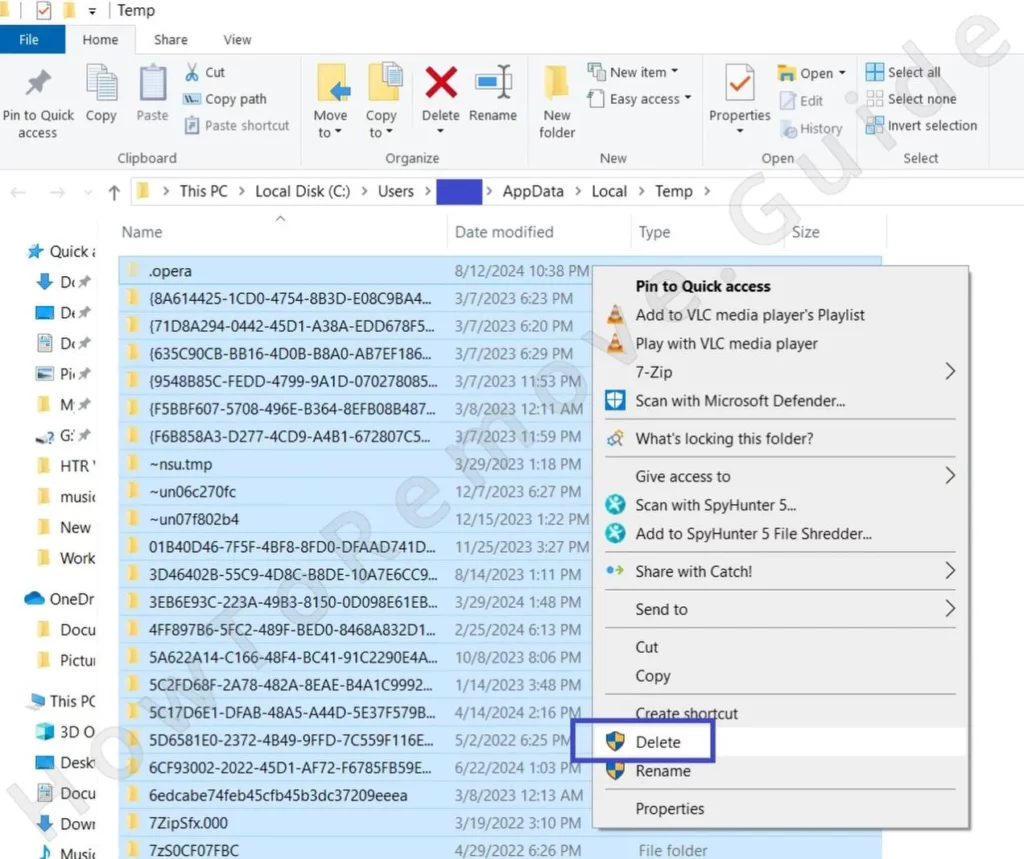
It’s both safe and recommended to fully empty the Temp folder.
Then explore the Program Files and Program Files (x86) folders in the C: drive and search them for oddly-named folders. If you spot a folder with an unfamiliar name, it’s best to delete it, because it’s either for a program you don’t need or one that’s linked to the malware.
Get Rid of W32.AIDetectMalware Scheduled Tasks
Many people forget to clear the Task Manager, but rogue tasks created there could result in the malware’s return even after you’ve removed it. It’s, therefore, essential to check this part of your system.
Search for it and open it through the Start Menu, then click Task Scheduler Library to see all tasks, and start checking them one by one.
Click each task, select the Actions tab, and see what it does. If it accesses a link, downloads a file, or runs a suspicious script or executable, delete the task.
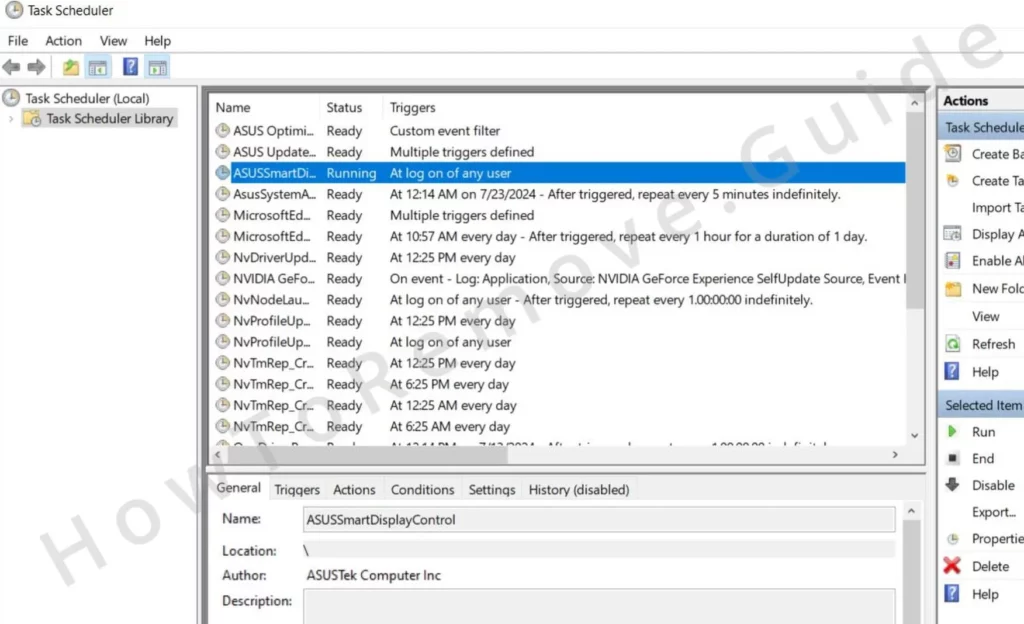
All tasks in the Task Scheduler must be checked in this way – no exceptions.
Video walkthrough for this step:
How to Remove W32.AIDetectMalware From the System Registry
The System Registry is the final place you must search for malware entries and delete anything rogue you find. But be very careful while doing this – you must delete only items that are certainly linked to the malware.
If you aren’t sure that’s the case about a particular registry item, better leave it intact to avoid damaging the system.
Type regedit in the Start Menu and open the first result with admin rights to access the Registry Editor.
Press Ctrl + F and, one by one, search for each process you tried to stop earlier and each program you attempted to uninstall at the very start of this guide.
If any of the searches find anything, delete the respective key in the left panel. Then search again to see if there are more related entries and delete them too.
Once you aren’t getting any more results, manually navigate to these registry directories:
- HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services
- HKCU\Software\Microsoft\Windows\CurrentVersion\Run
- HKCU\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKLM\Software\Microsoft\Windows\CurrentVersion\Run
- HKLM\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKLM\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer\Run
- HKCU\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunServices
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunServicesOnce
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce\Setup
Open each one and check its contents in the right panel.
If you see any suspicious values to the right that seem linked to the malware, delete them and only them.
Do not delete the actual keys that contain the suspicious values. These keys must stay intact.
This was the final of the manual tutorial. I hope this guide was enough to rid you of any threats, detected as W32.AIDetectMalware.
However, if the warnings keep popping up, then I strongly suggest you try SpyHunter 5 and clean your PC with its help. It will take care of any malware in a matter of minutes and also keep you protected from this and other threats in the future.
Video walkthrough for this step:
Is W32.AIDetectMalware a Virus?
W32.AIDetectMalware is a generic Trojan horse detection by Bkav Pro’s antivirus engine. Most users see this detection when they scan a particular file on the VirusTotal website. The site uses many different detection engines to determine the status of a given file and Bkav Pro is only one of them.
The W32.AIDetectMalware detection doesn’t refer to any particular Trojan. It’s a base heuristic detection that the security engine shows whenever a given app, program, or file displays a particular set of suspicious characteristics. As I mentioned, safe and legitimate apps can sometimes be flagged, but in all other cases, when the detection isn’t a false positive, you are probably looking at some type of Trojan Horse threat.
Is W32.AIDetectMalware a False Positive?
So the big question with W32.AIDetectMalware is if it’s really a threat or simply a mistake from the Bkav Pro engine. Since this specific detection moniker can flag both malware and harmless files, it’s essential to know what other red flags to look for in case it really is triggered by something malicious.
This detection will often flag files like Setup.exe and Setup.msi, as well as legitimate utility software downloads, but here’s the catch – Trojans will often disguise as seemingly safe programs and installers. This makes it even more confusing to the user when trying to figure out what they are actually dealing with. Our advice? Play it safe and delete everything you don’t need, recognize, or remember installing/downloading yourself.
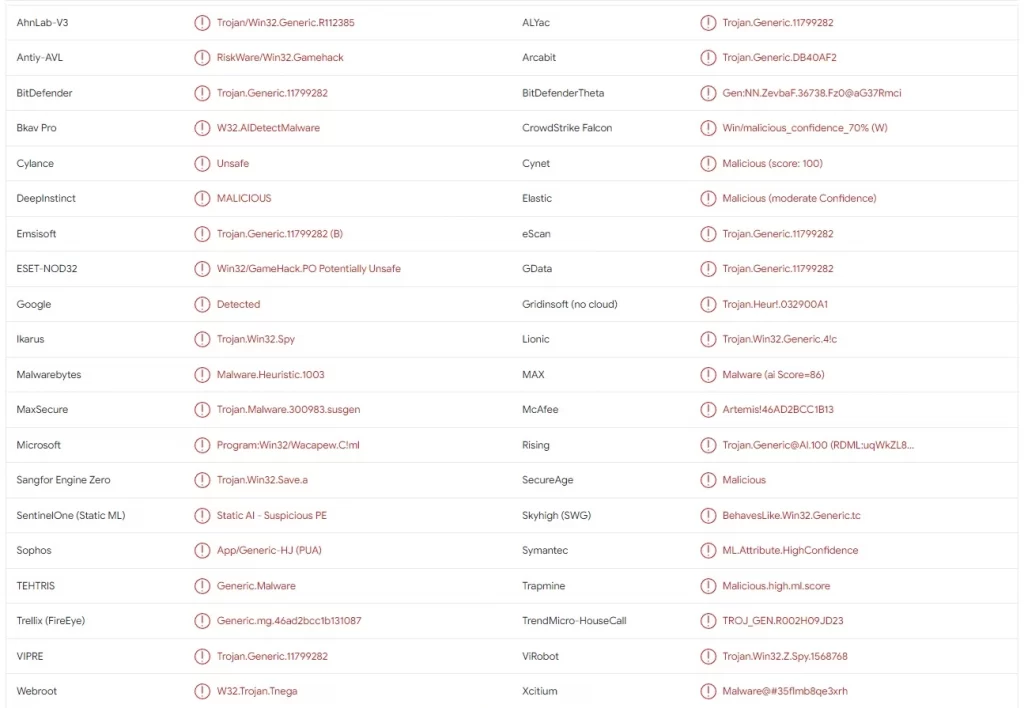
Do Other VirusTotal AVs Detect W32.AIDetectMalware?
If you want to get a clearer picture of whether a given piece of software is dangerous, check out what other detection engines have to say about it. You probably came here because you saw the Bkav Pro W32.AIDetectMalware detection in VirusTotal, but what about the other engines there? If they also flagged the file you scanned, you shouldn’t dismiss it as a file positive.
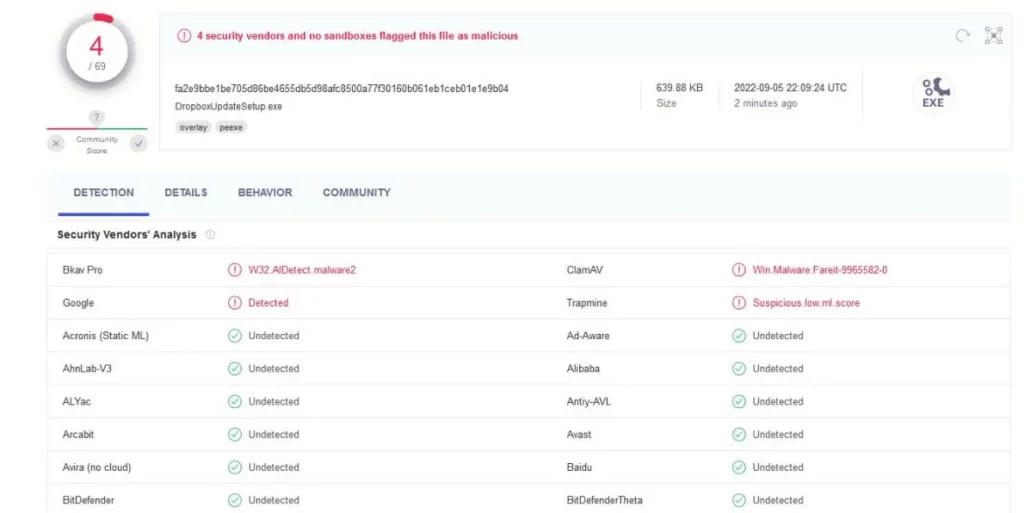
Note that their detection name could be different. A common one is Trojan.Malware.300983.susgen from the MaxSecure AV engine. Even if the name is different, this still tells you that the file is more likely to be unsafe, and that you should probably clean your PC from anything suspicious. Another associated detection is Suspicious.low.ml.score from the Trapmine VirusTotal engine.
If you want further confirmation, I recommend using the anti-malware tool posted on this page. It, too, can tell you if the scanned file is an actual threat and also help you remove it if it is indeed malicious.
W32.AIDetectMalware, Losseless Scaling, Roblox, and Plants vs. Zombies
On the flip side, there are instances when you can be pretty sure that the software that triggers the warning isn’t a threat. Some users have reported that Lossless Scaling – a legitimate app on Steam – will be flagged as W32.AIDetectMalware.
Sure, it’s not impossible that something on Steam gets hijacked by hackers and injected with malware, but the chances of this happening are really, really low. Of course, it’s an entirely different question if you got Lossless Scaling from a different, less legitimate (and legal) source. In that case, a W32.AIDetectMalware detection is a valid reason to be concerned and take measures to secure your PC.
It’s a similar thing with Roblox and PvZ (Plants vs. Zombies). The official games are legitimate, but if you got a cracked version of Roblox or PvZ, then don’t be surprised if it triggers a malware warning.
Another thing to mention here is that games like Roblox and Minecraft let users create custom games and mods. Those are usually monitored for malware, but it’s still not impossible for someone to inject malicious code into custom Roblox assets. Therefore, if you got W32.AIDetectMalware warning from a user-made mod, it’s best to take it as a sign of malware and take immediate action.


Leave a Reply