Malicious.high.ml.score
In order to identify an infection like Malicious.high.ml.score, which is a type of Trojan Horse, it’s crucial to carefully monitor any alterations in your system’s behavior and configurations. This includes being vigilant about the emergence of unfamiliar files or applications, as well as sudden disruptions in your software’s performance. Furthermore, as Trojans often deactivate installed security programs, any abnormal behavior in your antivirus software might signal the presence of this threat. Another aspect to exercise caution about is unexpected pop-ups and questionable advertisements redirecting you to suspicious websites. Taking prompt action upon detecting these indicators will enable you to respond swiftly and effectively eliminate the Malicious.high.ml.score Trojan Horse and protect your digital device from potential significant harm.
What is Malicious.high.ml.score?
Belonging to the Trojan Horse category, Malicious.high.ml.score is a malevolent software that, unlike traditional computer viruses, doesn’t propagate through replication. Instead it employs deceptive strategies to infiltrate systems. It adeptly camouflages itself as legitimate software or enticing free downloads to manipulate users into installation. However, once entrenched within the system, Malicious.high.ml.score provides its illicit operators with unauthorized access, enabling them to execute diverse malicious actions. These may include surveillance of online and offline activities, pilferage of personal or professional data, destruction of important files, or introduction of other malware. For these reasons, swift removal of the threat is essential to protect your computer.
Is Malicious.high.ml.score a Virus?
While both Trojan Horses like Malicious.high.ml.score and computer viruses exhibit malicious intentions, their modes of operation are fundamentally distinct. Computer viruses possess the autonomy to self-replicate and disseminate across diverse systems, infecting numerous files in the process. Conversely, Trojan Horses rely on stealth and camouflage to infiltrate systems, often assuming the guise of harmless or enticing software to deceive users into installing them. Unlike viruses Malicious.high.ml.score, or other Trojans like W32.AIDetectMalware and Suspicious.low.ml.score, harbor a broader range of malicious potentials and can be programmed to execute various forms of harm. More frequently, they serve as a gateway for hackers to illicitly access and attain full control over compromised systems.
Malicious.high.ml.score Virus
The Malicious.high.ml.score virus can infiltrate users through various avenues. One prevalent method involves phishing emails that carry harmful attachments or misleading links. Unsuspecting recipients unwittingly initiate the Trojan’s activation by either opening such emails or engaging with the deceptive links. Additionally, attackers proficiently camouflage the Malicious.high.ml.score virus as legitimate software, disseminating it through free software downloads, torrents, and advertisements. This Trojan infection can also be encountered through visits to malicious websites or falling prey to spam campaigns. To broaden its reach, cybercriminals employ social engineering strategies, leveraging false software updates or enticing offers to trick more users into installation, thereby leading to infection.
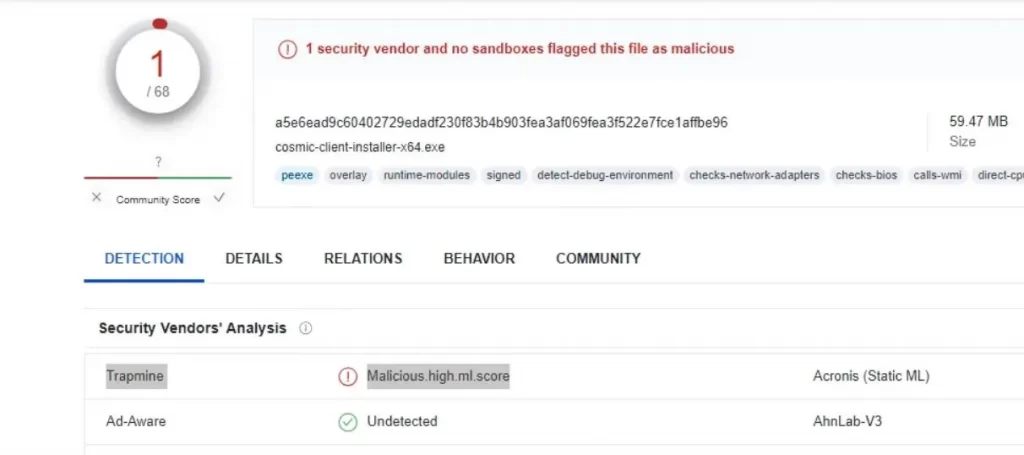
The Malicious.high.ml.score VirusTotal detection
To protect your computer from the Malicious.high.ml.score VirusTotal detection attacks, adopting a proactive defense approach is imperative. Users can improve their defense by arming themselves with powerful antivirus and anti-malware tools capable of swift detection and elimination of this stealthy Trojan. It’s equally crucial to keep their operating system and installed software up to date, as malicious actors often exploit vulnerabilities in outdated programs. Security experts also advise exercising caution with links and attachments from unfamiliar sources, particularly within emails or messages from unknown senders. Treating overly enticing offers with skepticism serves as a great preventative measure. By embracing these security guidelines, you significantly mitigate the risk of falling victim to the Malicious.high.ml.score VirusTotal detection attacks.
SUMMARY:
| Name | Malicious.high.ml.score |
| Type | Trojan |
| Detection Tool |
Malicious.high.ml.score Removal
To try and remove Malicious.high.ml.score quickly you can try this:
- Go to your browser’s settings and select More Tools (or Add-ons, depending on your browser).
- Then click on the Extensions tab.
- Look for the Malicious.high.ml.score extension (as well as any other unfamiliar ones).
- Remove Malicious.high.ml.score by clicking on the Trash Bin icon next to its name.
- Confirm and get rid of Malicious.high.ml.score and any other suspicious items.
If this does not work as described please follow our more detailed Malicious.high.ml.score removal guide below.
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide.
Some of the steps may require you to exit the page. Bookmark it for later reference.
Next, Reboot in Safe Mode (use this guide if you don’t know how to do it).
 Uninstall the Malicious.high.ml.score app and kill its processes
Uninstall the Malicious.high.ml.score app and kill its processes
The first thing you must try to do is look for any sketchy installs on your computer and uninstall anything you think may come from Malicious.high.ml.score. After that, you’ll also need to get rid of any processes that may be related to the unwanted app by searching for them in the Task Manager.
Note that sometimes an app, especially a rogue one, may ask you to install something else or keep some of its data (such as settings files) on your PC – never agree to that when trying to delete a potentially rogue software. You need to make sure that everything is removed from your PC to get rid of the malware. Also, if you aren’t allowed to go through with the uninstallation, proceed with the guide, and try again after you’ve completed everything else.
- Uninstalling the rogue app
- Killing any rogue processes
Type Apps & Features in the Start Menu, open the first result, sort the list of apps by date, and look for suspicious recently installed entries.
Click on anything you think could be linked to Malicious.high.ml.score, then select uninstall, and follow the prompts to delete the app.

Press Ctrl + Shift + Esc, click More Details (if it’s not already clicked), and look for suspicious entries that may be linked to Malicious.high.ml.score.
If you come across a questionable process, right-click it, click Open File Location, scan the files with the free online malware scanner shown below, and then delete anything that gets flagged as a threat.


After that, if the rogue process is still visible in the Task Manager, right-click it again and select End Process.
 Undo Malicious.high.ml.score changes made to different system settings
Undo Malicious.high.ml.score changes made to different system settings
It’s possible that Malicious.high.ml.score has affected various parts of your system, making changes to their settings. This can enable the malware to stay on the computer or automatically reinstall itself after you’ve seemingly deleted it. Therefore, you need to check the following elements by going to the Start Menu, searching for them, and pressing Enter to open them and to see if anything has been changed there without your approval. Then you must undo any unwanted changes made to these settings in the way shown below:
- DNS
- Hosts
- Startup
- Task
Scheduler - Services
- Registry
Type in Start Menu: View network connections
Right-click on your primary network, go to Properties, and do this:

Type in Start Menu: C:\Windows\System32\drivers\etc\hosts

Type in the Start Menu: Startup apps

Type in the Start Menu: Task Scheduler

Type in the Start Menu: Services

Type in the Start Menu: Registry Editor
Press Ctrl + F to open the search window


Leave a Comment