Malicious.moderate.ml.score
The term Malicious.moderate.ml.score might sound like tech jargon, but it’s essentially a Trojan horse detection signaled by the Bkav Pro antivirus on the VirusTotal site. Trojans are deceptive bits of software that masquerade as legitimate files, only to carry out covert operations once inside your system. This can range from stealing your personal info to making way for more aggressive malware. The trick with Trojans? They’re super sneaky. You won’t always know they’re there until something goes amiss. That’s why it’s crucial to keep your security software updated and always be wary of unfamiliar downloads or attachments. With threats like Malicious.moderate.ml.score lurking around, it’s better to be proactive than regretful.
TrapMine malicious.moderate.ml.score
TrapMine malicious.moderate.ml.score is a Trojan Horse detection on the popular VirusTotal security website. So, what does it mean? Essentially, it’s flagging a Trojan horse in the scanned file, indicating that the file is malicious and could infect your computer if you open it. Furthermore, it’s even possible that the Trojan has been activated in your system even if you haven’t opened the file, therefore requiring immediate action to secure your PC. There are many ways the Trojan could have entered your machine. Maybe you downloaded a cool-looking app, or clicked on that alluring email attachment. Sometimes, even visiting a sketchy website can initiate an unwanted download. These are classic Trojan tactics, and it’s likely that the file which is flagged with the TrapMine malicious.moderate.ml.score detection has entered your system in a similar way.
Bkav Pro malicious.moderate.ml.score
This Trojan gets flagged by other security programs too – the Bkav Pro malicious.moderate.ml.score detection, for example, refers to the same malicious threat. This malware can sneak into systems through deceptive techniques like malicious email attachments, compromised software downloads, or through misleading ads that prompt you to download seemingly legitimate files. For this reason, to prevent its entry in the future, always be cautious of unexpected email attachments and only download software from trusted sources. If a file feels suspicious, or its origin is unclear, be sure to scan the file with a trusted security program and if you get the Bkav Pro malicious.moderate.ml.score detection warning, delete the file right away and check your system for any other suspicious files, programs, and processes.
If malicious.moderate.ml.score, or another similar Trojan like W32.AIDetectMalware or malicious.high.ml.score, is already active in your system, some warning signs include: unexpected system slowdowns, frequent crashes, unfamiliar processes running in the background, or unauthorized changes in system settings. These symptoms indicate a possible compromise and underscore the importance of regular system scans and vigilance.
What is malicious.moderate.ml.score?
The Trojan named detected as Malicious.moderate.ml.score by the TrapMine security engine on VirusTotal, is a subtle but potent threat. Once it infiltrates your computer, it can stealthily monitor your activities, extract sensitive information, or manipulate system vulnerabilities to introduce additional malware. In worst-case scenarios, this Trojan can set the stage for destructive ransomware attacks, putting your files and privacy at risk. Its covert nature means many users may be unaware of its presence until significant damage is done. Recognizing this, it’s crucial to emphasize the importance of immediate action. If “Malicious.moderate.ml.score” is detected on your system, prompt removal is essential to safeguard your data and maintain system integrity.
SUMMARY:
| Name | Malicious.moderate.ml.score |
| Type | Trojan |
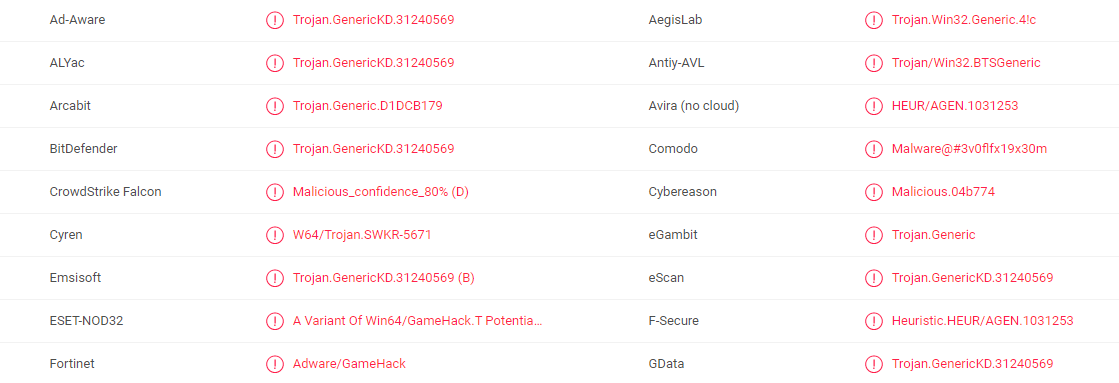
| Detection Tool |
Malicious.moderate.ml.score Removal
To try and remove Malicious.moderate.ml.score quickly you can try this:
- Go to your browser’s settings and select More Tools (or Add-ons, depending on your browser).
- Then click on the Extensions tab.
- Look for the Malicious.moderate.ml.score extension (as well as any other unfamiliar ones).
- Remove Malicious.moderate.ml.score by clicking on the Trash Bin icon next to its name.
- Confirm and get rid of Malicious.moderate.ml.score and any other suspicious items.
If this does not work as described please follow our more detailed Malicious.moderate.ml.score removal guide below.
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide.
Some of the steps may require you to exit the page. Bookmark it for later reference.
Next, Reboot in Safe Mode (use this guide if you don’t know how to do it).
 Uninstall the Malicious.moderate.ml.score app and kill its processes
Uninstall the Malicious.moderate.ml.score app and kill its processes
The first thing you must try to do is look for any sketchy installs on your computer and uninstall anything you think may come from Malicious.moderate.ml.score. After that, you’ll also need to get rid of any processes that may be related to the unwanted app by searching for them in the Task Manager.
Note that sometimes an app, especially a rogue one, may ask you to install something else or keep some of its data (such as settings files) on your PC – never agree to that when trying to delete a potentially rogue software. You need to make sure that everything is removed from your PC to get rid of the malware. Also, if you aren’t allowed to go through with the uninstallation, proceed with the guide, and try again after you’ve completed everything else.
- Uninstalling the rogue app
- Killing any rogue processes
Type Apps & Features in the Start Menu, open the first result, sort the list of apps by date, and look for suspicious recently installed entries.
Click on anything you think could be linked to Malicious.moderate.ml.score, then select uninstall, and follow the prompts to delete the app.

Press Ctrl + Shift + Esc, click More Details (if it’s not already clicked), and look for suspicious entries that may be linked to Malicious.moderate.ml.score.
If you come across a questionable process, right-click it, click Open File Location, scan the files with the free online malware scanner shown below, and then delete anything that gets flagged as a threat.


After that, if the rogue process is still visible in the Task Manager, right-click it again and select End Process.
 Undo Malicious.moderate.ml.score changes made to different system settings
Undo Malicious.moderate.ml.score changes made to different system settings
It’s possible that Malicious.moderate.ml.score has affected various parts of your system, making changes to their settings. This can enable the malware to stay on the computer or automatically reinstall itself after you’ve seemingly deleted it. Therefore, you need to check the following elements by going to the Start Menu, searching for them, and pressing Enter to open them and to see if anything has been changed there without your approval. Then you must undo any unwanted changes made to these settings in the way shown below:
- DNS
- Hosts
- Startup
- Task
Scheduler - Services
- Registry
Type in Start Menu: View network connections
Right-click on your primary network, go to Properties, and do this:

Type in Start Menu: C:\Windows\System32\drivers\etc\hosts

Type in the Start Menu: Startup apps

Type in the Start Menu: Task Scheduler

Type in the Start Menu: Services

Type in the Start Menu: Registry Editor
Press Ctrl + F to open the search window


Leave a Comment