Your device has been compromised
“Your device has been compromised” is often described as a browser hijacker for Android devices such as tablets and smartphones. The primary aim of “Your device has been compromised” is to draw the users’ attention to various types of promotional content by displaying it on their screen.
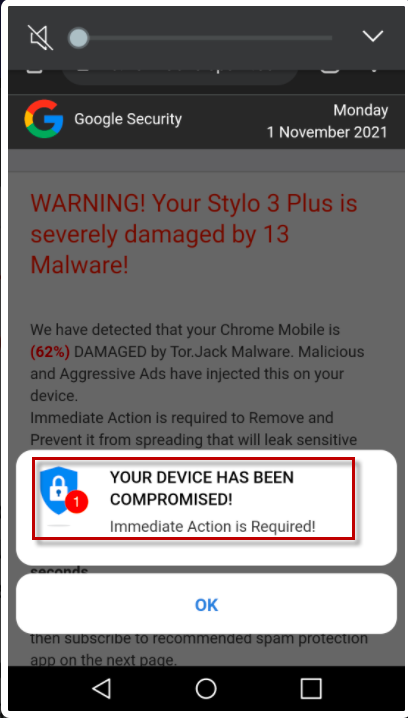
The “Your device has been compromised” infection is not as serious as a ransomware or a Trojan Horse infection, but in some instances, it may slow down your device and result in crashes and freezing.
There is one major issue with “Your device has been compromised”, and that is that it covertly obtains various rights on your device without asking your permission. Your information may be at risk because while it is on your device, this hijacker has access to information such as where you are located, the current version of your device’s operating system, what other applications you have installed, and your web browser history and preferences.
Hijackers like this one utilize this kind of information to generate appropriate advertisements and show them in accordance with your presumed interests.
The problem is that, it is very possible that the data collected from your device may end up with third-party marketers, who may sell it to organizations unknown to you. Because of this, your personal data may potentially wind up in the hands of hackers, fraudsters, or other kinds of criminals, putting your online security and privacy at risk.
What’s more, when your Android smartphone or tablet becomes bogged down by too many advertisements, pop-ups, redirects, and other aggressive advertising material, your device slows down and may even freeze.
Fortunately, “Your device has been compromised”, isn’t all that tough to remove, as long as you follow the instructions we’ve provided. The next time you are ready to download an app or see any questionable material, just be mindful of your actions. Preventing your device from being infected is always simpler than having to deal with potentially unwanted or dangerous software after it has been installed.
SUMMARY:
| Name | Your device has been compromised |
| Type | Browser Hijacker |
Remove “Your device has been compromised”
If you have an Android virus, continue with the guide below.
If you have an iPhone virus, please use our iPhone Virus Removal guide.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have a Windows virus, please use our Windows Virus Removal guide.

Whether you use the default “Internet” App for browsing or a different browser like Chrome you need to go to:
Settings/More/Application Manager/All
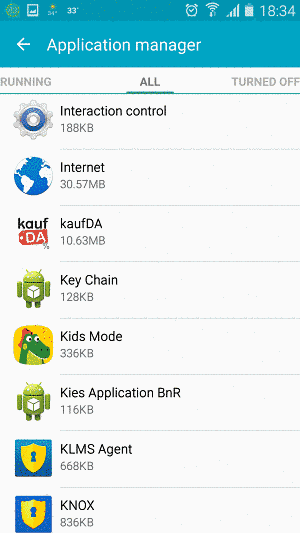
Locate the Browser/App in question and tap on it.

Now the method is effectively the same for users using both “Internet” and Chrome/Other Browsers, yet for more clarity we have provided instructions for both:
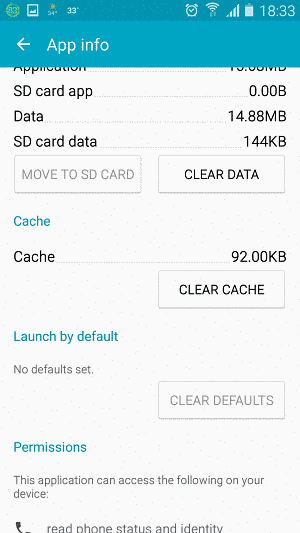
For “Internet” Browser Users:
Tap the Force Stop button.
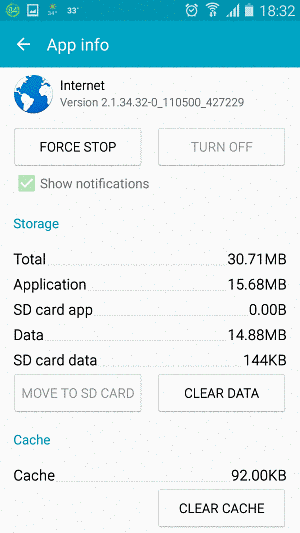
Now tap the Clear Data and Clear Cache Buttons.
For Google Chrome Users:
Click on Force Stop.
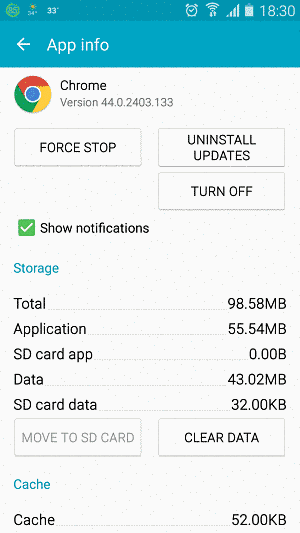
Then click on Clear Data and Clear Cache.
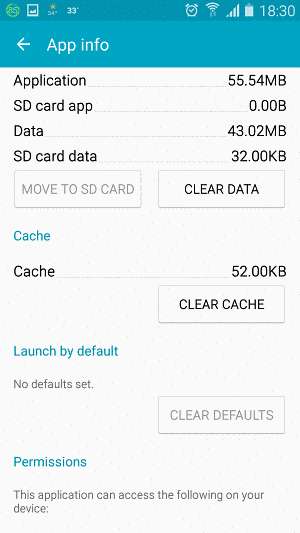

Restart your Browser. It might be a good idea to Reboot your Android device, just in case.
- Important!
If you are still seeing Ads in your browser, it is likely they are generated by the websites you visit and there is nothing you can do about it.
However, if you are seeing Adverts outside of your internet browser, then one of your installed Apps contains the problematic Adware. In this case you need to take a look at this guide.
Did we help you? Please, consider helping us by spreading the word!

Leave a Reply