Zeppelin
Zeppelin is a computer infection known as Ransomware – a form of malware that will keep your files hostage until you pay a ransom to the hackers behind it. Zeppelin secretly encrypts its victims’ files after it enters the system to make those files inaccessible.
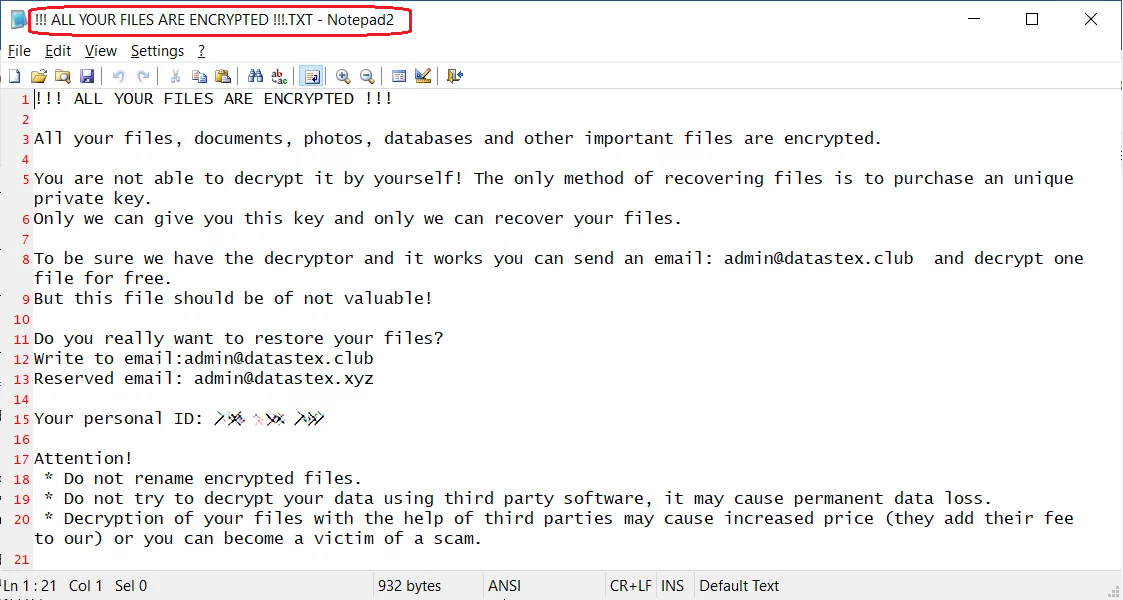
The Zeppelin Ransomware will demand from you to follow these instructions.
The Ransomware threats are everywhere and every user should know how to keep their data and computer safe from them. Here, we will be telling you about the Zeppelin virus – this is a new computer threat of the Ransomware category, one that is able to lock up all important data found on your computer in a matter of minutes and then ask you to “purchase” a private key, which is the only thing that can unlock the inaccessible files. Zeppelin doesn’t harm the infected system, and the files that it locks remain intact – they are just inaccessible to the user. To some, such a malware infection may not really sound like a big deal – after all, if there aren’t any valuable files in the system the effects of the malware shouldn’t be that problematic. This is true, but the fact is that most users do have some form of sensitive data kept on their computers – the data could be work or education-related, or it could be some form of personal data which holds sentimental value to the individual. In either case, getting your files sealed can be quite unpleasant, especially if you have no backups from which you can restore them. A backup is actually a very good countermeasure that could greatly reduce the severity of an attack by Zeppelin. However, in case you have been attacked by this virus and intend to bring back your files from a backup, make sure that you first remove Zeppelin and only then connect your backup device to the now cleaned computer. Otherwise, there’s a significant risk of your backup device getting infected and the files in it getting encrypted as well.
The Zeppelin Ransomware
The Zeppelin virus is a new Ransomware version that locks the user’s files by encrypting them and by changing their extension. The Zeppelin virus doesn’t release the locked files until the victim transfers a certain amount of money to the hacker.
If you have had your personal files locked by this Ransomware and have no backups lying around, then you’d need to carefully assess your options and figure out your priorities. One option is to pay the ransom in order to receive the decryption key but this something we’d typically advise against. The reason is you may simply never get the key from the hackers even after you make the money transfer. Those people are cyber criminals that have no fear of ever getting caught – there is nothing you, or anyone else for that matter, could make to get them to send the private key if they have simply decided that they won’t. Besides, the ransom sum is oftentimes too great for most users to afford, so this is an additional issue.
The Zeppelin file
The Zeppelin file is any piece of data on the attacked computer which this virus has managed to lock with its encryption. The Zeppelin file encryption will remain on the affected data until the corresponding decryption key is used on the inaccessible files.
Another option is to remove the malware and then try the alternative recovery methods we have posted in the second section of the removal guide for Zeppelin. The problem here is that those methods may also not always be fully effective. We cannot give promises with regard to the future of your files. Still, if you follow the steps from the guide, you should be able to get rid of the virus and you may get to restore some of your data for free.
SUMMARY:
| Name | Zeppelin |
| Type | Ransomware |
| Detection Tool |
Zeppelin Virus Removal
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Hi, Can do you decrypt files infected ZEPPELIN RANSOMWARE?. Thanks
Hi Arief Setiady, look for a decryptor on this page, if you cannot find one we cannot help you decrypt your files.