Ziggy
Ziggy is what experts identify as a file-encrypting ransomware virus. And as such, Ziggy encrypts specific files types on the infected machine, which essentially renders those files inaccessible.

The Ziggy ransomware will display a message with instructions
Hence, after a ransomware attack like this, users are left with a whole bunch of totally useless information that isn’t recognized by any software. This is mainly why viruses of this type like .Plam, Ygkz are considered highly dangerous, if not the most dangerous type of malware out there. And what makes this fact even more severe is that complying with the ransom demands of the hackers won’t necessarily guarantee the successful restoration of the encrypted data.
The hackers behind such malware variants usually try to blackmail their victims into paying rather large sums of money in exchange for a decryption key, which they claim to be the only viable solution to the encryption. However, even if you do receive one such key, there’s no telling whether it will indeed work on your files or not.
For this reason, we have designed a free removal guide which you can make use of just below the current post. And once you’ve safely removed Ziggy from your PC, you will reach the file recovery suggestions we have compiled for you in the second part of the guide. It is, of course, up to you whether to resort to them or just straight up go for the ransom payment. But it won’t cost you anything if you try to regain access to your encrypted data using alternative means first.
The Ziggy ransomware
The Ziggy virus used a complex encryption algorithm to lock users’ files and make them inaccessible. This very same encryption process also allows the Ziggy virus to avoid detection from most antivirus programs.
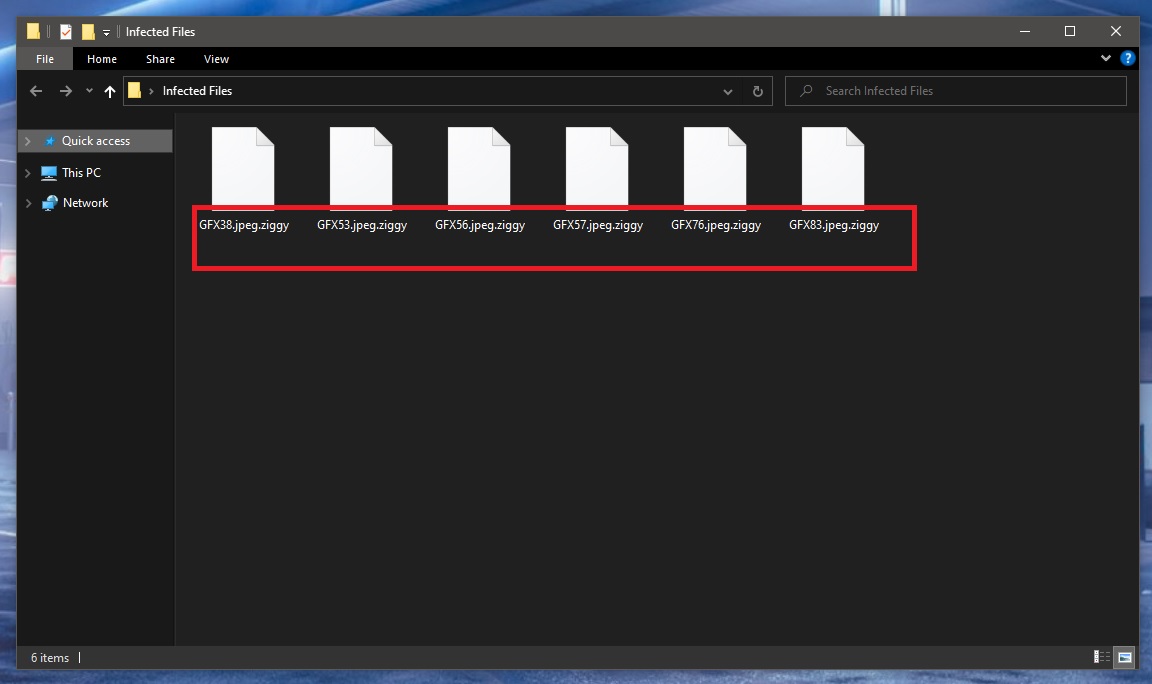
The Ziggy ransomware encrypted files
As unfair and ridiculous as it is, but it is a fact that most antivirus software doesn’t recognize the encryption process employed by viruses like Ziggy as something malicious. And indeed it is not a malicious act. This is the main trickiness of ransomware and one of the ways that cybercriminals manage to stay one step ahead of the rest of us.
But that doesn’t mean that we’re doomed to be at their mercy and we should just wait around for the next ransomware attack to happen. We aren’t powerless, and, as a matter of fact, we have a very powerful tool at our disposal that can completely disarm any malicious piece of programming of this kind. If users were to make copies of their most valuable data and frequently back it up on externals drives or even on clouds, this would automatically render any ransomware infection harmless. And of course, practicing basic safety measures when browsing the web can go a long way in preventing virus infections such as this one, as well.
The Ziggy file extension
The Ziggy file extension is the ending at the end of all encrypted files you see on your machine. The Ziggy file extension is essentially a suffix that replaces the regular file format. And because of it, no software is able to distinguish the type of file and read it.
SUMMARY:
| Name | Ziggy |
| Type | Ransomware |
| Detection Tool |
Remove Ziggy Ransomware
![]()
Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).
![]()
WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.
![]()
Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Type msconfig in the search field and hit enter. A window will pop-up:

Go in Startup —> Uncheck entries that have “Unknown” as Manufacturer.
- Please note that ransomware may even include a fake Manufacturer name to its process. Make sure you check out every process here is legitimate.
![]()
Type Regedit in the windows search field and press Enter. Once inside, press CTRL and F together and type the virus’s Name.
Search for the ransomware in your registries and delete the entries. Be extremely careful – you can damage your system if you delete entries not related to the ransomware.
Type each of the following in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete everything in Temp. The rest just check out for anything recently added. Remember to leave us a comment if you run into any trouble!
![]()
How to Decrypt Ziggy files
We have a comprehensive (and daily updated) guide on how to decrypt your files. Check it out here.
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment