Ygkz
Ygkz is a stealthy virus program recognized as a data-encrypting Ransomware that targets important user files with the goal to make them inaccessible. In a matter of minutes, Ygkz can lock up most of your files and then tell you that a ransom must be paid to recover the files.
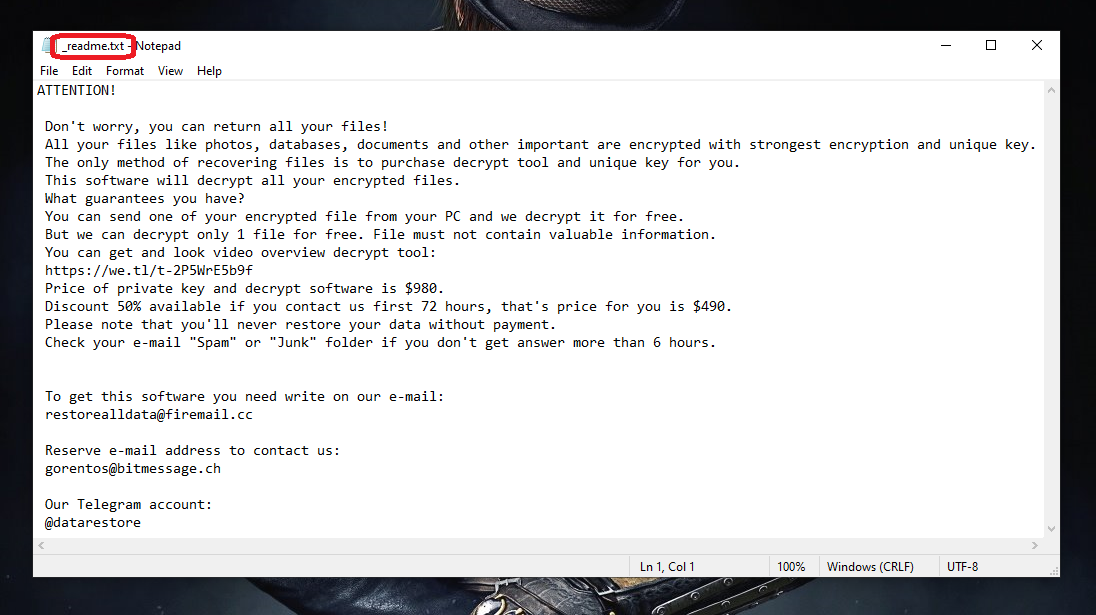
The Ygkz virus ransom note
The unauthorized encryption of your personal data files that you store in your computer can be a very unpleasant experience and could lead to many issues that you certainly don’t want to be facing. This is especially true if you have no backups of the files that have gotten encrypted and if the sealed data is related to your work or education. Unfortunately, there are many malicious programs out there that seek to do exactly that – place an advanced encryption code on the files of their victims and keep the targeted data inaccessible for an indefinite amount of time. Of course, the purpose of all this is to extort money from the victims of such malware attacks – the user whose files have gotten encrypted is supposed to pay a ransom to the people behind the malware, or else the data would never get unlocked. The malware programs responsible for this type of unauthorized file encryption are known as Ransomware cryptoviruses and we will now tell you about their latest representative – a nefarious and dangerous malware program called Ygkz.
The Ygkz virus
The Ygkz virus is a Ransomware file-encrypting virus that can quickly, and without getting detected, place encryption on all of your files, thus rendering them inaccessible. The Ygkz virus is oftentimes loaded onto users’ PCs with the help of a hidden Trojan Horse infection that serves as a backdoor.
Just like the other cryptoviruses of the Ransomware family, Ygkz a highly stealthy malware threat that can be really difficult to notice. If you are here because of this particular infection and if your data is currently inaccessible after getting encrypted by the nasty Ygkz, know that we will do our best to help you overcome this predicament without needing to pay anything to the hackers. However, unfortunately, we can’t make any promises about the future of your files. Sadly, one encrypted by Ransomware, there is no guarantee of what the future of your data may be. Still, it’s better to try out some alternatives that may be available to you such as the next Ygkz removal guide instead of directly opting for the money payment that the hackers require, hoping that this would solve everything (which it might not).
The Ygkz file
The Ygkz file is an encrypted file that has had its extension replaced by the Ransomware and can no longer be opened through conventional means. The Ygkz file will only become accessible if it gets decrypted or if the user manages to recover the file from another location.
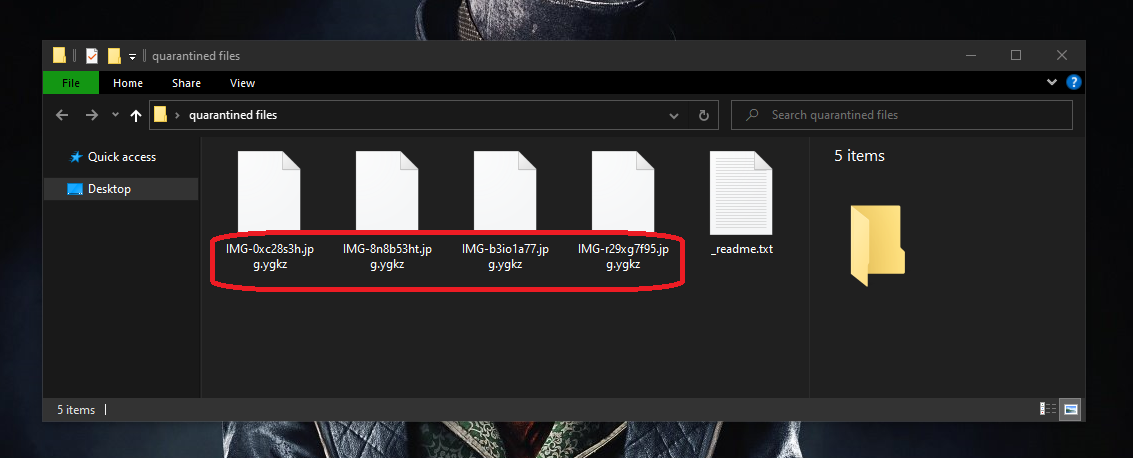
.Ygkz will encrypt your files and render them unusable.
The main reason we always tell our readers it is not a good idea to send your money to the blackmailers in hopes that they will give you a special decryption code that will give you back access to your data is because there really is no way you can be sure that the hackers behind Ygkz will actually do what they claim they would. It is perfectly possible that they take your money after you send it and give you nothing in return, thus leaving you with no way of opening your encrypted files. Also, no matter what happens with your currently encrypted data, you will still need to remove the malware from the computer so that you can at least prevent the encryption of any new files that you create or download onto your machine. As we said, the guide from this page will help you with the Ransomware’s removal. Additionally, there are several file-recovery suggestions there and though there is no guarantee that they would work in all cases ad for all files, it’s still worth giving them a try.
SUMMARY:
| Name | Ygkz |
| Type | Ransomware |
| Detection Tool |
Remove Ygkz Ransomware
![]()
Press Ctrl + Alt + Del and select Task Manager from the list of options. In the Task Manager, open the Processes tab and search for the Ransomware process. Do not expect to see Ygkz in there – malicious programs like this one tend to cover their tracks by giving their processes names that don’t raise suspicion. Still, look for processes in the list that have odd or unusual names or that consume way too much RAM or processing power despite not being linked to any program that’s running on your computer at the moment.
Once you think that you’ve found a process that could be linked to Ygkz, type its name in Google or another reputable search engine to find out more about that process if possible. In some instances, a process in the Task manager that looks sketchy may just be a regular system process from Windows, and it is important not to touch these.
If your online research tells you that the process in question is not from Windows or from another known legitimate program, go to it in the Task Manager, right-click on it, and select Open File Location.

The files stored in the location folder must be scanned for malware – we suggest using the following free online scanner that we have on our site:

If the scan tells you any of the files are infected, quit the process they are related to by right-clicking on it in the Task Manager and then select the End Process Tree option.
After that, try to delete the location folder. If you are not allowed to delete it, open the folder, and delete as many of the files in it as you can. Leave the files that can’t be deleted for now and return later, after you complete the other steps, to this folder to try to delete it once again.
![]()
WARNING! READ CAREFULLY BEFORE PROCEEDING!
It is important to complete the next steps with Safe Mode enabled because this will stop the Ransomware from running its processes in case you have missed any Ransomware processes in the previous steps. To access Safe Mode on your computer, use the steps from this guide if you need help with it.
![]()
Press Winkey and the R key from the keyboard and type msconfig in the Run window. Press Enter to open the System Configuration program and go to its Startup section. Look through the listed startup entries and if you see one or more items that seem linked to Ygkz, uncheck them and click on Apply. Also, do this for any items that are with unknown manufacturers or that seem unfamiliar to you. Of course, if a certain entry is from a program that you know and trust, there’s no need to uncheck it even if it is listed with an unknown manufacturer.
Once all suspicious startup items have been unchecked, save the changes by clicking on OK.
![]()
Check your Hosts file for malicious IPs by copying this next line into your Start Menu and selecting the first found result. This should be a notepad named Hosts and once you are in it, you must look at the bottom part of the text to see if there are lines of text written right below “LocalHost“. If there are, you must show them to us by pasting them in the comments section where we could see them. We will determine if they are from the virus and tell you what to do next.
If the IPs from your Hosts file are linked to the Ransomware, you will have to manually delete them from the file and then apply and save the changes by selecting the File menu and then selecting Save.
![]()
Important Note!: This step will involve making changes in the PC Registry where important OS settings are stored. You will have to delete items related to the virus, but it can sometimes be difficult to tell if a given item in the Registry is malicious or is from a legitimate program or from the OS. Deleting the wrong thing could damage and destabilize the system. Because of this, you must only delete items that you are certain are related to Ygkz, and in case of uncertainty, you must first ask us for assistance through the comments section so that you don’t end up deleting something that you shouldn’t.
To start the Registry Editor, you must go to your Start Menu and type “regedit” in it. An icon named regedit.exe should appear on the screen – open it and Windows will request an Administrator’s permission to start the program. Click on Yes to start the Registry Editor and when it starts go to the Edit menu and select Find. In the find window, type Ygkz and select the Find Next option to start the search. If the search finds an item with the Ransomware name, delete the item and repeat the search to find the next one. Keep searching and deleting until all Ygkz items in the Registry have been cleaned. Then, from the sidebar to the left, find these three directories.
- HKEY_CURRENT_USER > Software
- HKEY_CURRENT_USER > Software > Microsoft > Windows > CurrentVersion > Run
- HKEY_CURRENT_USER > Software > Microsoft > Internet Explorer > Main
In those directories, you must look for folders that have unusual names that don’t seem to belong there. For instance, a folder with a very long name that has random characters in it can be considered suspicious, and you may have to delete it. Again, we must remind you that if you are not sure about anything, the comments section on this page is always open, and you can ask us for our assistance through it.
![]()
Paste the first of the following lines in the Start Menu and hit the Enter button. When the respective folder opens, sort the files in it by date and delete the most recent ones – everything created/last modified after the Ransomware infection occurred.
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Do the same thing with the remaining four folders but once you get to the Temp folder, instead of deleting only the most recent files, delete all files that are stored in it.
Finally, remember to go back to the location folder from the first step and delete it if you were not able to do that at an earlier time.
How to Decrypt Ygkz files
Successful file decryption usually requires that you first remove the virus from your computer, so it is important to do that before you attempt to bring back your locked files. However, simply removing Ygkz will not recover your encrypted files automatically. Because of this, we’ve prepared a separate decryption guide that you can visit on our site and where you can find instructions that may help you bring back your data without giving the hackers behind Ygkz any money for the ransom. Before you go to our How to Decrypt Ransomware guide, however, you must make sure that the virus is truly gone from the system. If there are any strange suspicious files left on your computer, you can always use our free online scanner to test them for malware in order to delete them if they are flagged as hazardous.
Final Notes
The manual instructions should help most of you get rid of the malicious Ygkz threat. In case the malware still seems to be in your machine even after you’ve done everything as explained and/or if you think there may be a second threat hidden in the computer, we recommend that you try the advanced professional anti-malware program that you can find linked in the current guide. It can both quickly located and delete any malware that may currently be in your system and also keep potential future infections at bay.

Leave a Comment