*Zput is a variant of Stop/DJVU. Source of claim SH can remove it.
Zput File
The Zput encryption technique serves as the linchpin of the ransomware’s malicious agenda. Picture your favorite song, suddenly shifted into a bizarre frequency—whole in form, yet alien to the ears. While the core of the file remains untouched, its comprehension undergoes a seismic shift, becoming an enigma without the distinctive decryption password. The devious design of this ransomware is extensive, affecting diverse files from invaluable academic research to personal diaries, underscoring its relentless reach. The objective is simple: ensnare a file of consequence to the user, compelling them to succumb to the subsequent ransom demands resulting from the Zput encryption process.
How to decrypt Zput ransomware files?
In the convoluted realm of Zput ransomware, ensuring complete decryption of affected files remains a challenge, with some strategies proving more effective than the rest. To navigate this digital labyrinth, it’s prudent to first purge the system of the malignant software, taking cues from the comprehensive guidance offered on this platform. Subsequently, leveraging the gratis decryptor we’ve made available might just offer a glimmer of hope, facilitating the retrieval of your compromised digital assets.
How to remove the Zput ransomware virus and restore the files?
Confronting the Zput ransomware necessitates a meticulous system sweep to unearth and obliterate any malevolent traces. We’ve curated a step-by-step guide, supplemented by a state-of-the-art removal tool, to streamline this process for you. Once the ransomware is ousted, those seeking to restore their ensnared files can explore the potential of the free data recovery utility, conveniently anchored below our provided guidelines.
Zput Virus
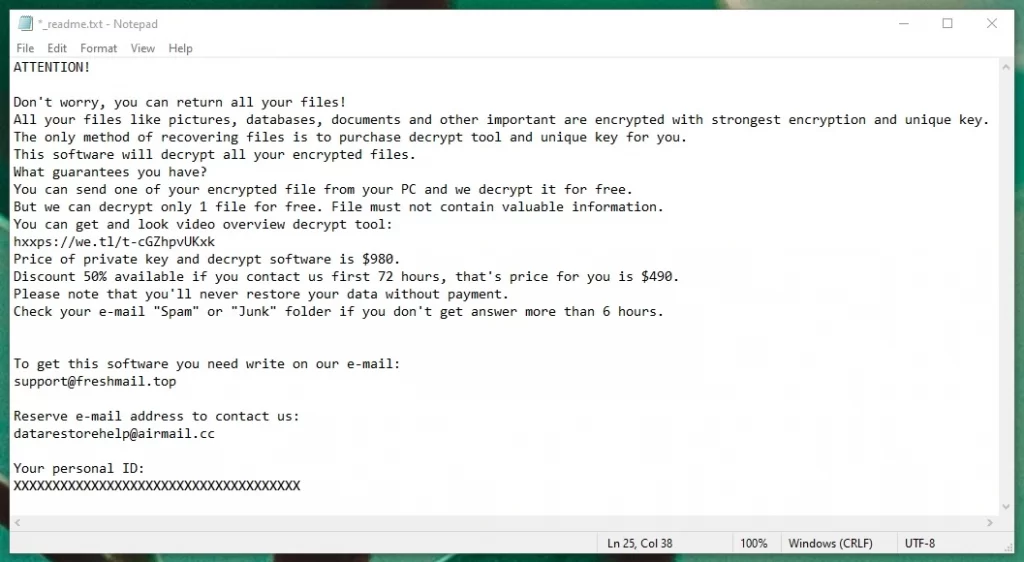
Positioned distinctively within the malware landscape, the Zput virus follows a singular modus operandi. Contrary to many digital adversaries that slyly pilfer or corrupt information, ransomware boldly holds your data hostage, presenting you with a ransom ultimatum detailing the payment specifics. After completing its encryption dance, the Zput virus sheds its cloak of invisibility. However, by this juncture, pre-emptive actions are futile. With data in the ransomware’s clutches, the only recourse is a methodical assessment of the predicament and strategizing an optimal recovery route. It’s worth noting that rushing to meet the ransom, without exploring other viable options, often isn’t the wisest course of action.
Zput
The art of disseminating Zput ransomware epitomizes cunning digital stratagems. The architects of this vile software cleverly embed it within seemingly harmless documents, ensnaring the naive. A favored subterfuge involves harnessing Trojan gateways. Once a Trojan establishes its foothold, it clears the path for the ransomware, facilitating its silent, unnoticed encryption onslaught. But Trojan-assisted deployments are just a fraction of the avenues leveraged for Zput and its kin, such as Itqw or Itrz. Crafty pop-up advertisements, unlicensed software downloads, deceptive websites, and phishing emails are some of the diverse conduits hackers exploit to maximize their malevolent software’s reach.
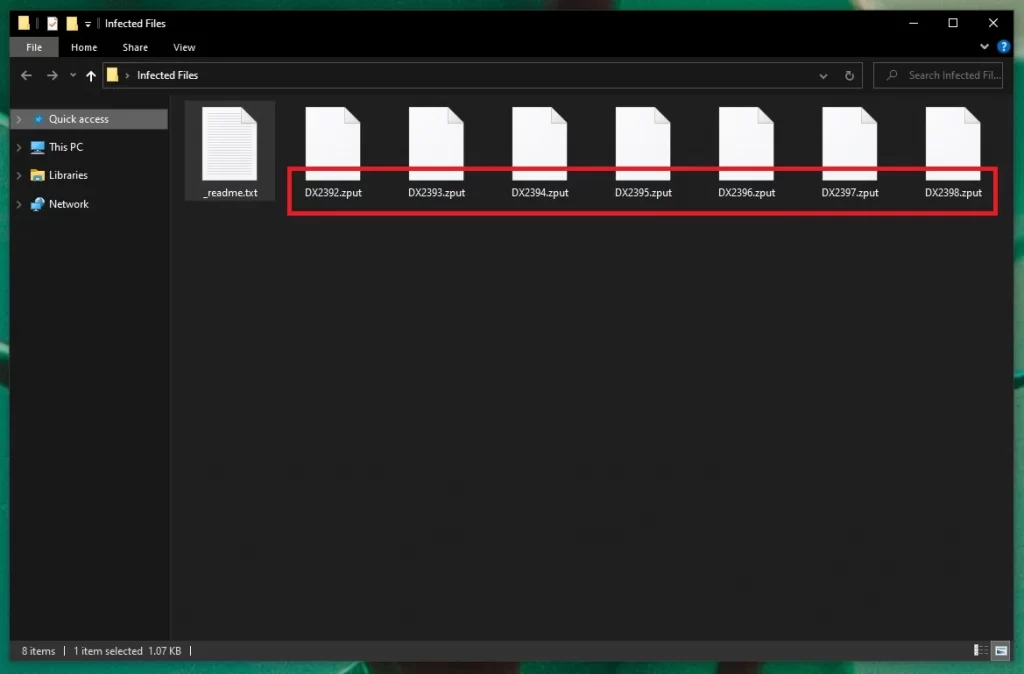
.Zput
In the wake of a successful attack by this ransomware, the targeted files typically sport the .Zput tag. This appendage isn’t merely symbolic; it signifies a file’s confinement. One could surmise that merely shedding this extension would grant file access, but this belief is flawed. The true hurdle is the convoluted encryption underlying the extension. Merely discarding the tag won’t reinstate the file’s original state. Confronting the .Zput file extension underscores the daunting quest users embark on to reclaim their digital assets. In such dire straits, the paramount approach is to maintain composure and deliberate the predicament systematically. Perhaps the compromised data has a backup, or its significance is negligible, enabling users to reset their systems, ensuring a pristine start sans the ransomware’s shadow.
Zput Extension
Stumbling upon a file tagged with the Zput extension is akin to discovering your digital assets have been taken hostage. These files, outwardly unaltered, are shackled by a formidable encryption protocol. Alongside this unsettling revelation, users typically unearth a digital ultimatum authored by the culprits. This foreboding message delineates the stark scenario: encryption has taken hold, marked by the Zput extension, and a payment is expected to reverse the damage. This message serves dual roles: it’s both informative and manipulative. While capitulating to the financial demand might seem tempting, it’s crucial to realize that succumbing doesn’t guarantee file liberation; cybercriminals may simply pocket the sum without returning your data’s accessibility.
Zput Ransomware
Zput ransomware exhibits a predatory omnivorousness, preying on everything from personal digital keepsakes to indispensable enterprise records. When entangled in its nefarious snare, feasible counteractions might appear scarce. Sure, acquiescing to the ransom is a possibility, yet it’s an inadvisable course of action that lacks any assurance of data revival. For those weighing the ransom’s demand against their data’s worth and discerning a mismatch, there exists the radical recourse of a system wipe – eliminating both the malevolent software and its captive data. Additionally, there’s the pathway of employing the following guide to expunge the Zput ransomware infection, retaining the affected files, and endeavoring to harness the included free decryption tool to potentially salvage a portion of your compromised data.
What is Zput file?
When the term “Zput file” is broached, it refers to a piece of data that has succumbed to this specific ransomware’s encryption, now lying dormant and inaccessible without its corresponding decryption cipher. To forestall your digital assets from ever adopting the “Zput file” label, vigilant preemptive measures are key: allocate funds for esteemed cybersecurity tools, consistently mirror data to external storage mediums, and approach unrequested electronic communications or questionable online resources with a discerning eye. The old adage remains relevant: fortifying against ransomware’s looming menace is the optimal strategy. Regrettably, if you’re already confronted by a ransom ultimatum sans prior preparations, navigating the predicament becomes considerably more arduous. Under such circumstances, our pressing advice would be to consult the ensuing tutorial.
SUMMARY:
| Name | Zput |
| Type | Ransomware |
| Detection Tool |
*Zput is a variant of Stop/DJVU. Source of claim SH can remove it.
Zput Ransomware Removal

Your computer may need to restart several times during the removal of Zput. Therefore, it is a good idea to bookmark this page with instructions in your browser or simply open it on another device, so you can refer to it forth and back as many times as you need.
Next, restart the system in Safe Mode (please use the instructions from the link) and once you do that, follow the instructions below.
Find the Windows search bar (in the Start menu or bottom left for Windows 10) and type msconfig in it. Press Enter and you will see a System Configuration window:

Select Startup and Uncheck any entries that you believe are not legitimate and could be linked to the ransomware that you want to remove.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Zput is a variant of Stop/DJVU. Source of claim SH can remove it.
After disabling the suspicious-looking entries from the Startup list, close System Configuration and press CTRL + SHIFT + ESC from the keyboard.
Next, in the Task Manager, click Processes and, just as you did above, search for entries that look suspicious, have unusual name, use too much CPU and Memory, etc., and try to determine if they are dangerous.
When a specific process grabs your attention, right-click on it and select Open File Location to view its files.

If you can’t decide about the legitimacy of the files just by looking at them, use the powerful free scanner below to check them:

If malware is found in them, end the processes they belong to and delete their folders.

In some cases, malicious IP addresses may be added to the Hosts file of your computer as a result of a ransomware infection. Therefore, it is a good idea to open that file by pasting the line written below in the windows search bar and pressing Enter:
notepad %windir%/system32/Drivers/etc/hosts
Next, find Localhost in the text and check if some questionable IPs have been added there.

If you detect something disturbing, don’t rush to delete it. Instead, please write to us in the comments with a copy of what you have found, and we will reply to you with advice on what to do.

*Zput is a variant of Stop/DJVU. Source of claim SH can remove it.
Next, you need to search for Zput in the registry of your system and delete any entries that are found there. To do that, first open the Registry Editor by heading to the windows search bar and typing Regedit it. Next, press Enter.
In the Registry Editor, press CTRL and F from the keyboard and write the exact name of the ransomware infection that you want to remove inside the Find box that appears on the screen. Then, search for entries that are matching that name. If anything appears in the results, it most likely should be deleted.
If you are not sure that it belongs to the infection, however, don’t delete anything because this may corrupt your OS. Instead, use a professional removal tool to scan the system and clean your registry automatically. Next, close the editor and go to the windows search field. In it, type each of the following and search for any recently added files and folders in there:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
At the end, when you open Temp, select everything there and remove it. By doing this, you will also remove any temporary files that the ransomware might have created.

How to Decrypt Zput files
When faced with the daunting reality of a cyber-attack, understanding the nature of the threat is paramount. If your files suddenly appear with unfamiliar extensions, it could hint at the ransomware variant that has breached your defenses. In this context, the Zput ransomware is one such malicious agent that’s been making rounds lately.
Once you’ve recognized the specific ransomware, it is of utmost importance to cleanse your system of the lingering malware to prevent further encryption or potential damage. To ensure this, we suggest meticulously following the step-by-step guide mentioned above, complemented by the specialized removal tool embedded therein.
New Djvu Ransomware
Emerging from the notorious Djvu ransomware lineage, the STOP Djvu variants have been wreaking havoc, creating worldwide distress by encrypting users’ essential files. Zput belongs to this Djvu subtype and its characteristic signature is the addition of the .Zput extension that it appends to the files it encrypts. If your files have received the Zput extension, then it means that this is the specific ransomware that you’re dealing with.
While the appearance of this new strain has understandably raised concerns, there’s a silver lining. Files encrypted by STOP Djvu, especially those that utilized an offline key during encryption, aren’t forever lost. A beacon of hope for affected users is the decryption tool crafted specifically to counteract the effects of this ransomware. The tool can be sourced from the following link:
https://www.emsisoft.com/ransomware-decryption-tools/stop-djvu
After procuring the tool, initiate its operation with elevated privileges. Upon being prompted, confirm your action by opting for “Yes.” It’s essential to acquaint oneself with the tool’s licensing terms and the brief overview provided. To commence the decryption process, select the ‘Decrypt’ button. While optimism is encouraged, it’s also crucial to remain cognizant of the inherent challenges, especially if faced with unknown offline keys or if the ransomware employed online encryption tactics.

Leave a Comment