This page aims to help you remove 30tab.com “Virus”. Our removal instructions work for Chrome, Firefox and Internet Explorer, as well as every version of Windows.
As an intro we need to say that browser hijackers represent a kind of software that could be capable of modifying your browsers as soon as they have become components of your system. What you could expect to happen due to the inflicted alterations of your Firefox, Chrome, Opera or Explorer (or any other browser) apps, is explained below:
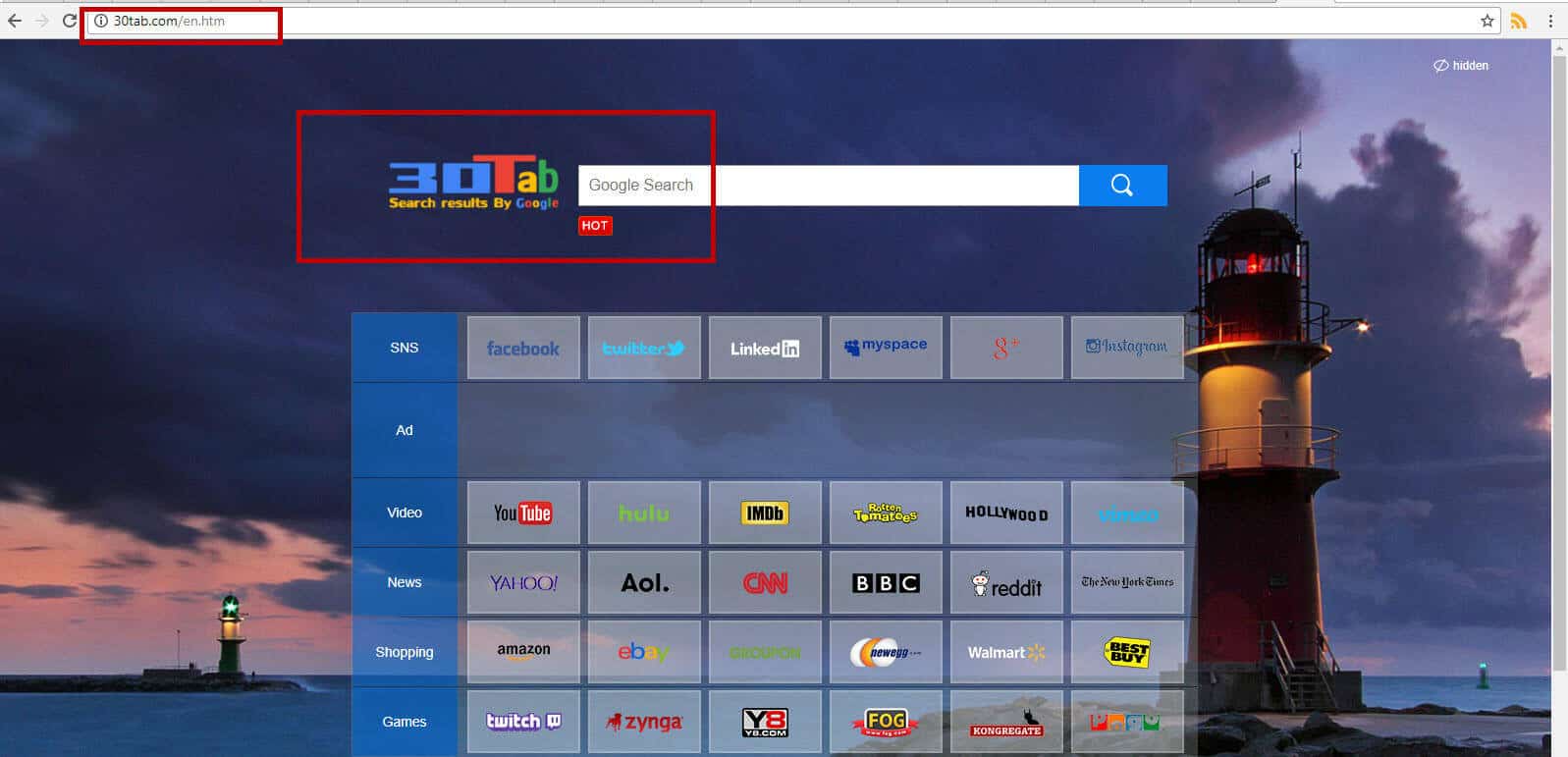
- there might be some absolutely new and unfamiliar new search engines and homepages set;
- some redirection processes to locations you have never wanted to visit might be conducted;
- last but not least, your browser might start broadcasting such a great number of ads that your browser tabs may get fully covered, and your surfing experience might be interrupted.
The exact program from this software category that we will be discussing below is called 30tab.com. It may possess the traits we have mentioned above so far.
Expected traits of browser hijackers as a whole:
The typical representatives of this software category act exactly in the way we have mentioned before. They could simply become a part of your system, access and alter the settings of your browser apps. What’s more, such a program may perform a very thorough review of your browsing history with the purpose of being able to later broadcast just the ads that may suit your personal preferences and interests. Furthermore, oftentimes the mass generation of ads may become a reason for a total slowdown of your PC – an effect that may further irritate and annoy you. However, as far as we are informed, hijackers have no malicious traits.
This type of programs can merely serve some marketing-related purposes. The true goal of the so-called hijackers is to promote all sorts of products, web platforms, search engines, browser homepages – and whatever other product or service might be in need of advertising. This marketing-directed behavior really explains the hijackers’ possible consequences. Nonetheless, do not go crazy – advertising is legitimate and present everywhere today!
What makes 30tab.com different from the most dangerous viruses? Is it entirely harmless?
Actual malware like the viruses related to Ransomware and Trojans can and normally will harm you and your system. On the contrary, though, browser hijackers can never do anything damaging. For example, in case your computer has caught a Ransomware program, all of the data you use on a regular basis will be in a grave danger. You may be interested in the reason why and it is the fact that such viruses are very likely and known to encode data, and request a ransom in exchange for the encrypted files. If you are having trouble with a Trojan horse infection, you may be experiencing many potential issues, like identity theft, destruction of data, corruption, and system crashes. Luckily, these effects are unlikely when we talk about any infection caused by any hijacker.
Where and in what way you could catch 30tab.com:
The most frequent sources of ad-broadcasting software (including hijackers and Adware) are these: torrents, shareware, spam and program bundles. The mentioned bundles indeed represent combos of games, different versions of Adware and hijackers, various apps and some newly developed programs. Such bundles are available for free practically everywhere on the Internet. Despite that, it is not the process of downloading any set of software that infects your system with a hijacker, it is in fact the way you perform the installation. All the software you get from the web must be installed in the most elaborate and cautious way forthe purpose of avoiding all irritating possible infections. Here we have described the way of installing any program properly and safely. Search for the Advanced installation option when the wizard is finally displayed. In some installers this feature might be named Custom [or Customized]. What’s really vital is that such a way of installing always lets you safely install the needed bundle, and manually select what to leave behind and what to put into your computer.
If you would like to maintain your system free of any unwanted programs, though, it is a good idea to install the most effective anti-virus program you can find. Buy the best one – definitely you will have no regrets later. As for the removal of 30tab.com, we recommend you follow the instructions we have provided below in the Removal Guide.
SUMMARY:
| Name | 30tab.com |
| Type | Browser Hijacker |
| Detection Tool |
30tab.com “Virus” Removal
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.

Leave a Comment