This page aims to help you remove [email protected] Ransomware Virus for free. Our instructions also cover how any .id-{YourID}.[[email protected]] file can be recovered.
In case that a scary ransom-demanding notification has appeared on your screen and all of a sudden it became impossible to open or use any of your files, then you’ve most likely become a victim of an incredibly hazardous malware from the Ransomware family named [email protected]. You have probably been informed by the ransom notification that your information has been locked with a strong encryption algorithm and you will need to pay a certain amount of money if you want to get it back.
If you’ve reached our page, though, you’re likely wondering if there’s a way around this threat. Fortunately, there might be something that might help you and our “How to remove” team will do its best to assist you cope with this highly dangerous Ransomware infection. If you stay with us, you will find some detailed instructions, neatly organized in a removal guide, which may help you remove [email protected] from your computer. You will also find some file-recovery suggestions which don’t involve paying ransom to some anonymous hackers. But first, let us give you some more light on this Ransomware and its specifics.
The [email protected] virus
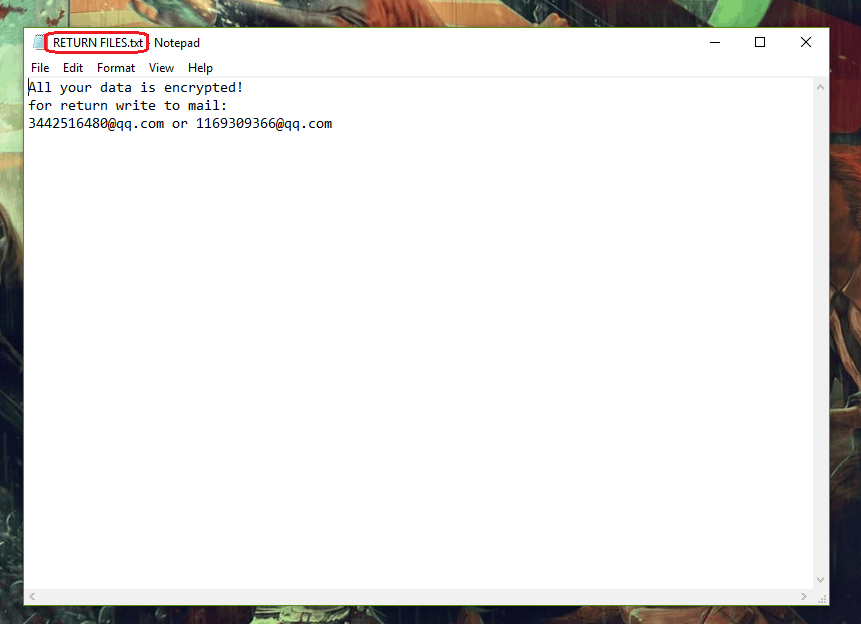
The [email protected] Virus will leave this message in a RETURN FILES.txt file
The moment you are infected with a Ransomware, it instantly begins to infiltrate your hard drive with the idea to encrypt a list of frequently used files. Once they are found, the cryptovirus converts them into a complex symbol combination that can not be opened and then changes their file extension. This entire process can run quietly in the background until all the information is encrypted, so it is really difficult to identify the danger before the ransom note appears on the screen and informs the victims of the malicious outcomes. The note typically includes a message from the criminals and guidelines on how to make the payment. In exchange for your money, the crooks promise to send you a unique key for decryption, which can bring your files to their previous state. The crooks generally ask for Bitcoins, as this is an untraceable online currency that helps them stay anonymous to the legal authorities.
The [email protected] file encryption
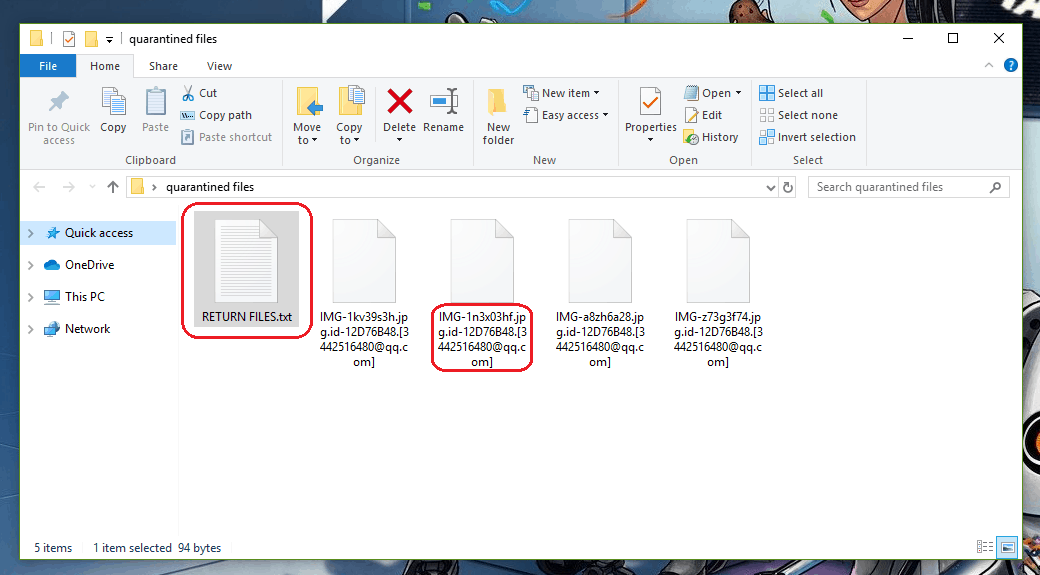
A screenshot of an encrypted [email protected] File
Once infected with [email protected], you don’t have many choices. You must either fulfill the hackers’ requirements and pay the demanded ransom, or you must find a way to remove the infection by yourself and try to restore your files without a key for decryption. While both alternatives hide their risks, we think that the worst is submitting to some unscrupulous cyber criminals who only want to extort some money by keeping user data hostage. Many security experts would advise you the same, since the bitter experience of the victims who paid the ransom and never received a decryption key has shown how unfair this “deal” is. And while no guarantee is given when one enters into a deal with unscrupulous online crooks, it should be clear that the infection should be removed. This is essential if you want to be able to use your computer after the attack, as well as to potentially recover some of your files. Therefore, we suggest you follow the instructions in the removal guide below and remove [email protected]. Once you do that, you can try to restore some of your files from system backups, external drives or a cloud or look at our frequently updated list of free decryptors.
SUMMARY:
| Name | [email protected] |
| Type | Ransomware |
| Detection Tool |
[email protected] Ransomware Virus Removal
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Leave a Comment