This page aims to help you remove 4yendex. These 4yendex removal instructions work for Chrome, Firefox and Internet Explorer, as well as every version of Windows.
If you are looking for information regarding 4yendex, then you have come to the right place. This article will aid you in resolving any issues that you might have with this unwanted piece of software. Additionally, in our removal guide below, you will also learn how to remove the intrusive application from your machine, so it will no longer bother you. However, it’s preferable that you read all the information that we have to offer you in the following paragraphs, because knowledge is key to handling such undesirable programs.
Browser Hijackers and their purpose
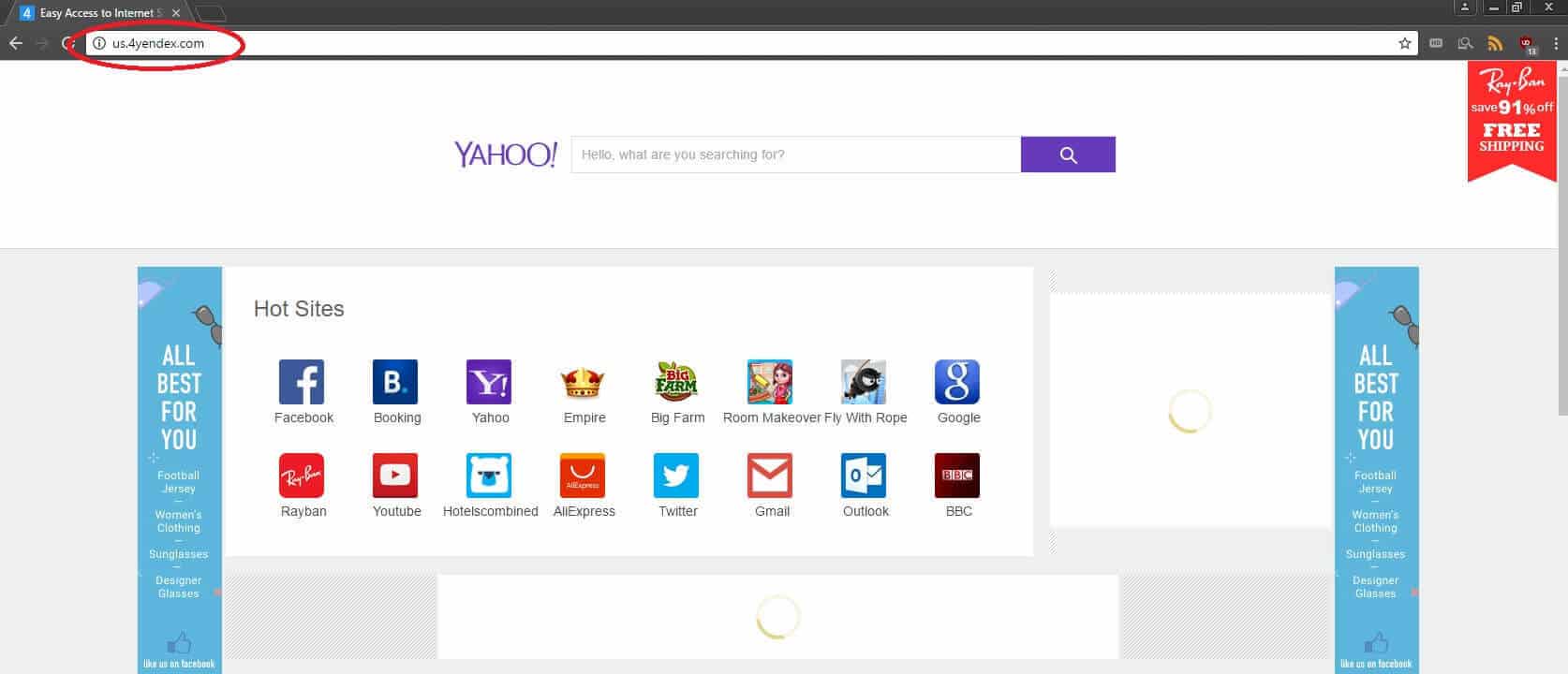
4yendex is a program of the Browser Hijacker type. Software that falls under this category aims to integrate itself onto your Chrome, Firefox or IE browser, causing different alterations to it, such as a changed homepage or search engine and occasional sudden page redirects without your permission. There are also several other potential negative traits to a Browser Hijacker such as 4yendex that we will get into later. Most programs you have on your computer are probably there because they help you in a certain way or provide you with some sort of useful function. However, if you have had 4yendex installed on your machine, the chances are that you are not getting any actual benefit from it. This is because applications of this type for the most part are being developed for the sole purpose of benefiting their creators. Usually, this is done by employing a variety of revenue-earning techniques that most of the time have something to do with the online marketing industry. The Pay-per-click scheme, gathering valuable marketing data from the user and promoting other products that are paid are some of the most common ways, in which Browser Hijackers are used to help their creators gain income. On some occasions, programs such as 4yendex could seem to contain some useful function for the actual user, but even if this is the case, those functions are something minor that is probably not worth the intrusive and unwanted aspects of the otherwise unwanted Hijacker.
PUP
Browser Hijackers are one of the many types of PUP’s. This abbreviation stands for potentially unwanted program – exactly what 4yendex is. It is important for you to realize that despite its irritating behavior, this piece of software is not some sort of malicious and harmful virus, so there is no need for panic. Actual viruses such as Trojan Horses and Ransomware are what you should be really concerned with. If it is only the Hijacker that is bothering you, then it should all be fine, as long as you make sure to remove it as soon as you can.
Why it is important to get rid of the Hijacker
Sure, applications such as 4yendex are not some sort of dangerous and noxious Ransomware viruses, but they are still unwanted. Therefore, the sooner you get rid of them – the better. In addition to what we already mentioned as potential negative effects that a Browser Hijacker might have on your PC, here are some more things that you need to be aware of when it comes to this particular type of PUP’s:
- They can spy on your browsing activities. While this might sound malicious, the acquired data is most of the time used solely for promoting purposes. Still, having an unwanted program looking through your online history is certainly something you would not want.
- Hijackers tend to display intrusive pop-ups and false/exaggerated error messages. This is typically done in order to persuade the user to buy some sort of system optimization tool that would supposedly fix the error. The thing is that oftentimes there is no such error to begin with or in some cases the said tool might not even be as helpful as it is marketed to be. Remember, good quality products do not need to be promoted via this sort of overly-intrusive advertising techniques.
- 4yendex may slow down your PC. In many cases the system resource requirements of such programs might turn out to be quite considerable, which could lead to a significant decrease of the machine’s productivity capabilities.
Stay safe
As soon as you go through our removal guide, you should have no problem getting rid of the bothersome piece of programming that is currently nagging you. However, you need to understand that this is only half the battle. The other half is keeping your machine clean and safe from any future Hijacker invasions. For that reason, from now on make sure to download content only from reputable sites while staying away from any shady and illegal ones. Also, avoid opening any suspicious links or e-mail messages that get sent to you – spam is often used by Hijacker developers to spread their products. Last but not least, always utilize the Custom setup option when installing new programs. Oftentimes the installer file is actually a software bundle that might contain unwanted add-ons such as 4yendex. However, when you use the Custom settings instead of the Quick ones, you’d be able to leave out any added content out of the installation by unchecking it.
SUMMARY:
| Name | 4yendex |
| Type | Browser Hijacker |
| Detection Tool |
4yendex Removal
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.

Leave a Comment