54bb47h
54bb47h is a ransomware cryptovirus that cybercriminals use to extort money from unsuspecting web users. 54bb47h renders digital files inaccessible through encryption and then blackmails the owners of said files to pay a ransom to access them.
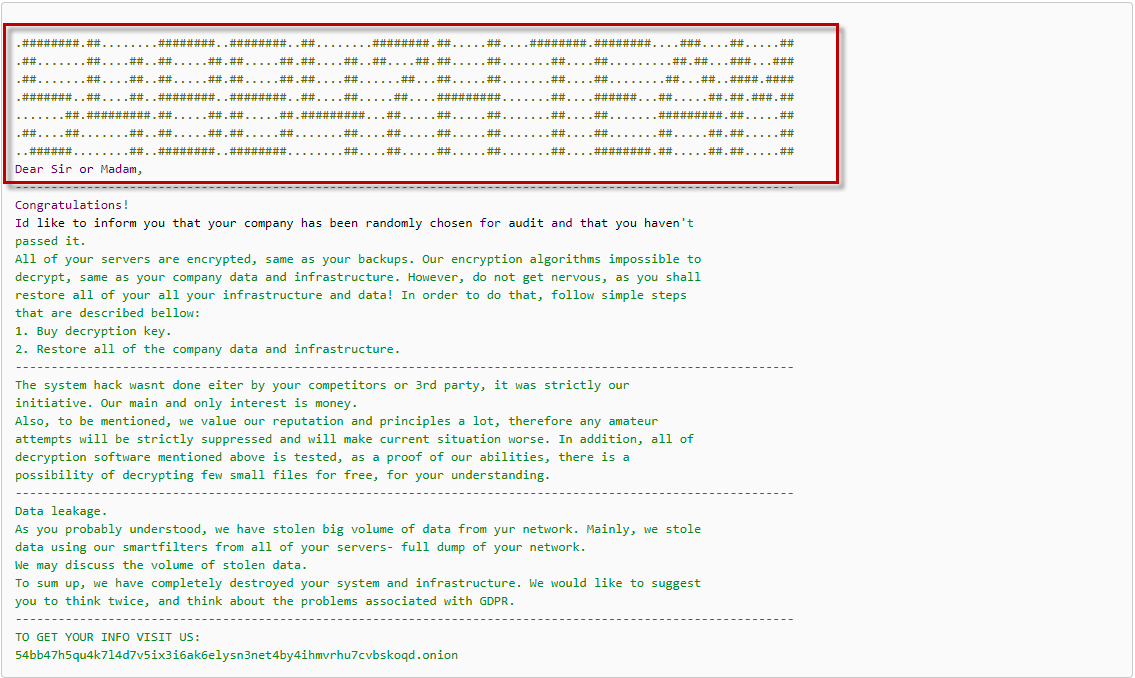
The 54bb47h virus ransom note
One of the new ransomware viruses that has been reported to our “How to remove” team is a threat called 54bb47h. This threat can secretly compromise a computer and encrypt the files stored there without visible symptoms. The entire scheme is based upon depriving you of access to your own information so that the attackers can then blackmail you to pay them some money to regain your access. In this post, however, we’re going to show you a possible roundabout to the ransom payment as well as a way to remove 54bb47h from your computer. That’s why, at the end of the page, we will give you a set of instructions on how to eliminate this terrible threat and how to recover some of your files from system backups.
The 54bb47h virus
The 54bb47h virus is a malicious software infection programmed to encrypt the data stored on a computer and to blackmail its owners to pay a ransom for its decryption. The 54bb47h virus will typically notify its victims about the attack by displaying a ransom message on the screen of the infected computer.
54bb47h employs advanced methods to infect as many computers as possible and to stay hidden inside the system until it completes its agenda. On top of that, this ransomware uses a complex encryption code to guarantee that you can’t get back your data unless you pay for the required money. That’s another thing that makes it so difficult to deal with this particular category of malware. However, it is important to mention that even paying the required money and fulfilling all the ransom demands cannot guarantee that your files will be recovered to their previous state. Unfortunately, even the attackers who’ve created 54bb47h and Maql may not be able to reverse the complex file encryption that has been applied to your information. Therefore, there are many cases where the victims who pay for a decryption key to the hackers receive a key that simply does not work and that fails to recover the encrypted data. The cases where the crooks simply “forget” to send a decryption key are also quite common. Therefore, if you’ve already been attacked by 54bb47h, we would NOT suggest resorting to the ransom payment.
The 54bb47h file decryption
The 54bb47h file decryption is a file-decoding process that is supposed to recover the encrypted user data to its previous state. The 54bb47h file decryption, however, is not guaranteed even if the victims pay for a decryption key.
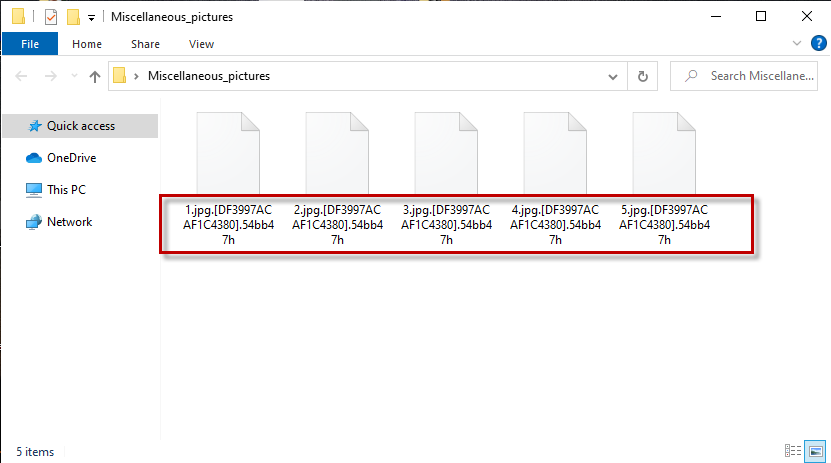
The 54bb47h file virus ransomware
But what choices are you left with? Now that some of your most valuable images, reports, documents, plans, projects, etc. have become inaccessible, it would be ideal if you have personal backups from where to recover them. Another option you can try is to extort some of your files from system backups. Concrete instructions on that you can find in the removal guide below, but before you give a try to any file-recovery suggestions, you should first remove 54bb47h from your system. This is important because if the ransomware is active on your computer, it will most probably encrypt your files again, along with your backup sources. So make sure you remove the infection and scan your computer with reliable security software to ensure no ransomware leftovers have remained hidden in your system.
SUMMARY:
| Name | 54bb47h |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Symptoms | Very few and unnoticeable ones before the ransom notification comes up. |
| Distribution Method | From fake ads and fake system requests to spam emails and contagious web pages. |
| Data Recovery Tool | Not Available |
| Detection Tool |
54bb47h Ransomware Removal
![]()
Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).
![]()
WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.
![]()
Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Type msconfig in the search field and hit enter. A window will pop-up:

Go in Startup —> Uncheck entries that have “Unknown” as Manufacturer.
- Please note that ransomware may even include a fake Manufacturer name to its process. Make sure you check out every process here is legitimate.
![]()
Type Regedit in the windows search field and press Enter. Once inside, press CTRL and F together and type the virus’s Name.
Search for the ransomware in your registries and delete the entries. Be extremely careful – you can damage your system if you delete entries not related to the ransomware.
Type each of the following in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete everything in Temp. The rest just check out for anything recently added. Remember to leave us a comment if you run into any trouble!
![]()
How to Decrypt 54bb47h files
We have a comprehensive (and daily updated) guide on how to decrypt your files. Check it out here.
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment