The Taidoor Malware
The Taidoor Remote Access Trojan (RAT) has been around since 2008, according to US Government agencies.
Taidoor, a new strain of malware used by Chinese government hackers during recent security breaches, was announced today with a joint alert by three agencies of the US administration.
The alert was drawn up by the Federal Bureau of Investigations (FBI), the Department of Homeland Security’s Cybersecurity and Infrastructure Security Agency (DHS CISA), and the Department of Defense’s Cyber Command (DOD CyberCom).
CISA, DOD and FBI have recently started working together to issue joint reports on emerging malware threats. The first joint alert was published in February this year when the three agencies alerted about six new malware strains created by state-sponsored North Korean hackers. Nevertheless, their latest joint alert warns of new malware coming from China.
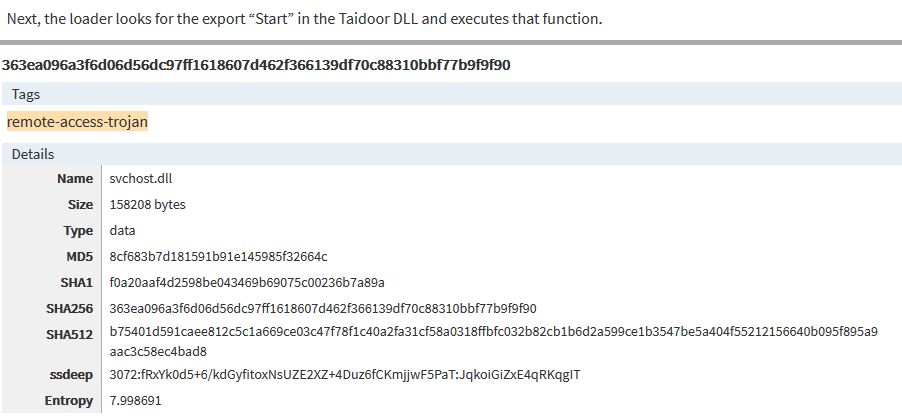
The three agencies explain that the latest malware, called Taidoor, has 32 and 64-bit versions and is typically installed as DLL (Dynamic Link Library) on victims’ computers. Two other files are in this DLL.
According to the information shared in the joint alert, the first file is a service loader. Its role is to decrypt the second file, which is the actual Remote Access Trojan (RAT) and executes it in memory.
The malicious actors can use the Taidoor RAT to remotely access infected systems and exfiltrate data or insert other malware.
The FBI claims that Taidoor is typically installed alongside proxy servers to mask the malware operator’s real point of origin.
Although the joint alert introduces Taidoor as a new threat that poses a new challenge to the cyber security community, the US Cyber Command said in a tweet post that the malware has been around for at least 12 years, secretly embedded in victim networks since 2008.
Following the joint alert publication, Florian Roth, a Nextron Systems malware researcher, said he has come across Taidoor samples previously, some of which date from March 2019 but were called Taurus RAT.
The three agencies have released a collaborative malware analysis report (MAR) with recommended mitigation strategies and suggested response steps for organizations who want to improve identification, avoid infections or are already compromised and need malware removal assistance.
Four samples from Taidoor have been uploaded by US Cyber Command on VirusTotal’s portal from where the files can be downloaded for further review and analysis.

Leave a Reply