aBSunset
This particular malware category is highly dangerous and problematic and every user who has issues with it must be well acquainted with the different capabilities of Trojan viruses which is why we have written this article – to provide our readers with useful and important information regarding aBSunset, one of the latest representatives of the Trojan Horse malware group.
The aBSunset Virus
In the next lines, you will be able to learn more about this nasty piece of malware so that you know exactly how to deal with it should it get inside your PC system. Be sure to carefully read all the following information and then, in case aBSunset Virus has already attacked your computer, head down to the removal guide for the virus. Use the guide to eliminate the threat so that it won’t be able to cause any harm to your PC and to your virtual security. As we already said, Trojans truly are one of the nastiest forms of malware and it is crucial that users take the necessary precautions on time so that the potential damage that such a virus may cause could be avoided.
Trojan Horse infections – why are they so difficult to handle?
A typical trait of most malicious programs that belong to this malware type is their stealthiness and their ability to “keep a low profile” while simultaneously carrying out their illegal and insidious tasks within the targeted machine. A Trojan Horse is an unseen threat that many users fail to notice and detect on time which could lead to all kinds of unpleasant and harmful consequences. First of all, when a Trojan infection occurs, it typically happens without any visible symptoms. The lack of red flags that could help the user recognize the infection oftentimes continues throughout the duration of the contamination period meaning that unless there’s a good and reliable antivirus software on the computer, the chances of spotting the virus would be rather low.
The aBSunset Virus
A virus such as aBSunset might actually be capable of executing different tasks once inside the targeted machine. Those tasks might include infecting your PC with other viruses (such as Ransomware), harming the system through corruption/deletion of important OS data and Registry keys, stealing personal/professional data, monitoring the user’s activity while they are on the PC, stealing money from the victim’s online banking accounts, etc.
Bear in mind that having a security program on your PC doesn’t guarantee the safety of the machine. Antivirus programs are useful and helpful but they are not flawless. Even if you have the best antivirus software on your computer, it might still fail to detect a certain malicious program, especially if the virus is a new one (such as aBSunset). That is why it is always better to ensure that no such threats come near your PC in the first place. The good news here is that in most of the cases you can actually provide your PC with some adequate protection as long as you remember to keep away from any potential sources of Trojan Horse viruses such as aBSunset Virus. Note that even the nastiest of viruses typically need you to make some kind of a mistake so that the infection could actually take place inside your PC. Such a mistake could involve the opening of an infected spam message attachment, the running of a compromised software installer, the clicking on a misleading online advert or something similar. Hackers are really good at sneaking their viruses inside users’ computers by disguising the malware as seemingly harmless content. Still, though, a user who is vigilant and cautious enough should be able to recognize and identify potentially hazardous content and stay away from it in order to keep their PC safe. Therefore, make sure that you too remain careful while surfing the Internet and avoid interaction with anything that might not be reliable or safe. If anything you come across on the World Wide Web doesn’t seem to be trustworthy, it is probably better to simply keep your distance.
Some Trojans create botnets of infected machines and use all of the infiltrated devices to conduct tasks such as crypto-mining, Distributed Denial of Service (DDoS) attacks, spam e-mail campaigns and others. All in all, Trojans are a very versatile group of viruses and predicting what such a virus might be used for in each separate case might not always be possible. Nevertheless, regardless of what aBSunset might be seeking to accomplish in your particular case, you should certainly not wait to find out first hand. Instead, as we already said, it is advisable if you use the guide provided on this page and eliminate the threat before it has managed to cause some major damage to your machine and/or to your virtual privacy.
SUMMARY:
| Name | aBSunset |
| Type | Trojan |
| Detection Tool |
Remove aBSunset Virus
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
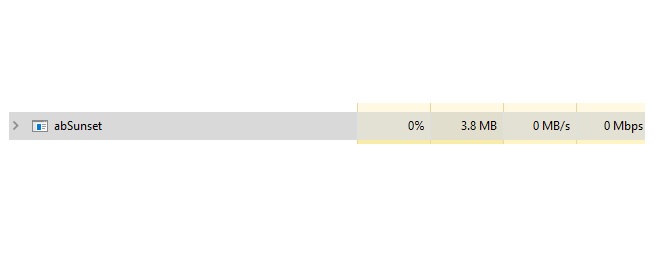
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning. You can find the removal guide here.
For mobile devices refer to these guides instead: Android, iPhone

Leave a Comment