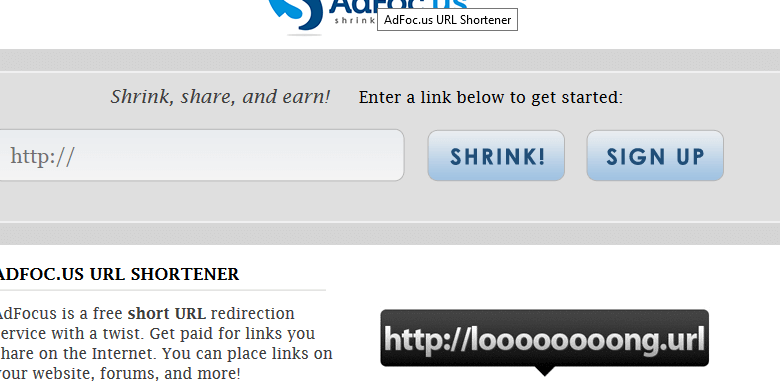
Adfoc.us
You might have come across Adfoc.us most likely because your computer has been suffering from too many and too aggressive ads and browser redirects, which are constantly appearing. If so, your problem’s source is an Browser Hijacker-like program, most probably Adfoc.us.
The Adfoc.us virus will display pop up ads and messages
On the one hand, you should not panic – Adfoc.us is not an actual virus in any way and cannot harm your computer on its own. On the other hand, it may appear particularly irritating and may redirect you to possibly dangerous websites and software.
The following information will make the entire picture clearer to you as it explains the typical features, methods of distribution and ways of removal of Adfoc.us “virus”.
The Adfoc.us Virus
At first the Adfoc.us Virus originated as a direct-marketing-campaign tool. Its characteristics fully match the typical behaviour of Browser Hijacker. The advertisement campaigns of the Adfoc.us Virus generates might constantly renew themselves because this Browser Hijacker version has been built according to the pay-per-click system. In other words- the bigger the number of the displayed and clicked-on ads gets, the bigger the amount of the generated profits is.
Another typical feature of Adfoc.us is that it can predict and automatically fit the pop-up flow to your tastes and preferences.
If Browser Hijacker doesn’t ring a bell
Browser Hijacker is derived from the term “advertisement software”. Apparently, this software represents the programs that generate probably unwanted ads in various forms (pop-ups/banners/pop-unders/newly-opened browser tabs and windows).
Nonetheless, Browser Hijackers are criticized because they may use quite intrusive in the way they disturb your browsing process and at times rather shady methods of distribution. However, please, don’t get panicked! Browser Hijacker is not similar to malware because it cannot self-replicate, compromise private data or take control of the computer system. What’s more, you can be sure that Browser Hijacker-like programs will not demand money as ransomware typically does. They just need your attention and time because they are paid to promote services and products.
How do we get to know this buddy?
It is important to mention the fact that generating ads is a completely legitimate practice, that is very profitable for its owners. As a result, as you might expect, the chance to get to know Browser Hijacker personally is very high. Here we are going to discuss the most common distribution methods that are exploited by the Browser Hijacker’s developers.
To begin with, those distribution methods may greatly vary. That’s why we will focus on the ones that are most often used. Among the usual suspects are software bundles. Usually developers may tend to put Browser Hijacker-based apps in the shareware bundles, so that they can generate some additional profits. Nonetheless, it is essential to know that not all Browser Hijacker depends on illegitimate practices. Many of the Browser Hijacker-developing and distributing companies are absolutely legal. In most of the cases this ad-producing software might just seem extremely disturbing. However, some of the Browser Hijacker programmers could be indeed less scrupulous and could be likely to program their Browser Hijacker-based products to track your browsing habits search requests online. This is how this type of software is able to show mainly advertisements related to your recent searches and personal tastes. Another possible threat that may come from Browser Hijacker is that the generated pop-ups and banners could redirect you to webpages with probably dangerous content like, for example – Ransomware.
Another possible way a user may get infected with Browser Hijacker is by visiting an already infected page in the web. One more option of catching such irritating software is by using a torrent website that is not trustworthy.
Be cautious because Browser Hijacker is able to integrate itself into all the most famous browsers (Firefox, Chrome, Opera and Internet Explorer).
Prioritizing prevention
It is essential that you always make prevention a priority. An already occurred problem may be harder to be solved than to be simply avoided. Be careful and always strive to keep your system and yourself out of trouble. Some of the advice that comes in handy is to purchase reliable anti-virus software with a good reputation and trustworthy image, to always enable your firewalls and pop-up blocking tools. Another important aspect of being fully safe is to learn how to properly install free software. The best possible way is to always choose the “Manual/Customized” feature of the installer. Also, it will be necessary for you to carefully read all the End-User Agreements and menus to be better aware of the programs you integrate into your PC. If you closely follow our prevention tips, you will be out of trouble.
What to do in case of an infection with this Browser Hijacker
Unfortunately, your system has have already been infected with Adfoc.us. Then, you will have to be careful. Always try to avoid clicking on any place in the pop-ups and banners, different from the Adfoc.us. You should only try to close them down. You may find that some of them can be removed easily and no professional help will be required. Nevertheless, others could require more profound actions to be performed. In both cases you should really try to stay calm. The removal guide below has been prepared to assist you in dealing with your problem in a simple and efficient way.
SUMMARY:
| Name | Adfoc.us |
| Type | Browser Hijacker |
| Detection Tool |
Remove Adfoc.us Virus
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.
For mobile devices refer to these guides instead: Android , iPhone

Leave a Comment